Microsoft releases out-of-band security update to plug .NET hole

No one in Redmond is popping champagne to celebrate the 100th and last Microsoft security update of the year.
MS11-100, released today, is a rare out-of-band security update—one delivered on a Thursday, several weeks ahead of the next regularly scheduled Patch Tuesday release.
The bulletin, described in this blog post, is rated Critical for a Denial of Service (DoS) vulnerability and specifically praises the ASP.NET team for its "holiday heroics":
Yesterday evening, we published an Advanced Notification alerting customers to a new out-of-band security update planned to be released today. The notification listed the update as addressing a Critical Elevation-of-Privilege vulnerability, leading to several questions from customers who expected the bulletin addressing a Denial-of-Service vulnerability to be rated Important.
Before hearing about this vulnerability, we had planned to release a .NET security update addressing three vulnerabilities, one of which was a Critical elevation-of-privilege vulnerability. When this vulnerability notification arrived a few weeks ago, the ASP.NET team included the fix into the update already being developed and tested. So the bulletin today addresses four vulnerabilities, one of which is the ASP.NET Denial-of-Service vulnerability presented yesterday. You can read more about the other vulnerabilities in the Security Bulletin and we also invite you to join us for a webcast at 1:00 p.m. PST today (Dec 29) where we will describe the vulnerabilities and answer your questions live “on the air.” You can sign up for the webcast here.
The four patched vulnerabilities affect the Microsoft .NET Framework on every supported version of Windows, including Windows XP SP3, Windows Vista, Windows 7, Windows Server 2003, and Windows Server 2008 and 2008 R2. Exploits against unpatched systems could allow an attacker to "take any action in the context of an existing account on the ASP.NET site, including executing arbitrary commands."
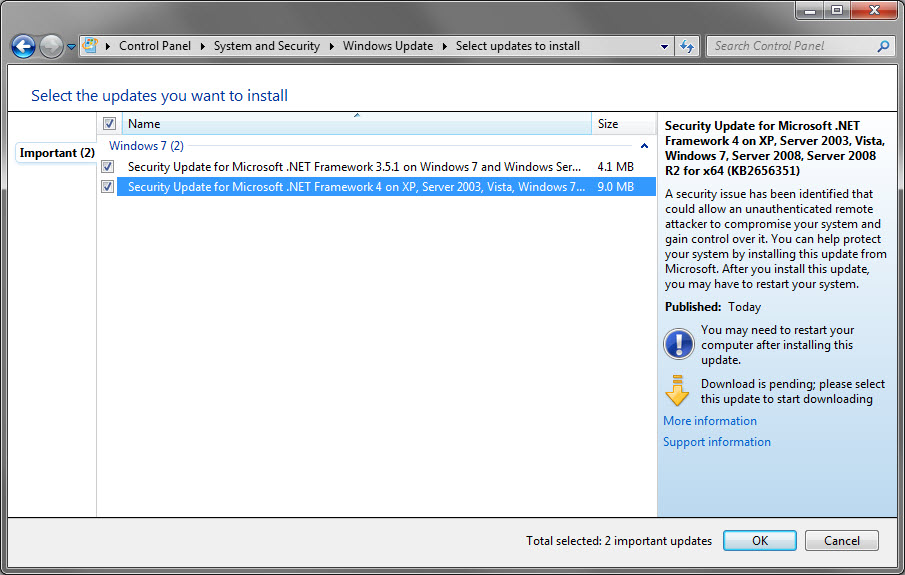
The update will be delivered without user intervention to machines that have Automatic Updates turned on. If you prefer not to wait, open Windows Update and check for updates manually. Here's what it looks like.
Typically, an out-of-band update indicates that the risk of "in the wild" exploits is high, so this update demands immediate attention.