Charlatan hijacks iPhone 5S fingerprint hack contest, fools press

Just hours after we reported the crowdfunded effort to hack the iPhone 5S fingerprint scanner, istouchidhackedyet, a shyster hijacked the contest and got big press for it — and has revealed to ZDNet he does not intend to join the bounty award after all.
And some major press outlets fell for it — even though he never had anything to do with the project in any way.
Arturas Rosenbacher told ZDNet by phone last night that his funds are "not liquid" enough to join the contest.
He also separated himself from the bounty contest, telling us that he would not be joining the #istouchidhackedyet crowdfund in either its awarding of the bounty or its terms for the award and laid out his own terms for awarding any funds.
The #istouchidhackedyet bounty can kiss its $10,000 goodbye. And Rosenbacher got some terrific press out of it — even at one point, a profile.
It's unclear whether or not Rosenbacher ever intended to participate in a group award of the bounty, but one thing's certain: he represented and spoke for the project at every press opportunity.
Thursday night, bounty founders Nick Depetrillo and Robert David Graham — along with a few other notorious hackers, such as The Grugq — said they would give cash to whoever proved they could hack the iPhone 5s fingerprint scanner.
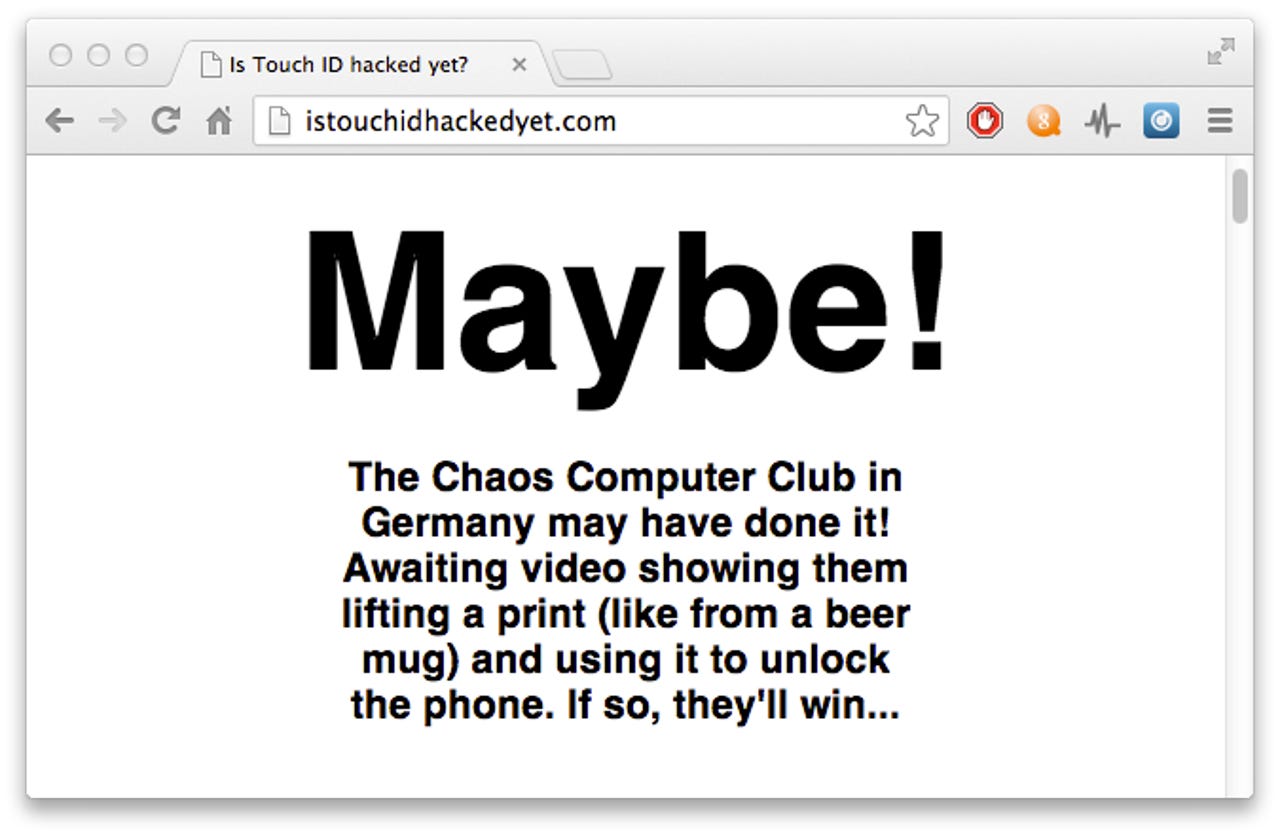
Since their friends in the infosec community had the same "let's break it better" urge about the new premium offering from Apple, and so Depetrillo and Graham made the istouchidhackedyet.com website.
