Windows 7 UAC flaw: "Pandora's box of all vulnerabilities"

The background
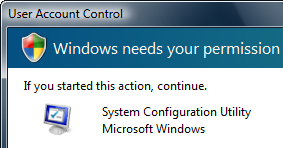
UAC, or User Account Controls, made its first appearance in Windows Vista as a precautionary measure to ensure the user doesn't modify something which would change a setting which would effect the overall stability or usage of the computer. It also served as a preventative control to make sure programs and applications wouldn't run without your express permission, or an application changing your settings without you being fully aware of it. This came in the form of an annoying popup box, I'm sure you won't have any problem in remembering:Standard users would be able to modify "user settings", such as the wallpaper, screensavers, how things look on screen and suchlike. If standard users wanted to modify "global settings", settings which affected the experience of other users such as screen resolution or installing applications, they would be prompted to do so by UAC. To enable standard users to modify global settings, they would need to be "elevated" to temporary administrator status to do this. Afterwards, the user would revert back to standard user status.
Turning UAC off in Vista had a bit of a trick behind it. It wasn't a case of simply ticking a box, rather having to go through a hidden Windows utility and launching a command process; it wasn't deemed necessary for an ordinary end-user to disable it.
However, through much complaining, hissy fits and multiple workarounds being circumvented across the web, Microsoft buckled and tamed down UAC in an effort to be less intrusive, less annoying but more secure.
Instead of taming the system, they've blown its bloody head off.
The vulnerability
In Windows 7, the settings have changed for UAC, allowing the system to be more malleable and flexible for users. Certain applications which are digitally signed are fast-tracked through UAC by default to reduce the unnecessary user interaction. The vulnerability shows itself when this third-party application calls on malicious code "by proxy" through an existing Windows application, which never invokes the UAC prompt.To put it simply, through application piggybacking, it allows malware to be automatically elevated to administrator user status which in turn allows it full, unrestricted access to the computer and global settings.
Long Zheng, Windows enthusiast, evangelist, student and campaigner of this flaw, spoke to me earlier today. He has written many times on this, along with his friend and colleague Rafael Rivera, who created a proof-of-concept behind this flaw. This video, available on Zheng's website, details how the proof-of-concept works in a Windows 7 environment.
The consequences
Microsoft have since stated they will not be fixing this flaw as it is "by design", and Zheng's reply:"I'm not saying this is the end of the line for Windows 7, it's an amazing operating system. But for Microsoft to simply ignore this seems irresponsible to me. There are so many people I'd like to evangelise Windows 7 to once it ships, and I'd hate this to be one thing I'd also have to mention."
More details of how malware can silently elevate with Windows 7's default UAC policy is available in a post he wrote earlier this year.
It would be far easier to explain what the consequences weren't. If the US defence systems were running Windows 7, at this rate, all-out nuclear war could be a possibility if someone was determined enough and the end-user was unlucky enough.
The fact of the matter is, this vulnerability opens up Windows 7 like a cracked nut; exposing the possibility of a malware attack instigated unknowingly by the end user at any given time. But for the reasoning behind Microsoft's decision not to fix this unholy flaw not only shows their arrogance, but also their inability to listen to some of the most influential and experienced people on the web.
[poll id="24"]