X Font Server flaw hits Sun Solaris hard

According to an alert from iDefense, the flaw exists in the way Solaris implements the X Font Server (xfs), which is used to handle font rendering on X11 (X Window System).
The vulnerability, fixed in XFS version 1.0.5, affects multiple vendors but current versions of Solaris are hardest hit because the XFS service is turned on by default and listens on TCP port 7100.
"These vulnerabilities are remotely exploitable [on Solaris]," iDefense warned.
In the absence of a patch from Sun Microsystems, Solaris users are urged to stop XFS from listening remotely by disabling it via the service manager.
[SEE: Sun rushes out patch for Solaris Telnet exploit ]
Exploit code for this vulnerability has been released by Immunity, Inc., a penetration testing firm that sells access to exploits and vulnerabilities. "Good default anonymous remotes don't come out every day. Solaris is still all over the place so this sort of thing is quite interesting," said Immunity researcher Dave Aitel.
On modern Linux systems, these vulnerabilities are only locally exploitable since the server is configured to listen on a UNIX socket only.
Technical details of the X Font Server vulnerabilities:
An integer overflow vulnerability exists within the handlers for the QueryXBitmaps and QueryXExtents protocol requests. Both requests result in a call to the build_range() function. This function takes a 32bit integer from the request, and uses it in an arithmetic operation that calculates the size of a dynamic buffer. This calculation can overflow, which leads to an improperly sized memory allocation. This results in a heap overflow.
Additionally, a heap corruption vulnerability exists within the handlers for the QueryXBitmaps and QueryXExtents protocol requests. Both requests result in a call to the swap_char2b() function. This function takes a 32bit integer from the request, and uses it as the number of bytes to swap in the request buffer. This allows an attacker to swap an arbitrary number of bytes on the heap.
Sun Microsystems has taken baby steps recently to improve its security response process. This month, for the first time, the company provided advance notification of security updates for Java SE.
Sun said this is the first step towards the simultaneous release of security fixes across all supported Java SE release families. "Sun expects to fully synchronize the release of security fixes across all supported releases, including J2SE 1.3.1 in 2008," the company said on its security blog.
Sun has been heavily criticized in the past for the way Java patches are released.
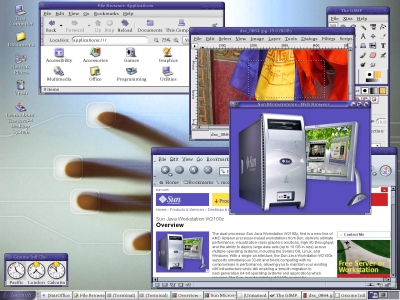
* Image via Wikipedia article on Sun Solaris.