Verizon records vacuumed up by NSA under 'top secret' Patriot Act order

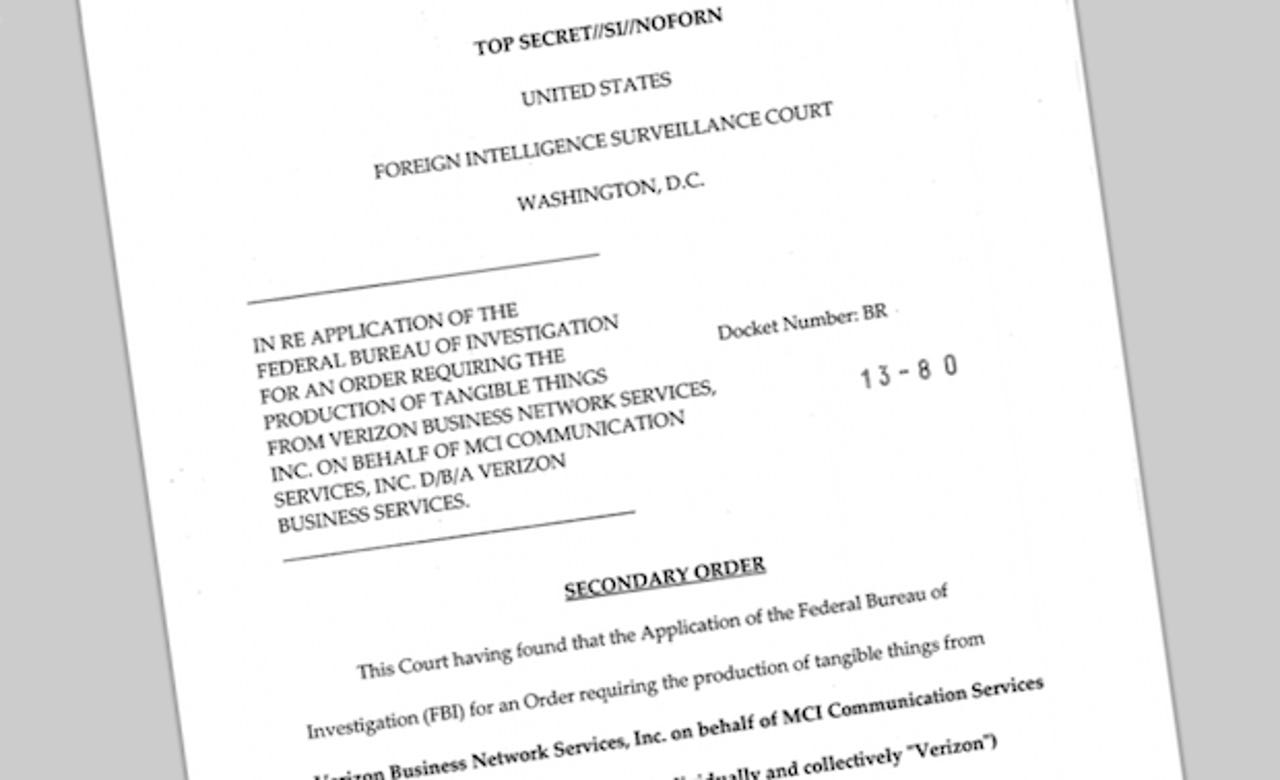
A "top secret" order issued by a little-known U.S. court isn't so secret anymore, after The Guardian published it on Wednesday evening.
The London, U.K.-based newspaper revealed exclusively that the U.S. National Security Agency (NSA) has and continues to vacuum up millions of Verizon customer details, including information on phone calls both within the U.S. and between the U.S. and other countries.
Under the order, Verizon is ordered on an "ongoing, daily basis" to hand the NSA the information on all of the call data in its systems.
As of the company's 2012 fiscal fourth quarter, Verizon had 115.78 million cellular subscribers. That's a good chunk of Verizon customers, but still excludes a larger number of overall customers affected by this court order.
