How to remove the ICPP Copyright Violation Alert ransomware
Who would have thought that on your way to remove a ransomware scam that affected your PC, you would be one day pirating the application that was originally using a "copyright violation alert" theme, as a spreading technique?
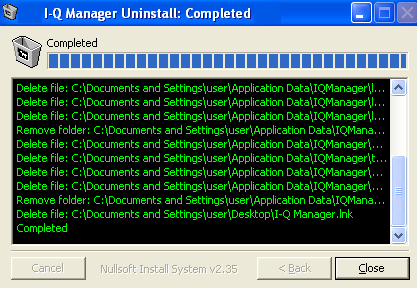
What's the best way of removing it? A working license code that completely uninstalls the ransomware, remains the most effective post-infection approach.
What would be the best, and most effective way to get rid of the ransomware once and for all, excluding the use of freeware tools that detect and remove it?
As always, prevention is better than the cure.