Malware and spam attacks exploiting Picasa and ImageShack
In the wake of the recent malvertising attacks where malicious flash ads were appearing at trusted web sites, evidence from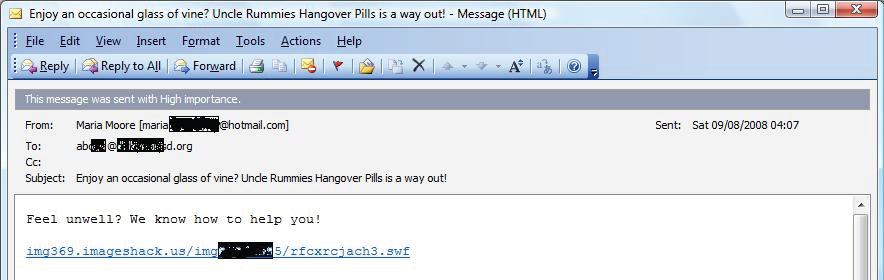
Could a simple flash file redirector pushing fake security software actually trick a large number of users? Of course, especially when the files are hosted at legitimate services, the message localized to a native language, and the links spammed to millions of users.
According to the August 2008 MessageLabs Intelligence Report :
"Analysis highlights that Google Picasa Web Albums is the latest of Google's hosted services to be exploited by spammers while Adobe Flash redirection techniques are also being abused by spammers to host Flash-based .SWF, Shockwave Flash, files that cause Web browsers to re-direct to the spammer's site. Together, both of these new techniques accounted for less than 2 percent of spam in August, but MessageLabs expects these tactics will increasingly generate more spam in the coming months."
With malicious attackers looking for alternative ways to monetize the traffic that's coming to their rogue security software sites, as of recently they've also introduced client-side exploits within the sites, potentially infecting even those who didn't download the software itself. Theoretically, localizing the spam message by translating it into a native language increases the chances that more local users will click on it, and with Symantec reporting a localized message to German with over 300 million instances of it already detected, we have a decent example of a localized attack :
Symantec's comments on the ImageShack attack :
"The .swf attack with the largest volume observed is the German pharmacy attack, with over 300 million instances seen. The body of this message is in German and includes a list of medications that are offered for sale along with the price and assurances that the transaction will be discreet. To order a product, you are directed to click the link of the .swf file, which then redirects you towards an online ordering site. These sites, as well as the .swf links, seem to be rotating fairly often which is a common spammer technique."
With spammers, phishers and malware authors consolidating and working together, it is becoming increasingly common to