Report: malicious PDF files becoming the attack vector of choice
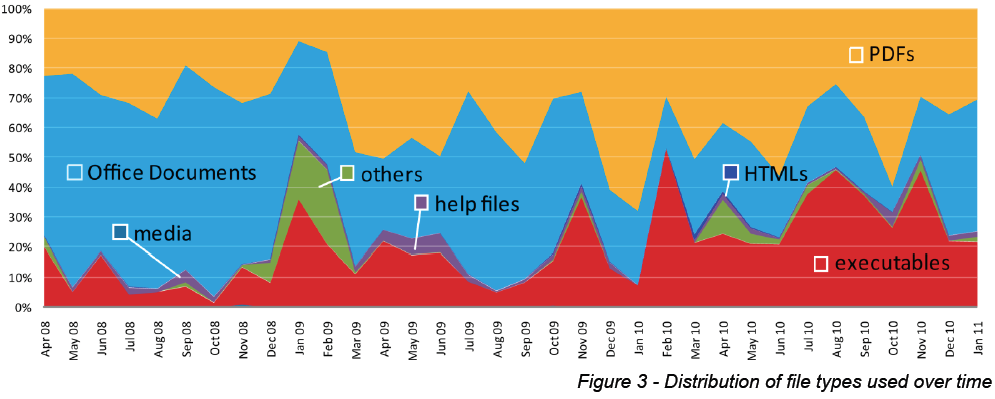
According to a newly released report by Symantec's MessageLabs, malicious PDF files outpace the distribution of related malicious attachments used in targeted attacks, and currently represent the attack vector of choice for malicious attackers compared to media, help files, HTMLs and executables.
The report also notes a slight increase in the distribution of executable files, a rather surprising trend given the fact that spam and email filters will definitely pick them up.
PDFs now account for a larger proportion of document file types used as attack vectors. However, it should be noted that office-based file formats are still a popular and effective choice used in some targeted attacks. In 2009, approximately 52.6% of targeted attacks used PDF exploits, compared with 65.0% in 2010, an increase of 12.4%. Despite a recent downturn in the last three months, if this trend were to continue at the same rate it has for the last year, the chart in figure 2 shows that by mid-2011, 76% of targeted malware could be used for PDF-based attacks.
PDF-based malware campaigns are here to stay, though:
"PDF-based targeted attacks are here to stay, and are predicted to worsen as malware authors continue to innovate in the delivery, construction and obfuscation of the techniques necessary for this type of malware," said MessageLabs Intelligence Senior Analyst, Paul Wood.
Are cybercriminals picky? Not necessarily as it's entirely based on the campaign in question. In this case, they appear to be interested in bypassing spam and email filters by distributing a ubiquitous filetype that's often allow to pass through them in the first place.
Email attachments combined with social engineering tactics, are among the many attack vectors, cybercriminals take advantage of. Next to email attachments, the use of web malware exploitation kits is growing, with the majority of publicly obtainable data indicating that they continue relying on outdated and already patched vulnerabilities for successful exploitation.
See also: