Rootkit called Carrier IQ discovered phoning home with user data

Remember Locationgate? Well, that might be nothing compared to a rootkit that's been discovered pre-installed on some Android handsets.
[The Locationgate scandal erupted in April 2011 when a hidden file called “consolidated.db” (containing a database of Wi-Fi hotspots and cell towers around your phone's location) was discovered unencrypted in iOS 4.]
Well, at least consolidated.db didn't phone home and report your whereabouts to the mothership -- which is what appears to be happening on millions of Android handsets.
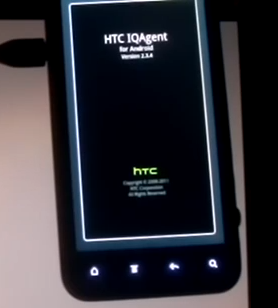
In this video, 25-year-old security researcher Trevor Eckhart of Connecticut shows how two nefarious apps (HTC IQAgent and IQRD) are discovered pre-loaded and running on his HTC smartphone.
Eckhart demonstrates how the surreptitious apps log text messages, encrypted web searches -- and just about everything else -- and send the data to Carrier IQ’s servers.
Worse, Wired reports that the rootkit can't be turned off without rooting the phone and replacing the operating system. "And even if you stop paying for wireless service from your carrier and decide to just use Wi-Fi, your device still reports to Carrier IQ."
Luckily, Logging Checker (main site) is an Android app by TrevE that tests to see if your device is among the afflicted. Here's a screenshot:
Update: I ran Loggig Checker on my Droid RAZR running on Verizon Wireless and all the tests came up negative. It appears that at least the RAZR on VZW doesn't have it.