Once the 'pot' turned into a bounty, we reported on it, followed one hour later by Forbes. Then Rosenbacher threw his hat in the ring for an astonishing $10,000.
From that moment, Rosenbacher raced to embrace press and media covering the contest with open arms — as the infosec community leader behind the contest.
If you read or saw items in outlets like CNBC or the U.K.'s Telegraph, you would walk away thinking #istouchidhackedyet was his project. One article for #istouchidhackedyet in the Chicago Business Journal is entirely about Rosenbacher.
Meanwhile, his astonishing $10,000 reward promise — to be put in the community bounty pot — was yet to materialize.
At one point Rosenbacher claimed to some press it was his infosec firm that was behind istouchidhackedyet.com.
Great interview with @Arturas, why his security research firm is offering $10K to 1st to hack iPhone5s fingerprint. Watch @KIRO7Seattle at 5
— John R. Knicely (@JRKnicely) September 20, 2013
In a phone interview Rosenbacher told ZDNet that he does not have an information security company, nor does he work in the infosec industry in any capacity.
Rosenbacher (aka "USAnon") managed to insert himself into nearly every piece of press about the bounty.
Angry that Rosenbacher has hijacked and claimed the community effort as his own to the world (as well as mad as hell that press outlets fell for it), the people actually behind #istouchidhackedyet asked Rosenbacher to put his money where his mouth is.
@Arturas @BloombergTV don't know about u guys, but doing a marketing stunt out of some1 else's idea is not cool imo #istouchidhackedyet
— Mattias Jidhage (@mjidhage) September 20, 2013
When we asked Rosenbacher what his response was to accusations on Twitter that he was faking the offer of $10,000, he told ZDNet that he had not seen anything of the sort and asked if we could describe the tweets.
We did, and it was then that Rosenbacher said that he and his company would deny escrow to any third party as a matter of trust and would instead do a separate award based on "rigor and trust."
.@Arturas what's the best way to contact you for arranging the transfer to @bugcrowd's capable and specialised bug bounty hands?
— the grugq (@thegrugq) September 20, 2013
Part of the new terms Rosenbacher laid out were that the hacker show that they were going "straight to Apple" with their findings.
When asked what his response is to accusations that he'd taken credit for the contest in media and press, Rosenbacher stated: "We did not start the contest. We are just trying to get it going."
To show good faith and in response to their frustration with Rosenbacher's evasion, most everyone offering cash and bitcoins for the hack have now put their donation into an escrow account.
Everyone except for Rosenbacher:
So, this is the same guy who made a fake $10k pledge to #istouchidhackedyet, then took credit for the whole idea. http://t.co/7PaIPRT4C7
— Chris Eng (@chriseng) September 21, 2013
Eng, who is security firm Veracode's Vice President of Research, pointed out an anonymous posting about Rosenbacher.
But a quick Google doesn't help his case much, unearthing a run-in with Occupy Chicago in 2011 (where he withdrew), and accusations in early 2012that he'd "swindled donations" from members of the hacktivist entity Anonymous.
He was quick to tell the world about his upcoming #istouchidhackedyet press appearances.
On CNBC, he spoke for "the hacking community," representing #istouchidhackedyet.
