Predictably, Snapchat user database maliciously exposed

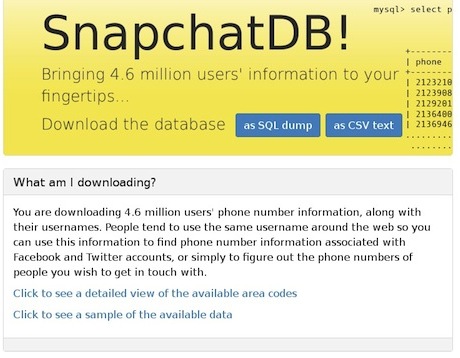
On January 1, 2014, an anonymous user announced the release of SnapchatDB and 4.6 million usernames and matched phone numbers in a Hacker News post.
The Snapchat accounts - even those marked 'private' - were exposed in a database hack that Snapchat knew about for four months, ignored, then told press last week was only "theoretical."
According to SnapchatDB, the leak was made possible with a recently patched, but still useful exploit.
Hacking the database wasn't enough to merit a response
One week ago in December, we broke news that Researchers at Gibson Security published Snapchat code allowing phone number matching after exploit disclosures ignored.
GibSec highlighted several Snapchat exploits and they were arrogantly dismissed by Snapchat, but it looks like someone else has taken GibSec seriously.
The SnapchatDB website is gone, but the database was copied, torrented and mirrored (on Mega) widely prior to its removal.
Several websites immediately sprung up offering a tool for users to see if they're in the database leak. The source of the first and second disclosures, Gibson Security, created this Snapchat hack lookup tool.
The last two digits of each phone number in the hack dump were hidden. But SnapchatDB said full numbers would be revealed for interested parties, indicating the 4.6 million usernames and numbers will likely be sold to spam and phishing operations.
The linking of phone numbers to usernames in accounts from major cities within the United States and Canada is a private information disaster that could have been avoided if the company had acted when repeatedly warned.
Gibson Security told ZDNet that fixing the threat would have only cost Snapchat ten lines of code.
With publication of username matches to phone numbers, malicious entities can now hop-step to brute force account passwords, and cross-match data from other databases to compile profiles across multiple services for stalking, spamming, and more.
In the EU, a person's phone number is categorized as personal information, and falls under data protection laws.
Responsible disclosure is dead
Snapchat joins a long legacy of companies denying responsible disclosure by security researchers, only to be embarrassed when users become victims of the exact targeted attacks whose warnings went ignored.
In October, Apple told press that Apple can read your iMessages with an iMessage man-in-the-middle attack (hijacking and changing messages between iPhones in real time).
Like Snapchat, Apple downplayed the risks and attempting to discredit responsible security researchers by cavalierly labeling responsible disclosures as "theoretical."
In a statement to AllThingsD, Apple spokesperson Trudy Muller said: "iMessage is not architected to allow Apple to read messages. The research discussed theoretical vulnerabilities that would require Apple to re-engineer the iMessage system to exploit it, and Apple has no plans or intentions to do so."
The same day as Apple's dismissal, we published video of the researchers giving us a live demonstration of iMessage interception and alteration between iPhones, directly proving Apple wrong.
Snapchat's story is disturbingly egregious; Gibson Security warned Snapchat in August of its security problems, and went public with claims when Snapchat refused to acknowledge what GibSec felt were issues that put users - such as themselves - at serious risk.
Snapchat did nothing. On Christmas Day, Gibson Security published Snapchat exploits (only a few of the ones GibSec found) in an attempt to spur Snapchat into action to take user safety and database security seriously.
Gibson said it was sick of Snapchat ignoring security researchers.
"That vulnerability is completely theoretical." - Microsoft
Like Apple Snapchat did not respond to ZDNet's request for comment - despite the fact that we first broke news and published technical information about security researchers' discoveries.
In fact, Snapchat admitted to Gibson Security that it first learned about the exploits from our pre-publication email requesting comment about GibSec's disclosures.
Both companies only responded to press outlets that have a record of reporting uncritically about the companies.
Unfortunately for Snapchat, TechCrunch wasn't buying it.
This behavior typifies the irresponsible behavior of companies both new and established when it comes to user security issues - notably different than the companies' behavior about company security issues.
In 1992 an early hacking group known as L0pht Heavy Industries posted a quote from Microsoft, "That vulnerability is entirely theoretical."
It was from an email exchange between L0pht and Microsoft, when the hackers responsibly disclosed the discovery of a security problem (one of the first buffer overflows) in their software.
The quote became the group's tagline, "Making the theoretical practical since 1992."
Publication of such a massive user name and number database gives weight to the other serious problems Gibson Security has uncovered.
Snapchat has ignored Gibson Security's revelation that a mass registration exploit shows there is no way to verify the validity of Snapchat user accounts - raising questions about Snapchat's actual user numbers, versus inflated reports.
Another glaring issue Snapchat has not acknowledged is the direct accusation that Snapchat had lied to its investors, notably Goldman Sachs, about user gender.
Snapchat currently has over five open job listings on its website, none of which include security positions.
ZDNet reached out to Snapchat prior to publication of this article, but the possibility of Snapchat's response is entirely theoretical.