With Azure Active Directory, Microsoft wants to be the meta ID hub

Microsoft isn't just reimagining Windows and reimaginging tablets. It's also reimagining Active Directory in the form of the recently (officially) unveiled Windows Azure Active Directory (WAAD).
In a June 19 blog post that largely got lost among the Microsoft Surface shuffle last week, Microsoft Technical Fellow John Shewchuk delivered the promised Part 2 of Microsoft's overall vision for WAAD.
WAAD is the cloud complement to Microsoft's Active Directory directory service. Here's more about Microsoft's thinking about WAAD, based on the first of Shewchuk's posts. It already is being used by Office 365, Windows InTune and Windows Azure. Microsoft's goal is to convince non-Microsoft businesses and product teams to use WAAD, too.
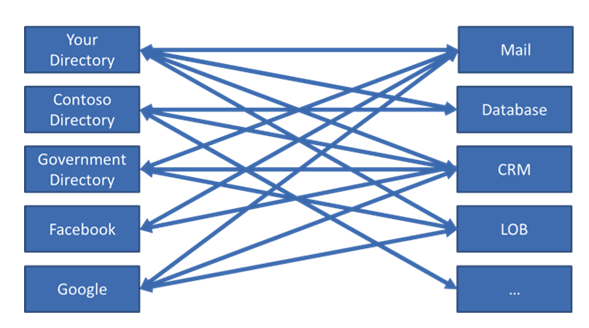
This is how the identity-management world looks today, in the WAAD team's view:
And this is the ideal and brave new world they want to see, going forward.
How is Microsoft proposing to go from A to B? Shewchuk explains:
"(W)e currently support WS-Federation to enable SSO (single sign-on) between the application and the directory. We also see the SAML/P, OAuth 2, and OpenID Connect protocols as a strategic focus and will be increasing support for these protocols. Because integration with applications occurs over standard protocols, this SSO capability is available to any application running on any technology stack...
"Because Windows Azure Active Directory integrates with both consumer-focused and enterprise-focused identity providers, developers can easily support many new scenarios—such as managing customer or partner access to information—all using the same Active Directory–based approach that traditionally has been used for organizations’ internal identities."
Microsoft execs are sharing more information and conducting sessions about WAAD at TechEd Europe, which kicks off on June 25 in Amsterdam.
Microsoft announced the developer preview for WAAD on June 7. This preview includes two capabilities that are not currently in WAAD as it exists today, Shewchuk noted. The two: 1. The ability to connect and use information in the directory through a REST interface; 2. The ability for third-party developers to connect to the SSO the way Microsoft's own apps do.
The preview also will "include support for integration with consumer-oriented Internet identity providers such as Google and Facebook, and the ability to support Active Directory in deployments that span the cloud and enterprise through synchronization technology," he blogged.
Shewchuk said the WAAD developer preview should be available "soon."
Update: In spite of what the Microsoft diagram seems to indicate, the Softies say they are not positioning WAAD as a hub. A new and improved diagram is in the works that will make it clearer that in Microsoft's updated identity vision "there is no hub; there is no center."