Microsoft bracing for malware attacks from embedded fonts

Security researchers say it's only a matter of time -- days not weeks -- before malicious hackers start exploiting one of the vulnerabilities via booby-trapped Web pages or Office (Word or PowerPoint) documents.
The specific vulnerability -- in the font parsing subsystem of the win32.sys driver -- provides an entry point for hackers to take complete control of an unpatched machine without any user action beyond normal browsing or opening a rigged document file.
A proof-of-concept exploit has already been fitted into the Metasploit point-and-click tool. According to Metasploit's HD Moore, the code triggers a BSoD (blue screen of death) from a Web page. With some modifications, Moore expects to get reliable code execution very soon.
Microsoft's MS09-065 bulletin says an exploit was already publicly available before the update was ready on Patch Tuesday (perhaps this one released since August?), meaning that malware authors have gotten a long head start researching entry points for attacks.
Metasploit's Moore said it was "a pretty easy bug" to find based on the description provided by Microsoft.
"This demonstrates how just plain wrong some features of Windows are," he added.
According Brian Cavenah, a researcher in Microsoft's security response team, the company expects to see reliable exploit code publicly available within 30 days.
On the SR&D blog, Cavenah outlines the severity of this issue:
The severity rating of critical was chosen since the vulnerable code is exposed through Internet Explorer and can be exercised without user interaction/notification.
Here are the worst-case attack vectors that result in remote code execution without authentication:
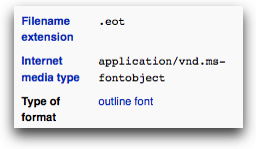
- Malicious fonts (TTF’s) delivered within .eot files hosted on malicious web sites which are rendered in all versions of Internet Explorer by default.
- Malicious office documents e-mailed to victims with social engineering to entice the victim to open the document which contains a malformed embedded font which would then be rendered upon opening the Office document (PowerPoint and Word documents are the most likely attack vectors).
There are also some local attack vectors (worst case scenario is Local Elevation of Privilege):
- Malicious fonts (TTF’s) delivered to win32k.sys by an authenticated user in a multi-user environment (Terminal Services (TS)) scenario. Such scenarios might abuse AddFontResource() to achieve this.
The best protection from likely attacks is for all affected users to download and apply the patch.
Alternatively, affected Windows uers can disable support for parsing/loading embedded fonts in Internet Explorer (warning: Web sites which make use of embedded font technology will not render properly).
This can be done via IE's Tools > Internet Options > Security settings:
* Images via Microsoft's SR&D blog and the Wikipedia entry for Embedded OpenType Font.