Meet the 'Spy Smurfs': Here's how the NSA, GCHQ target iPhones, Android devices

British and American spy agencies are able to gather vast amounts of personally identifiable information, including age, location, and even sexual orientation and political persuasions, according to the latest documents leaked by former US government contractor Edward Snowden.
The Guardian, The New York Times, and ProPublica working together each published claims that smartphone apps "leak" data from iPhone and Android apps, which are then piggybacked by Britain's GCHQ and the US National Security Agency.
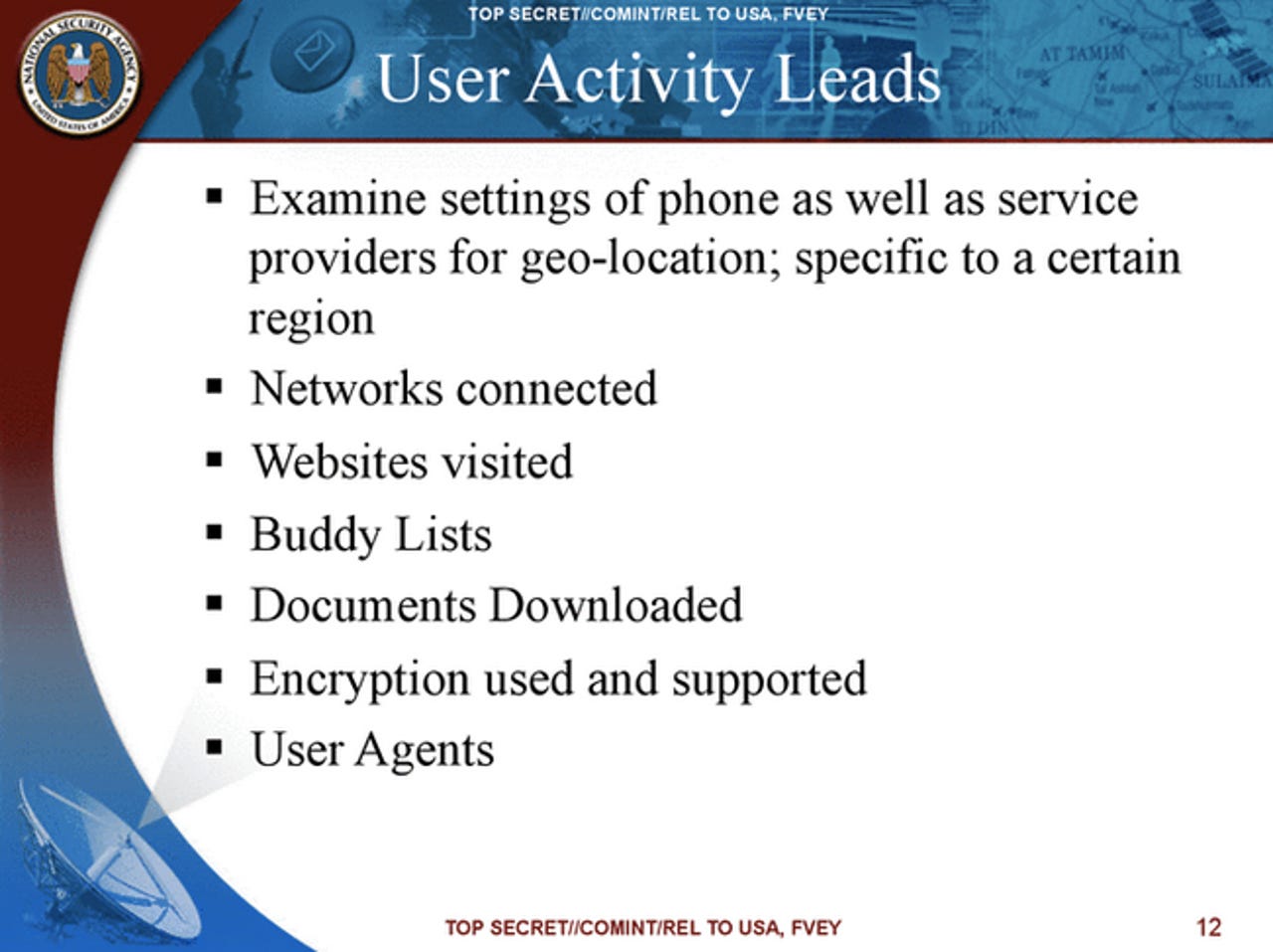
Not needing to tap into a user's smartphone directly, other mass surveillance efforts -- such as cable taps -- provide the intelligence agencies with the bulk of this data.
That's not to say that Britain's GCHQ didn't have the targeted tools against individual smartphones, such as iPhones, Android devices, and other platforms if needed.
Named after the children's television cartoon characters, "The Smurfs," these tools allow the British spy agency to target individual smartphones. For example, "Tracker Smurf" allowed high-precision geolocation, and "Nosey Smurf" gave analysts access to a device's microphone. Meanwhile, "Dreamy Smurf" allowed analysts to switch stealthily activate a device that is apparently switched off.
The Guardian, reporting from New York, said the NSA has already spent $1 billion on this phone targeting effort. The logic behind this is said to be as a result of terrorists and other intelligence targets increasingly using mobile devices.
One slide, titled "Golden Nugget!" describes how a photo uploaded to a social network, such as Facebook, Flickr, LinkedIn, and Twitter, from a mobile device would yield a vast amount of data and metadata, known as EXIF (Exchangeable Image File Format).
Named in one report, smartphone-based queries on Google Maps could be intercepted -- to such a point that one 2008 document described the effort as effectively anyone using the service "is working in support of a GCHQ system."
Not unique to Google's mobile mapping system, the information gathered by apps is designed to be used by an app's advertisers, to deliver relevant targeted content.
Whether this kind of personal data is collected by the NSA or GCHQ remains unclear, as the documents do not state. However, the reports suggest this kind of information would be considered "content," rather than metadata.
Above all else, while the intelligence agencies' approach may be invasive for some, the documents do set out exactly how much data can be collected from popular apps -- in some cases apps that have been downloaded millions, or even billions of times, such as the Rovio app Angry Birds, by smartphone users.
Rovio said it had no previous knowledge of this data collection by intelligence agencies, nor does it work with the British or American spy agencies, The Guardian's report said.
Meanwhile, The New York Times reported that advertisers working with app makers -- such as named Baltimore, MD-based company Millennial Media -- profiles include "optional" data beyond the standard information, including ethnicity, marital status, and sexual orientation.
The latest leaks offer yet another insight into how multiple NSA and GCHQ programs are being used in other intelligence operations, based on other leaks offered by Snowden.
It was reported late in 2013 that the NSA spied on the activities of suspected terrorists in efforts to build up profiles of their personal states, in order to later "discredit" them. The leaks identified a number of Muslim targets said to be vulnerable to accusations of "online promiscuity," according to the BBC News.
This information could be used to "call into question a radicaliser's devotion to the jihadist cause, leading to the degradation or loss of his authority," the leaks suggested.
VIDEO: Your Android phone may have malicious ghost apps installed