What's new in Vista Group Policy?

Group Policy in Vista adds hundreds of settings, giving administrators more control than ever over users and computers. Some of these settings pertain to Vista's new features, and others add more control over features that were carried over from XP.
Let's look at what you can do with some of the more interesting new Group Policy settings in Vista. You can download a spreadsheet containing all of the Group Policy settings for computer and user configuration that are included in the administrative template files that ship with Vista from the Microsoft Web site. Note that administrative template files in Vista use a new XML-based file format (.ADMX).
Unfortunately, they can also pose a big security problem for companies: Users can easily download data that shouldn't leave the company networks to a removable device and take it with them or they can upload data from a device and unknowingly introduce viruses or malware to the company computer.
In the past, some companies went so far as to physically destroy USB ports by filling them with epoxy or some other substance. A less drastic measure was to disconnect the USB ports inside the computer and remove optical drives capable of burning discs. You could buy third-party software to allow you to enable or disable access to USB devices, CD/DVD writers, etc. Or you could create a custom .ADM file to block usage of these devices in XP.Vista makes it much easier.
Here's what you do to apply a policy controlling access to removable media to the local Vista computer:
- Click Start | Control Panel | Administrative Tools.
- Select Local Security Policy.
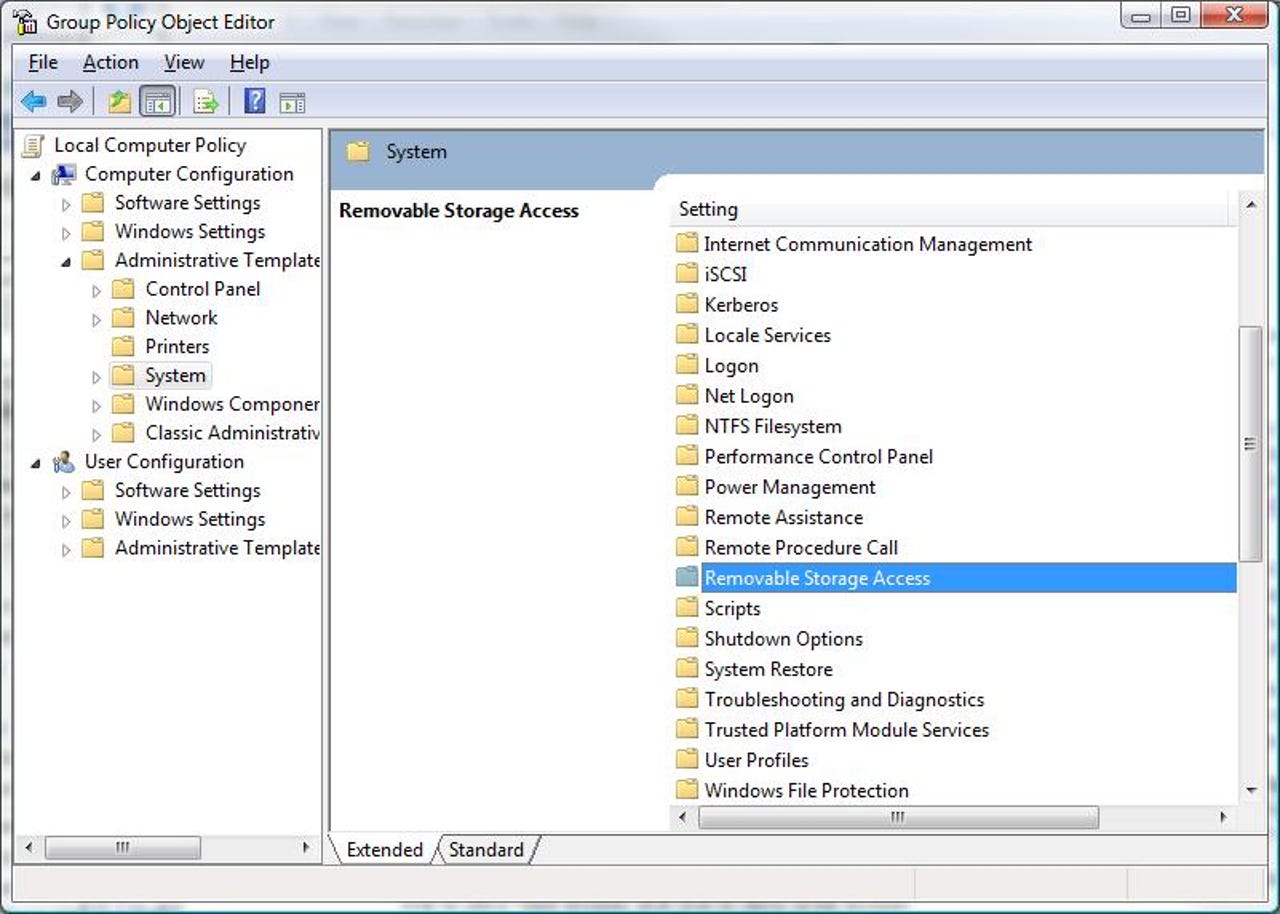
- In the Local Security Policy console's left pane, under Computer Configuration, expand Administrative Templates and click System.
