Firms needlessly fall to simple attacks

Security researchers have done the analysis and found that simple, not complex, exploits are responsible for the majority of hacker attacks — but many businesses aren't testing for them or other avenues of attack.
Speaking at Informa's inaugural Cybercrime Symposium last week, Pure Hacking chief technology officer Ty Miller ran through his analysis of the past security incidents that occurred in Australia and made it into the media.
"There [are] 535 unique hacker groups or individuals that have been doing the attacks over the last year. There were 22 different attack techniques that they used to break into different systems, and the number of compromised systems was just over a million," he said.
According to Miller, the most common form of attack is carried out by using SQL injection techniques. In properly designed web applications, users are unable to query a company's database directly. Instead, the web application takes the user's input, and uses that in an SQL query that it makes to the database.
However, when these applications are not designed correctly, malicious users can force the web application to run unintended queries of the user's choice, and thereby "inject" their own commands to the database.
"It's basically where an attacker breaks through your website into your back-end database, and can either compromise your internal corporate network, or they can compromise all of your data. With an SQL injection attack, they can potentially rip out your entire client database — all of their data, credit cards, usernames, passwords, all of those things."
Chris Gatford, director of penetration-testing company Hacklabs, has conducted a similar analysis of reported security incidents, but, in his talk, he shared his findings on the last 100 penetration tests that Hacklabs has conducted, including those that don't make it to the media.
"My guesstimate of events that are going on in Australia that make it to the public? About 5 per cent. And I know that because sometimes we're involved in helping organisations recover from [attacks], and they never get to the press," Gatford said.
He confirmed that SQL injection is one of the easiest ways to get into an organisation, but also listed poor passwords, direct object-reference vulnerabilities, software-buffer overflows and poor access-control mechanisms as other easy points of entry for testers and hackers.
Absent from both of the security researchers' common exploits lists were advanced persistent threats and zero-day exploits, with Miller stating that it is wrong to think that these are the average weapons of choice among groups like Anonymous.
"You generally assume that they're using these high-tech attack techniques, like zero-day exploits and things, but actually we found that most of the attacks were SQL injection or distributed denial-of-service, and that probably made up about 90 per cent of the Anonymous attacks. If you actually put in protection against SQL injection and distributed denial-of-service, you're going to find you're knocking out a lot of the attacks that these larger groups are going to be performing," Miller said.
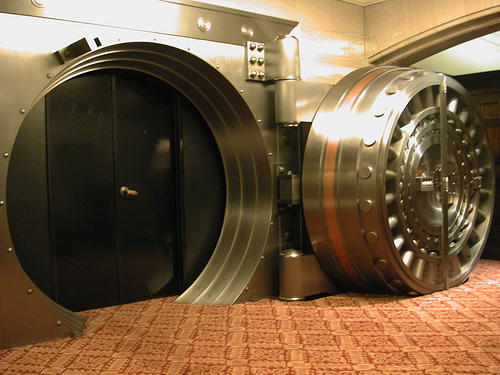
But Gatford, who has previously been given free rein to hack into one of Australia's banks in the past, has used other means to break test the supposedly secure systems. These methods don't necessarily involve sitting behind a computer.
In the banking incident, he posed as a recruiter and used information from social networks to headhunt bank employees. After conducting several phone interviews with those involved with various ICT systems at the bank, he was able to build up a profile of what operating systems and antivirus products the bank was using, whether or not he would be able to log in via SSH and other details, such as their network traffic-control policies.
From here, he found the email addresses of the employees responsible for the bank's accounts receivable and payable functions, and, by dropping a malformed PDF file designed to exploit a flaw in Acrobat Reader, took over their machine and tunnelled out of the machine's network.
Although Australian financial institutions are likely regularly tested these days, Gatford said that other businesses are still doing little to protect themselves.
He said that when testing for vulnerabilities, 40 per cent of his customers have never had a penetration test before. Furthermore, he said that he still finds vulnerabilities in half of those that claimed they had been tested before.
However, both Miller and Gatford said that prevention is better than a cure. Miller said that once hackers are successful, it becomes necessary to perform a forensic investigation to determine how they got in. In addition to the unexpected and likely unbudgeted costs of implementing proper security, Miller said that a complete investigation can cost anywhere from $10,000 to potentially millions. In the meantime, customers would be left in the dark, and e-commerce businesses lose money every day that they are offline.
"If you think of Sony, people were complaining about how long it took them. They took about a week to come out and say "we got hacked". But realistically, you don't want to come out and say you've been hacked until you know what's happened, and you know the extent of it."