News, entertainment sites hotbed for serving malware ads, says report


Hackers and malicious actors are increasingly targeting online ad networks as a means to infect users, a new report says.
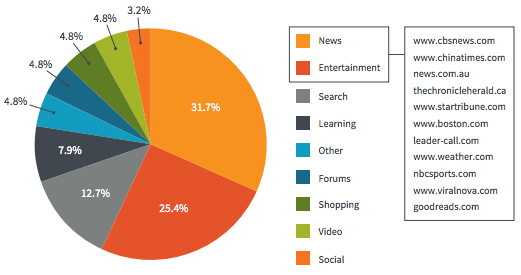
A new report by Bromium, a Cupertino, Calif.-based firm with a commercial stake in the security space and a research unit, says more than half of these "malvertising" attacks originate from news and entertainment sites that inadvertently display infected online ads. Bromium has created technology called micro-virtualization, which is designed to sandbox various threats and malicious code. The company is venture backed and counts Andreessen Horowitz and Intel Capital among its investors.
NBCSports.com, Weather.com, and CBSNews.com (ZDNet is also owned by CBS) were named in the report as "attractive" targets for hackers.
"In a classic malvertisement attack, the attackers like to target as many users as possible," Rahul Kashyap, Bromium's chief security architect, told ZDNet in an email.
That is one of the main reasons why news and entertainment and news -- among the most visited websites online -- are big targets for hackers and malicious actors.
Kashyap, a security industry veteran, explained how hackers were able to trick ad networks into accepting malware.
"In the real world, attackers buy ads from online advertising companies and insert malware in these ads," he said. "This is done typically by leveraging an exploit kit that delivers the malware payload."
Kashyap explained that many of the exploit kits are able to "profile" its victims, such as which vulnerable browsers and plugins are installed, in order to select the right payload to exploit a flaw.
"After successful exploitation, the malware gets installed on the victim's machine," he said.
But it's not entirely the fault of the news sites in question, however. Kashyap said in many cases they "cannot do much" to solve problems with third-party ad networks, except limit third-party code to run on their sites. In many cases, however, display ads -- which include text, images, and Flash-based video content -- allow websites to subsidize their costs, providing news or other content for free, making it financially difficult to roll back.
MORE ON RANSOMWARE
The report said the volume of ads is so high it's almost impossible to verify every ad, but Kashyap said ad networks should do more.
"Ad networks have a huge responsibility here, which is unfortunately unfulfilled," said Kashyap.
In an emailed statement Tuesday, a spokesperson for CBS Interactive said: "We have not seen the report and therefore cannot speak to its accuracy, research methods or specific findings. Ad networks, not individual web properties, are at the center of this issue. However, the detection and immediate remediation of malware is a shared responsibility."
Ed Kozek, senior vice president of product and engineering at The Weather Company, said in emailed remarks: "I don't know the specifics of this particular study as it hasn't been made available to us. However, we do work with a third-party malware detection company that scans the ads on our sites thousands of times a day. If they flag anything as questionable, we immediately investigate and take action if needed."
Emails to representatives of Boston.com and NBC Universal went unanswered at the time of writing.