New Mac OS X malware variant spotted
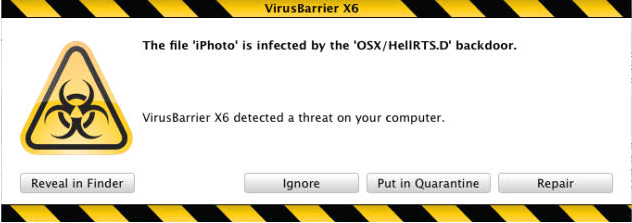
Intego is reporting on a newly discovered variant of a Mac OS X malware first detected in 2004.
According to the company, the source code of the OSX/HellRTS.D is already being distributed across multiple forums, which could potentially allow malicious attackers to create new variants of it.
More details on the malware:
- It sets up its own server and configures a server port and password
- It duplicates itself, using the names of different applications, adding the new version to a user’s login items, to ensure that it starts up at login. (These different names can make it hard to detect, not only in login items, but also in Activity Monitor.)
- It can send e-mail with its own mail server, contact a remote server, and provide direct access to an infected Mac
- It can also perform a number of operations such as providing remote screen-sharing access, shutting down or restarting a Mac, accessing an infected Mac’s clipboard, and much more
A similar leak of source code took place in November, 2009, when the source code for ikee iPhone worm became publicly available. The leak, however, didn't result in any new worm modifications back then.
- Go through related posts: Mac OS X SMS ransomware - hype or real threat?; New Mac OS X email worm discovered (May, 2009); Mac OS X malware posing as fake video codec discovered (June, 2009); New Mac OS X DNS changer spreads through social engineering (August, 2009); iHacked: jailbroken iPhones compromised, $5 ransom demanded
The company has rated the malware as low risk due to the fact that they are unaware of any infected Macs so far.
However, this rating shouldn't apply to you overall situational awareness (See: How To Disable "Open Safe Files After Downloading" Feature In Safari) on the fact that Mac OS X malware is no longer an urban legend, but a fully realistic event with Apple Inc. publicly admitting that "no system can be 100 percent immune from every threat".