Tor users advised to 'switch away from Windows' after malware attack

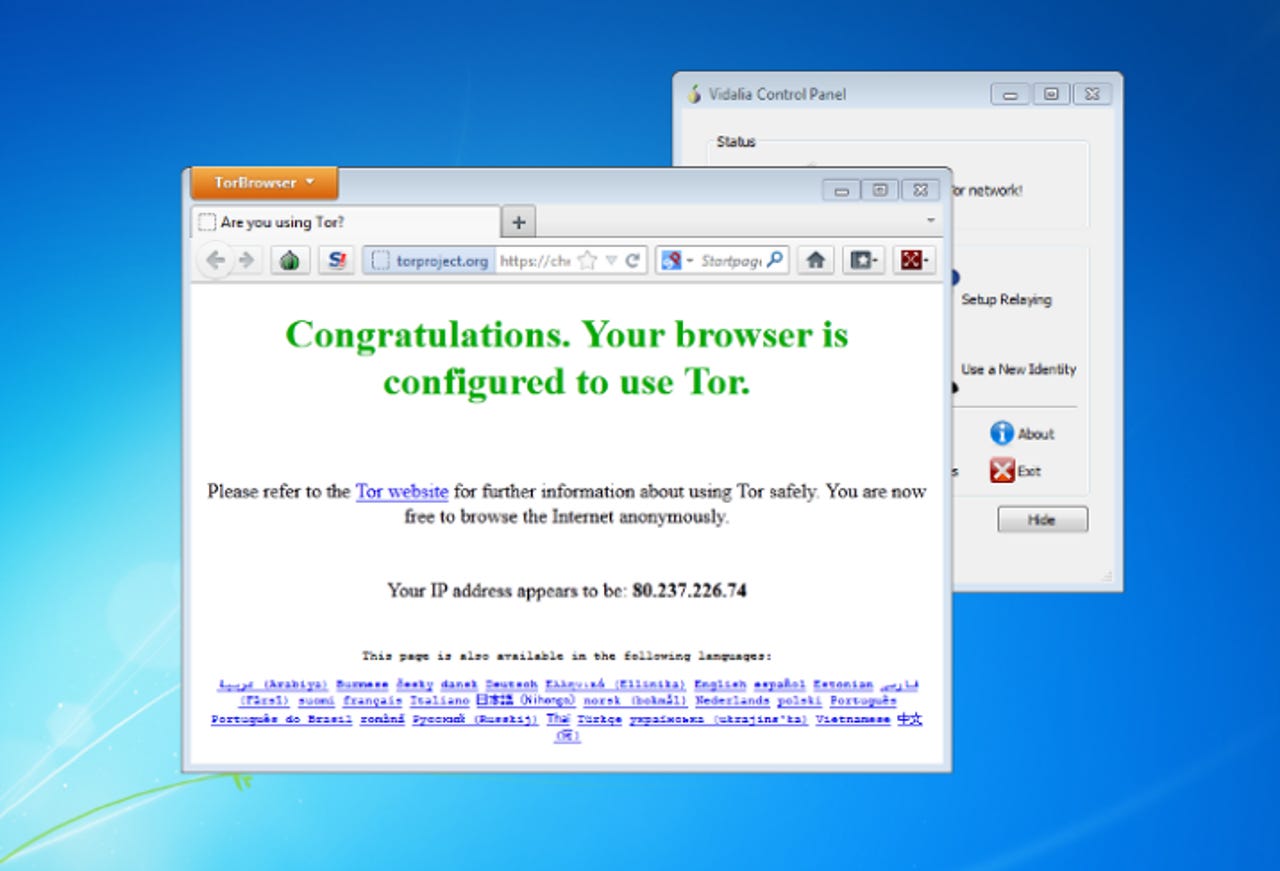
A critical security advisory issued on Monday advises users of the Tor network to stop using Windows and switch to "live" systems if they want to keep their identities anonymous online.
Tor Project staff warned that Windows users with vulnerable Firefox versions "were actually exploitable" to an attack discovered earlier this week.
Some users accused the U.S. Federal Bureau of Investigation (FBI) of exploiting a vulnerability in a Tor bundle, which includes an older version of Firefox 17, with a known security flaw.
However, the true identities of the attackers — whether government operatives or non-state hackers — are not yet known.
Many Tor users are ordinary citizens concerned about government monitoring or private industry tracking, while others use the service to send and receive documents without leaving a trail. The anonymous network is particularly prevalent among journalists and civil liberties activists working in politically unstable regions of the world.
But organized criminals also use the service to evade authorities to distribute illicit goods, including child abuse imagery and illegal real-world goods.
Tor says on its blog that in the network's design, a "user cannot know where the server is located, and the server cannot find out the IP address of the user, except by intentional malicious means like hidden tracking code embedded in the web pages delivered by the server."
The attackers targeted Windows users to gather data used to identify users. The code used to exploit the flaw in Firefox was injected to servers owned by Freedom Hosting, a series of sites accessible only on Tor.
Freedom Hosting was accused in 2011 of hosting child abuse imagery. Controversial hacker activist collective Anonymous attacked the servers and published more than 1,500 names of alleged pedophiles that had accessed the site.
The malware attack is linked to the FBI's attempt to seeking the extradition of Eric Eoin Marques, understood to be the owner of the Tor-operating servers, dubbed the "largest facilitator of child porn on the planet."
The malicious code was reverse engineered and revealed to transmit hostname and unique MAC address data back to a Washington D.C.-based server.
The advisory also notes: "The vulnerability allows arbitrary code execution, so an attacker could in principle take over the victim's computer."
While vulnerable versions of Firefox 17.0.7 and earlier — used in the "browser" bundle to include additional privacy patches — are available for all operating systems, the advisory notes that "only Windows users" were vulnerable to this attack.
Users are advised to switch to live-CD versions of Linux, such as Tails, or non-Windows operating systems, such as Apple's OS X. Affected users should also update to the latest Tor browser bundle. Users wishing to remain on Windows can disable JavaScript, but were warned in the advisory that in doing so will "make some websites not work like you expect."
The advisory also notes that despite the call out to switch away from Windows, there are "many other vectors" for vulnerabilities. The note calls for assistance with Tor project to better improving usability and security.