MD5 password scrambler 'no longer safe'

The original author of the MD5 password hash algorithmhas publicly declared his software end-of-life and is "no longer considered safe" to use on commercial websites.
This comes only a day after a data breach led to 6.46 million LinkedIn hashed passwords leaking to the Web. Since the data breach, thousands of passwords, including many that could be considered strong, have been decrypted, either through brute force or through lookups.
The primary cause is LinkedIn's failure to properly 'salt' the hashed passwords using SHA-1 algorithm. MD5 is a password hashing algorithm similar to that of SHA-1.
LinkedIn's Vicente Silveira said on Wednesday the company has increased its security "which includes hashing and salting of our current password databases." Although the post says this change was made “recently,” it does not indicate whether the change was applied last month, this week, or yesterday.
Danish developer Poul-Henning Kamp, who developed the widely used MD5 password scrambler, said that limitations to his software and a corresponding increase in computing power since its initial release has rendered his algorithm obsolete.
"I implore everybody to migrate to a stronger password scrambler without undue delay," he wrote in a blog post.
"On a state of the art COTS computer, the algorithm should take at the very least [100 milliseconds] when implemented in software, preferably more. Some kind of 'round count' parameter should be made run-time tweakable so that the runtime/complexity can be increased over time by system administrators."
"The algorithm should be based on repeated data-dependent iterations of several different complex one-way hash functions (MD5, SHA1, SHA2, BLOWFISH, you name it, use them all) in order to 'soak up area' in hardware based attack implementations."
How an MD5 hash is generated.
In 2004, researchers revealed a number of weaknesses in regularly-used hash functions. Later in 2005, MD5 was declared "broken" by security expert Bruce Schneier.
Kamp emphasised that there is "no advantage" in every major website using the exact same algorithm --- "quite the contrary in fact," he added --- as it makes it easier for hackers to develop their attack strategy.
"All major Internet sites, anybody with more than 50.000 passwords, should design or configure a unique algorithm --- consisting of course of standard one-way hash functions like SHA2 etc --- for their site, in order to make development of highly optimized password brute-force technologies a 'per-site' exercise for attackers."
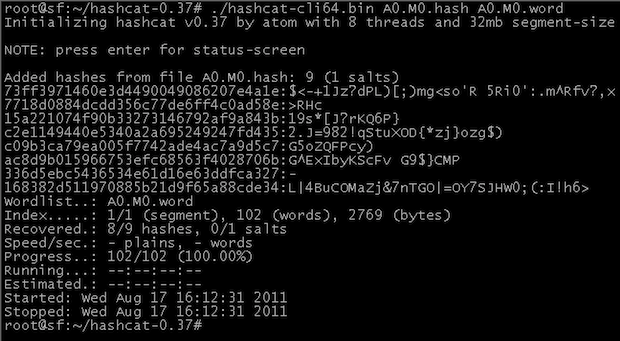
Image credit: Hashcat.
Related: