Malware poses as fake Yellowsn0w iPhone unlocker
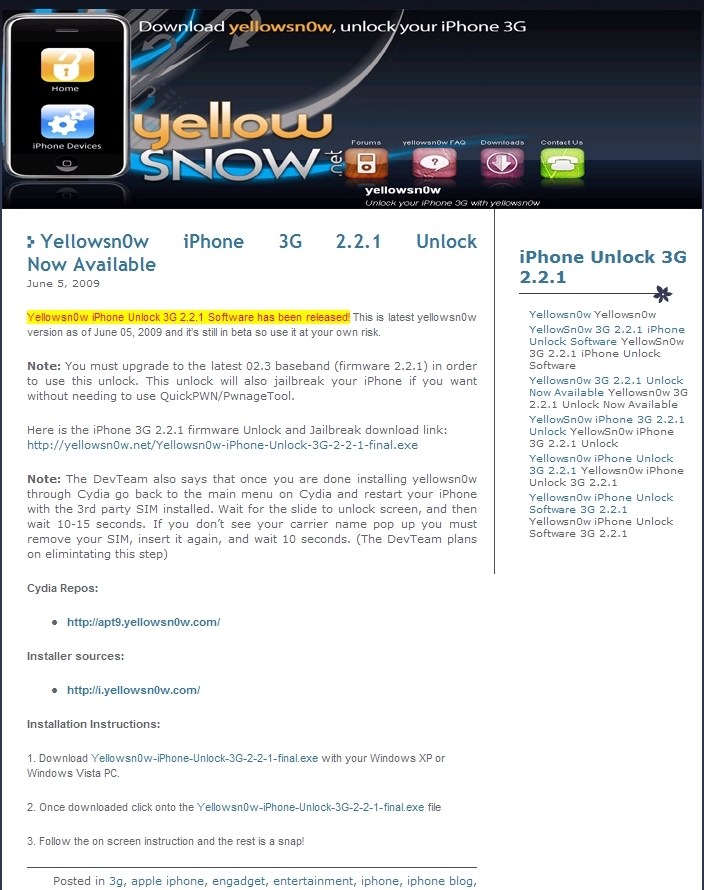
The (now down) -- Wordpress blog yellowsn0w221.wordpress.com was promoting Yellowsn0w-iPhone-Unlock-3G-2-2-1-final.exe at the following IP 74.52.118.244 which is now returning a reported attack site image, presumably in an attempt by the author to cover up his activities.
Upon impersonating the DevTeam, the author attempted to spread it by posting messages across four yellowsn0w-iphone-unlock-3g-221 Google Groups, next to several BitTorrent sites.
The Dev-Team Blog promptly warned users of the bogus nature of tool:
"These are very exciting days ahead! WWDC, the new 3.0 firmware, the new iPhone2,1 device. All in the span of a month or two. Nobody is more excited than we are :) Unfortunately, there are predators out there that are counting on your over-exuberance. Maybe we should call it yell0w fever. One very recent example is a certain yellowsn0w221 page on wordpress.com. Do not download anything from that page if you’re on a PC, else you’ll be infected with a virus. The page talks and talks about a supposed Firmware 2.2.1 yellowsn0w exploit, but it’s all a ruse to get you to download and infect your PC."
Who's behind the malware? Interestingly, at 74.52.118.244 we have a parked domain Jl202site.com, which is registered to Jonathan Larso, who's been "surprisingly" posting "become a iphone unlock affiliate and make %50 of sale" messages across the Web.