TrueCrypt quits? Inexplicable

It may rank up there with the greatest mysteries of history: What is Stonehenge? Who was Jack the Ripper? What happened to TrueCrypt?
TrueCrypt (is? was?) an open-source software project for file and full-disk encryption. It was fairly well known and respected. A major volunteer project was under way, run by legitimate crypto people, to give it a formal security audit.
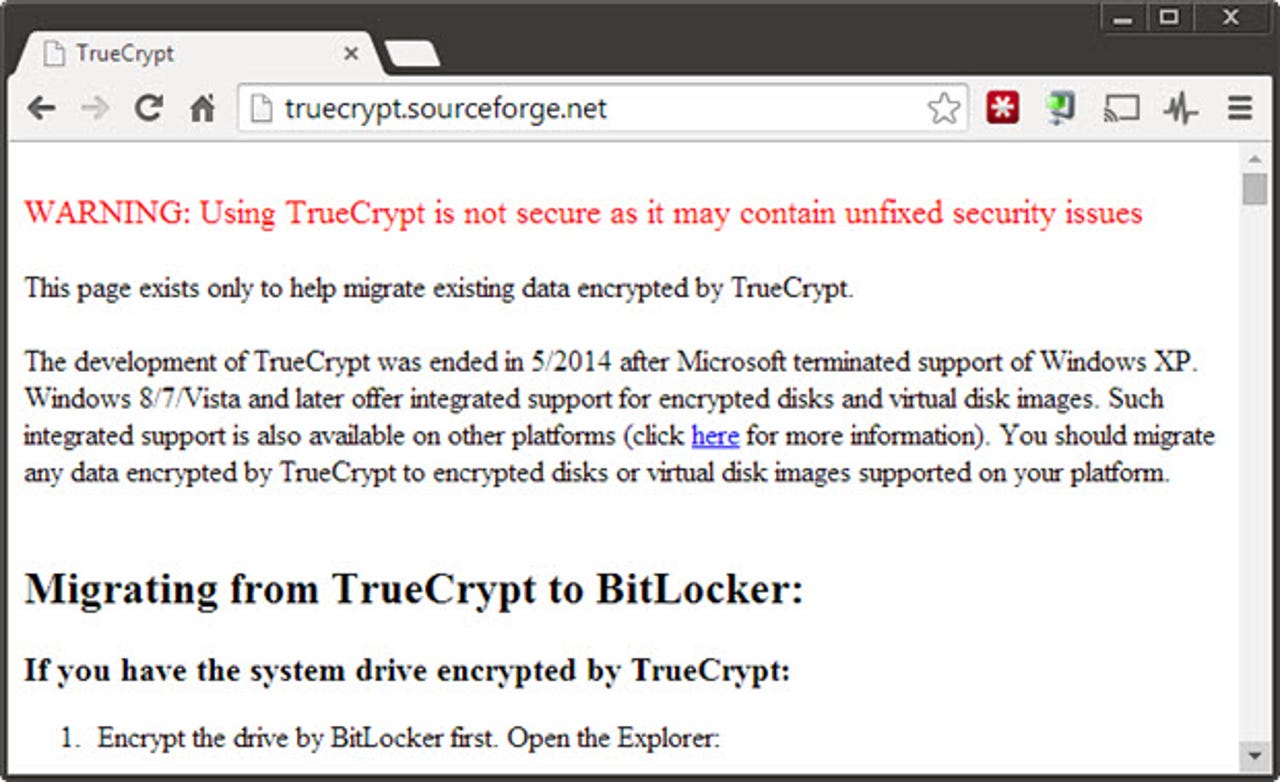
And yet, some time Wednesday, the TrueCrypt project site began displaying a message of abject surrender.
All day Twitter was full of speculation about what happened. The message on the TrueCrypt page is hard to take at face value. What "unfixed security issues?" They ended the project for that? The project was always somewhat mysterious, as the developers were anonymous, so there's nobody to go to for an explanation.
AR + VR
Early on, it was possible to dismiss as a defacement of the web site, but it's lasted a good solid day now and, more significantly, a new version of the TrueCrypt executable was digitally signed with the same key as the earlier versions.
Matthew Green, a cryptographer and research professor at the Johns Hopkins University Information Security Institute, led the TrueCrypt audit project, but he has no special insight into what happened. In an interview with Brian Krebs he said, as he had tweeted earlier in the day, that he believed the TrueCrypt team did it. His guess is that they just wanted to quit and this was their way of doing so with a bang.
He's probably right that, of all the bad explanations, the best is that the TrueCrypt team did it.
There had been real accusations that TrueCrypt could be compromised. As this conversation between Green, and reporter Glenn Greenwald shows, they think Greenwald's partner's hard disk, protected with TrueCrypt, was somehow penetrated by the authorities. Green tells Greenwald "...trusting an uncertified Windows binary from a mysterious anonymous organization isn't good practice."
I don't know that there are any security problems with TrueCrypt in the sense that the TrueCrypt site implies, and I suspect that the claim is phony. The idea that they would pack it in and tell everyone to use BitLocker just doesn't pass the laugh test.
This would all be a lot clearer if only it were April 1.