Online brand-jacking increasing
With the evolving sophistication of online scammers' understanding of social engineering and trust building online, the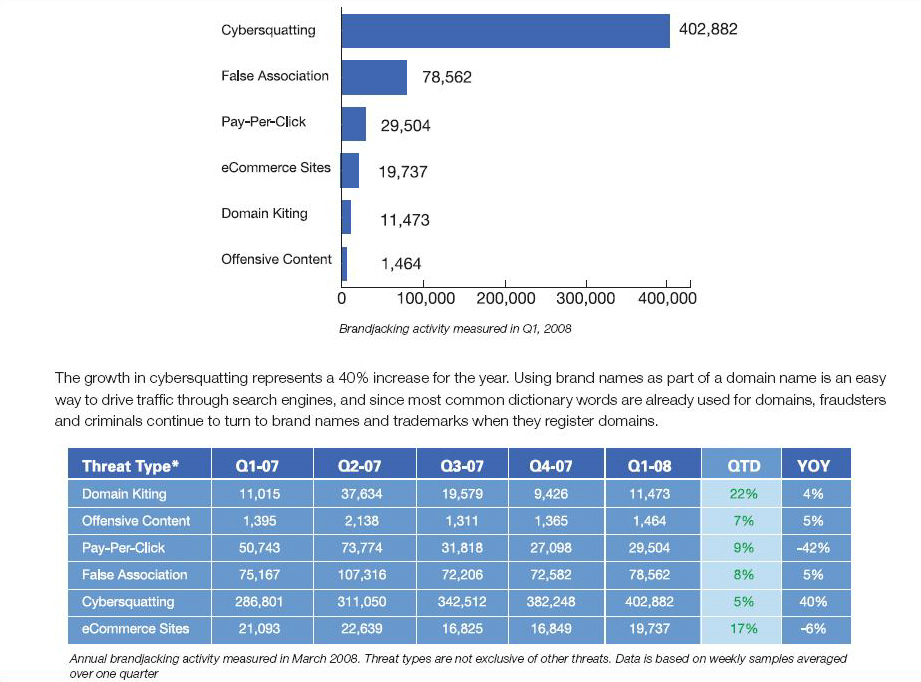
MarkMonitor's recently released Brandjacking Index 2008 indicates that brand-jacking is increasing, with online scammers actively abusing a brand's reputation in order to build more legitimacy into their campaigns, by taking advantage of the brand's trusted reputation. Some of the highlights in the report :
- On average, almost half a million instances of brand abuse were measured each week including 402,882 accounts of cybersquatting, the registration of domain names containing a brand, slogan or trademark to which the registrant has no right. Instances of cybersquatting rose 40 percent in the first quarter of 2008
- Media brands continue to be the most targeted by brandjackers with over 40,000 instances of abuse in Q1 2008. Abuse against automotive brands increased by 99 percent since Q1 2007 to 25,792
- Pay-per-click abuse continued to remain low in Q1 and is down 42 percent for the year. This form of brandjacking has experienced almost zero growth since Q2 2007. Vigilance by brandholders, regulatory changes by ICANN and policy changes by major search engines have driven the declines
- While brand abusers can be located anywhere in the world, their top countries for Web site hosting remained consistent. The U.S. is home to 66 percent of Web sites that host brand abuse. Germany hosts 7 percent, followed by the United Kingdom at 6 percent. Canada hosts 4 percent
As you can see cybersquatting to visually social engineer the visitor into thinking the site's legitimate, false association with industry leading brands into the consumer protection business, as well as the phishing, represent the largest proportion of brandjacking techniques used. However, these are not mutually exclusive, and in reality often intersect with one another to provide a scammer with a multi-layered brandjacking capabilities. Let's discuss the most prevalent brandjacking tactics in details.
- Cybersquatting
The rise of cybersquatting can be explained with the overall availability of automatic domain registration software, which in a combination with automated approach to verify the availability of the domain and purchase it without the brand owner proactively monitoring for such abuse, is what's driving this increase. Some of the cybersquatted domains are in fact so creative, that would successfully spoof a brand's web application structure in the domain name, an example of which you can see in two cybersquatted domain portfolios impersonating PayPal and Ebay. In March, 2008, I assessed a domains portfolio registered by a single company known for its misleading business practices, that managed to brandjack security software brands such as Pandasecurity, McAfee next to Adobe's Acrobat Reader, with trustworthy looking domain names. Upon notification of the affected parties, the company expanded its portfolio, this time cybersquatting Symantec's Norton Antivirus. All of these examples indicate a certain degree of centralization, namely, known companies and individuals continue cybersquatting some of the world's most popular brands, whose domains usually remain online for longer than they should be due to the brand's lack of proactive response to this tactic.
- False Association
You would purchase an item from a site that's been recommended by half the industry's leading anti-hacker monitoring services, and has all those "false feeling of safety and privacy" banners aiming to increase the trust of the potential buyer? The only difference between a rogue software site and the original one for instance, is that you would be able to click on any of these banners on the legitimate site and receive a response, whereas, there are no external links to click on at the bogus sites. This is where false association comes into play, and it's something I've been monitoring for a while now. Basically, each and every rogue security software is quoting comments from leading industry benchmarkers on how well it performs, and how many stars it's been awarded by a known service that tests and reviews software. And due to the overall availability of web site templates for rogue security software, on their way to scam as many people as possible, scammers often forget the take the time and effort to modify the template, ending up in amusing situations where the images promote a fake software while the text is promoting the old software included in the template. Knowing Dalai Lama doesn't mean Dalai Lama knows you, however, from a psychological perspective this is a very successful tactic that scammers would continue using.
- Phishing
Phishing is prone to increase given the direct scamming approach it utilizes in order to reach everyone, everywhere, in a combination with ongoing development of do-it-yourself phishing kits that I've assessed in a previous post. But the statistics released from the majority can be greatly engineered in respect to the changing tactics phishers take advantage of, such as hosting the phishing pages on breached sites courtesy of the access provided by web site defacers, and SQL injecting them on vulnerable sites, with the most recent case where the U.K's Crime Reduction Portal was hosting a phishing page.
Here are some of highlights on phishing discussed in the report :
- The number of organizations phished in Q1 remained steady over Q4 2007 at 408, representing an 8 percent rise for the year. The number of new organizations targeted by phishers decreased to 102 in Q1 2008
- 14 organizations account for 90 percent of all phishing URLs. Eight of these organizations are based in the U.S., and six are in the United Kingdom. 11 are financial institutions
- Phishing attacks against auction brands comprise 60 percent of all phish attacks in Q1 2008
- Phishing attacks against retail/service brands declined by 85 percent this quarter returning to Q1 2007 levels. This trend is evidence of the seasonal rise in phishing attacks against retail brands during the pre-holiday season
- 34 percent of phishing sites were hosted in the U.S. in Q1 2008 compared to 21 percent in Q4 2007
- Phishing URLs continued to decline in Q1 2008, evidence of continued influence from the Rock Phish Gang
A company wanting to protect its customers should either build an in-house capacity to monitor any brandjacking attempts, or outsource the process to vendors who have already build the capabilities to monitor, detect and respond to such attacks before a customer gets tricked. As for the customers, sometimes the bargain deal may be worst deal you've ever made if fall victim into a scammer targeting bargain hunters with propositions they simply cannot resist - but should.