SOPA reincarnates to hold your computer hostage

SOPA. The dearly-beloved anti-piracy bill rightfully quashed before it reared its ugly head and became signed into U.S. law. It only took months of worldwide protests, tech media outrage, site blackouts and the occasional satirical video or two.
A huge sigh of relief spread through the technology community when the bill was discarded -- at least for the moment. However, enterprising virus developers have piggy-backed on to the fear that copyright infringement and court cases produce for the general public -- using the recognizable SOPA branding to lure victims into parting with their hard-earned cash.
The so-called SOPA cryptovirus which warns users that their IP address is on a copyright infringement blacklist has been discovered. The 'ransomware' holds a computer hostage, warning that unless a victim hands over money, data will be wiped. U.S. and Canadian victims have to pay via a MoneyPak prepaid voucher, whereas others have to use Western Union.
Once accused of distributing illegal files, infected users are told they must pay $200 within three days.
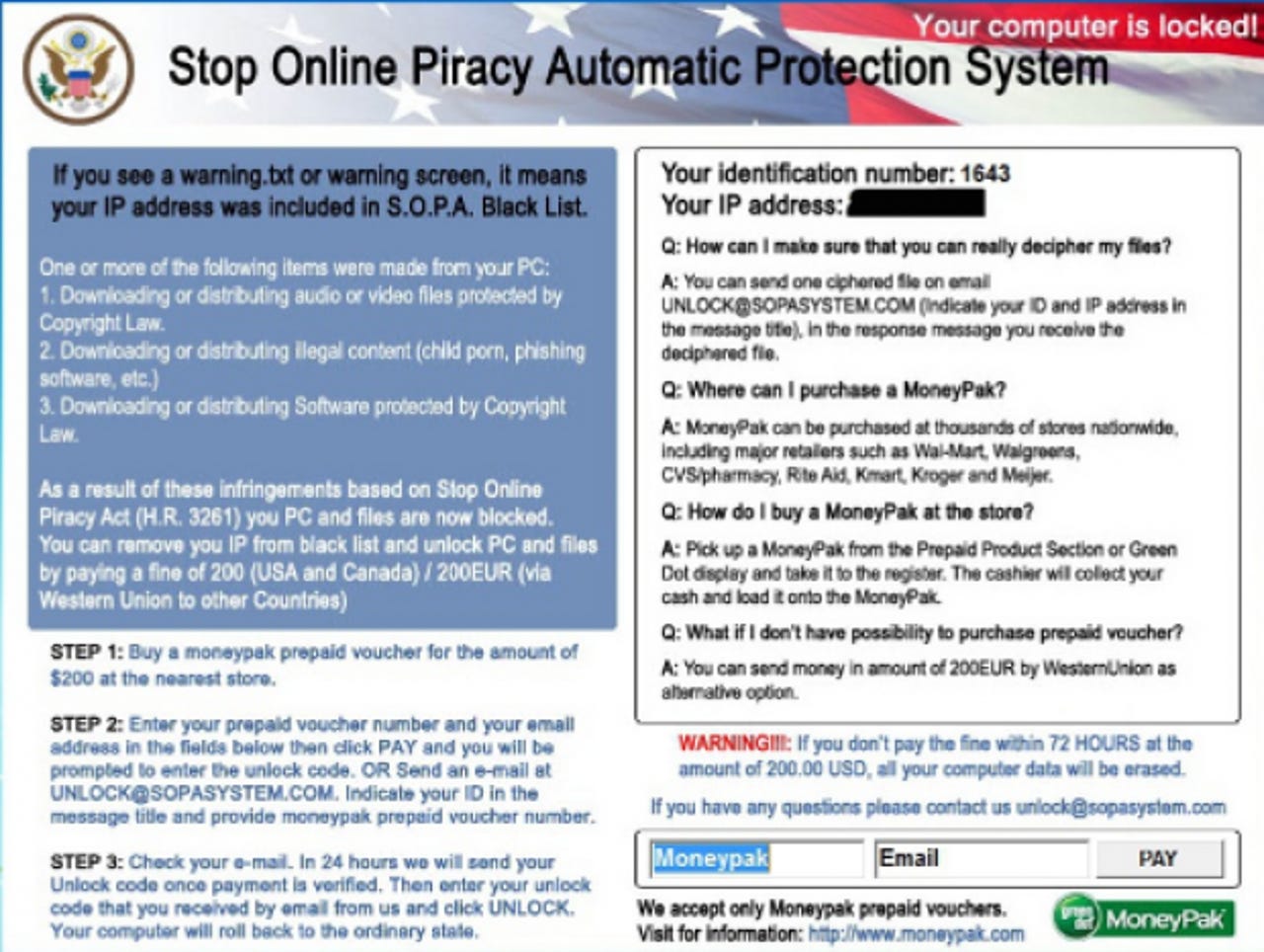
The warning screen above says:
If you see a warning.txt or warning screen, it means your IP address was included in S.O.P.A. Black List. One or more of the following items were made from your PC:
1. Downloading or distributing audio or video files protected by Copyright Law.
2. Downloading or distributing illegal content (child porn, phishing software, etc.)
3. Downloading or distributing Software protected by Copyright Law.
As a result of these infringements based on Stop Online Piracy Act (H.R. 3261) your PC and files are now blocked.
Of course, ransomware must be ignored. As Sophos' Naked Security points out, simply searching for "Stop Online Piracy Automatic Protection System Removal" will get your data back, without spending a penny. However, something that surprised them was the inclusion of a decryption test service. Sophos' Chester Wisniewski says that "If you are willing to mail off one of your encrypted documents with your unique ID number the criminals will decrypt it for you to demonstrate they do in fact possess the keys."
In the same way that phishing emails often appeal to a victim's emotions or expectations of a future event -- consider the tax rebate, student loan company mistakes or banking communications we receive on a daily basis -- it seems that virus makers are also jumping on the social engineering wagon. In both cases, taking a step back and doing your research online before giving out sensitive information or banking details is always the best course of action.