CNBC: What is the hacking community now doing with the phone?
Rosenbacher: (...) Basically, we are trying to make sure that this is as secure as possible before it becomes a problem. (...) We owe it to users of the iPhone.
His elaborations included fabricating what #istouchidhackedyet would do if a hack was indeed found and — incredibly — authoritatively told CNBC that Apple would respond by shutting off the fingerprint scanner to fix it.
When asked if istouchidhackedyet findings would "go straight to Apple," Rosenbacher replied:
Rosenbacher: (...) that will go straight to apple and every national security agency that wants it. We estimate there will be an update to cure that within 24 hours. They might even turn off the fingerprint sensor as a whole until it's fixed.
CNBC: Wow!
Bloomberg — thankfully — featured Robert David Graham in a split-screen with Rosenbacher.
However, while Depetrillo reiterated that he started the whole thing because he wanted to show people that hacking the iPhone's fingerprint scanner was going to be a lot harder than anyone thought, Rosenbacher told Bloomberg — just as he'd told CNBC — that this hack was going to be easy.
By September 20, it wasn't just press who now were publicly handing the project to Rosenbacher.
He was credited for the project's propulsion by every surface-skimmer who stumbled across the news:
I love that @Arturas/@IOCapital and others are making it an compelling challenge to improve Touch ID security, with #IsTouchIDHackedYet.
— Faruk Ateş (@KuraFire) September 20, 2013
By September 21, the hackers behind #istouchidhackedyet decided enough was enough.
Compelled to stop the madness, the following text was added to the website footer: "This site created by @nickdepetrillo and @erratarob, out of discussions with @thegrugq, @quine, @DonAndrewBailey, and a large cast of characters on Twitter."
That cast does not include Rosenbacher's name.
CipherLaw's Jim Denaro said in a tweet (currently unavailable) on Friday: "Spoke with @Arturas," adding: "No escrow can be paid at this moment; but still considering options."
Ultimately, no one has been hurt by the misappropriation and misattribution.
But there's no doubt that a number of hackers are furious that a community effort with good intentions was leveraged as a press opportunity for someone who, in reality, has yet to participate in or contribute to #istouchidhackedyet in any way.
Though Rosenbacher did gain a neat 5,000 new followers on Twitter out of the whole thing.
Still laughing at how @Arturas hacked the hackers ahhahahahahhahah :-]
— The gdb monster! (@osxreverser) September 21, 2013
Most coverage was correct, minus a few details here and there. Some even attributed sources.
But how did some major media outlets get the story so wrong? Lots of reasons, of course.
But two primary issues are on the table: a disturbing lack of due diligence by reporters and writers, and the tirelessness and zeal with which Rosenbacher pursued press opportunities.
@TheBrianDonohue neither myself nor @ErrataRob (who was not credited) were consulted for your article. We are both accessible on Twitter.
— NickDe (@nickdepetrillo) September 19, 2013
Hurrying to get a story out is the wrong excuse for journalists to omit proper attribution.
However, the race to the bottom for pageviews and fame over accuracy and substance (and over respect of both subject and peers) has cultivated an environment where readers are fed incorrect information on a regular basis.
This is a problem — for obvious reasons, many of which are important enough to merit another article.
But in this case, the problem created is the opportunity for people like Rosenbacher to softball his way into major press opportunities over the people behind #istouchidhackedyet — in a media environment rich in low-hanging fruit for the taking.
Or as one wise hacker put it:
@thegrugq @dangents @CipherLaw @nickdepetrillo @ErrataRob "This is why we can't have nice things"
— Dan Kaminsky (@dakami) September 21, 2013
Update 23 September 2013 10:50 PDT: Mr. Rosenbacher deleted his Tweets that were embedded in the original version of this post; the post has been edited to replace Mr. Rosenbacher's embedded tweets with screenshots. Additionally, 12 hours after this article was published Mr. Rosenbacher produced a press release stating that his award is seperate from #istouchidhackedyet with his own award Terms.