The document states that under the Foreign Intelligence Surveillance Act (FISA) court, known as the FISC, the order was granted to the U.S. Federal Bureau of Investigation (FBI) on April 25. The order expires on July 19 — around six weeks from now.
The three-month order gives the U.S. government agency an endless supply of data for the period.
The data that is being collected on Verizon customers — including cellular and landline customers — includes all call details or "metadata" relating to calls created by Verizon between the U.S. and abroad, or within the U.S., including local calls. This metadata, the publication reported, links into a 2005 ruling that determined that cell site location data is also considered as being under this scope.
Location data of Verizon customers, therefore, is in the NSA's hands.
This includes routing data, such as the originating and recipient phone number; the IMEI unique phone identifier; the IMSI number used to identify calls on cellular networks; trunk identifiers; phone calling cards; and the time, date, and duration of the call.
Verizon customers that are outside of the U.S. and making calls to non-U.S. residents are exempt from the secretive court order. Names, addresses, and financial data are also not collected. That said, it's not exactly difficult for the NSA, in conjunction with the FBI, to work out who someone is from that very specific data.
This comes only a month after former FBI counter-terrorism agent Tim Clemente told CNN that the U.S. government can acquire personal and sensitive data, and that it is "captured as we speak, whether we know it or like it or not."
It's not clear whether other cell networks, such as AT&T, T-Mobile, and Sprint, have been targeted with similar or identical warrants. Key "gagging order" provisions mean that the FISC court order does not allow anyone, including the aforementioned, to disclose the order to anyone.
It relives similar orders under the Bush administration, in which the NSA was ordered to wiretap without warrant U.S. citizens in a mass domestic surveillance program. An AT&T whistleblower disclosed that the cell company was "complicit" in the U.S. government's monitoring of phone calls, Web activity — including history and email details — and text messaging data of U.S. residents.
The wiretapping stopped in January 2007. In 2008, the FISA Amendments Act was introduced.
For the first time under Obama's time in office, the document proves that millions of U.S. citizens and residents are under surveillance by the government — whether they are even suspected of committing a crime or not.
The interesting factor here is that the FISC can order such widespread snooping under the condition that U.S. citizens could be communicating with foreign citizens — which, under FISA, such snooping is authorized. But the key factor here is "residents," and not "citizens." FISA also authorizes widespread snooping on "persons" within the U.S., as long as they are legally allowed to be there.
It was, after all, designed and brought into law in 1978, at the height of the Cold War, where spying was widespread across the U.S., Europe, and Russia.
But questions remain over why. Nobody seems to know exactly why Verizon was targeted with a "top secret" court order.
Under Section 215 of the Patriot Act, first brought out in October 2001, just a month after the devastating terrorist attack in New York City, "business records" can be acquired by the U.S. intelligence agencies — such as the NSA and the FBI — in vast swathes with a single warrant.
It also allows any "tangible thing" to be acquired by the government, such as books, receipts, and even privately held computer databases, such as in this case.
Last year, Senator Ron Wyden (D-OR) and Senator Mark Udall (D-CO) revealed, while still under U.S. secrecy laws: "We're getting to a gap between what the public thinks the law says and what the American government secretly thinks the law says."
They specifically warned about the "business provisions" in the Patriot Act that allow the U.S. government to acquire vast amounts of data with a single warrant, including medical records, so long as it pertains to an intelligence investigation.
The secret interpretation of the "business records" provision by the U.S. Justice Department led the two senators to speak, albeit within the bounds of U.S. secrecy laws, to disclose that there was a "secret interpretation."
Section 215 has already been used to obtain driving license, credit card, car, and apartment rental records. Such records are not within the parameters of the Fourth Amendment, which protects residents from "unreasonable" searches, because arguably they are not considered a "search."
The Patriot Act provision also means that such an order must be approved by the secret FISC, and can be so long as the data sought is relevant to a terrorism investigation. Such investigations do not require much, however.
Basically, Verizon couldn't do anything about this even if it wanted to. It's not allowed to disclose anything about this order, and naturally declined to comment to The Guardian.