- Scroll down in the right pane and double click Removable Storage Access, shown here.
You can select from a number of choices, depending on what type of removable storage you want to control. For example, you can deny access to all removable storage classes by double-clicking the right pane item All Removable Storage Classes: Deny All Access.In the properties box, select the Enabled option.
The Power Management node in Vista Group Policy, located in the same Administrative Templates folder as the Removable Storage Access node discussed above, contains several subfolders for apply policies to different aspects of power management.
- Select the Power Button action when the computer is plugged in
- Select the Sleep Button action when the computer is plugged in
- Select the Start Menu Power Button action when the computer is plugged in
- Select the Lid Switch action on portables when the computer is plugged in
- Select the Power Button action when the computer is on battery power
- Select the Sleep Button action when the computer is on battery power
- Select the Start Menu Power Button action when the computer is on battery power
- Select the Lid Switch action on portables when the computer is on battery power
The possible actions you can assign to each of the buttons are:
- Take no action
- Sleep
- Hibernate
- Shut down
Double-click the button item you want to configure and select the Enabled option. Then, select the action from the drop-down list.
- Critical battery notification action
- Low battery notification action
- Critical battery notification level
- Turn off low battery user notification
- Low battery notification level
Using these policies, you can set the levels at which notifications will be triggered (low and critical levels). When a level policy is enabled, you specify the value as a percentage of remaining battery capacity (for example, 10 if you want notification when the battery has 10 percent of its full capacity remaining). This setting is shown here.
The notification action policies allow you to specify what the computer should do when it reaches the low or critical level set in the level policies. When you enable these policies, you can select from the following actions:
- Take no action
- Sleep
- Hibernate
- Shut down
To change the settings, under the Computer Configuration node in the left pane of the Group Policy Object Editor, expand Windows Settings, then Security Settings, and then Local Policies. Now, click Security Options.
- Admin Approval Mode for the built-in Administrator account: If you enable this policy, the built-in Administrator account will log on in Admin Approval Mode, which means you'll be prompted to consent before elevation of privileges occurs. By default, this policy is disabled so that the built-in Administrator account (unlike other administrative accounts in Vista) logs on in XP-compatible mode; all applications can run by default with full administrative privileges. Enabling this policy increases security.
- Behavior of the elevation prompt for administrators in Admin Approval Mode: By default, all administrators (except the built-in Administrator account) are prompted for consent before an elevation of privileges occurs. If you enable this policy, you can choose to increase security by requiring that administrators enter their credentials to elevate privileges or you can lower security by allowing elevation without prompting for credentials or consent. The choices are shown in the photo above.
- Behavior of the elevation prompt for standard users: By default, those logged on with standard user accounts are prompted to enter administrative credentials to elevate privileges. If you enable this policy, you can choose to increase security by returning an access denied message when a standard user tries to perform an operation that requires elevated privileges.
- Detect application installations and prompt for elevation: If you enable this policy, application installation packages that require elevation of privileges will be detected through a heuristic algorithm,and the configured elevation prompt will be triggered.
- Only elevate executables that are signed and validated: This policy allows you to increase security by enforcing PKI signature checks on interactive applications that request elevation of privileges. By default, PKI certificate chain validation is not enforced.
- Only elevate UIAccess applications that are installed in secure locations: If you enable this policy,UIAccess applications will not launch unless they're stored in a secure location. Secure locations include the Program Files directory and the Windows\System32\r-_\Program Files (x86) directory. This policy is enabled by default, but you can disable it if you want UIAccess applications stored in other locations to be able to run.
- Run all users, including administrators, as standard users: This policy is enabled by default and is the heart of Vista's UAC protection. If you disable this policy, all UAC policies will be disabled and security is decreased. You must reboot for a change in this policy to take effect.
- Switch to secure desktop when prompting for elevation: This policy is enabled by default; when elevation is requested, the desktop locks down and no applications can interact with it. You can disable this policy to cause elevation requests to display on the normal interactive desktop, but this reduces security.