Verizon eyes QR codes as authentication option

Verizon Enterprise on Tuesday is launching QR codes as a two-factor authentication option in its universal identity service. What's unclear is how many companies will see the handy QR code as a way to help eradicate user names and passwords.
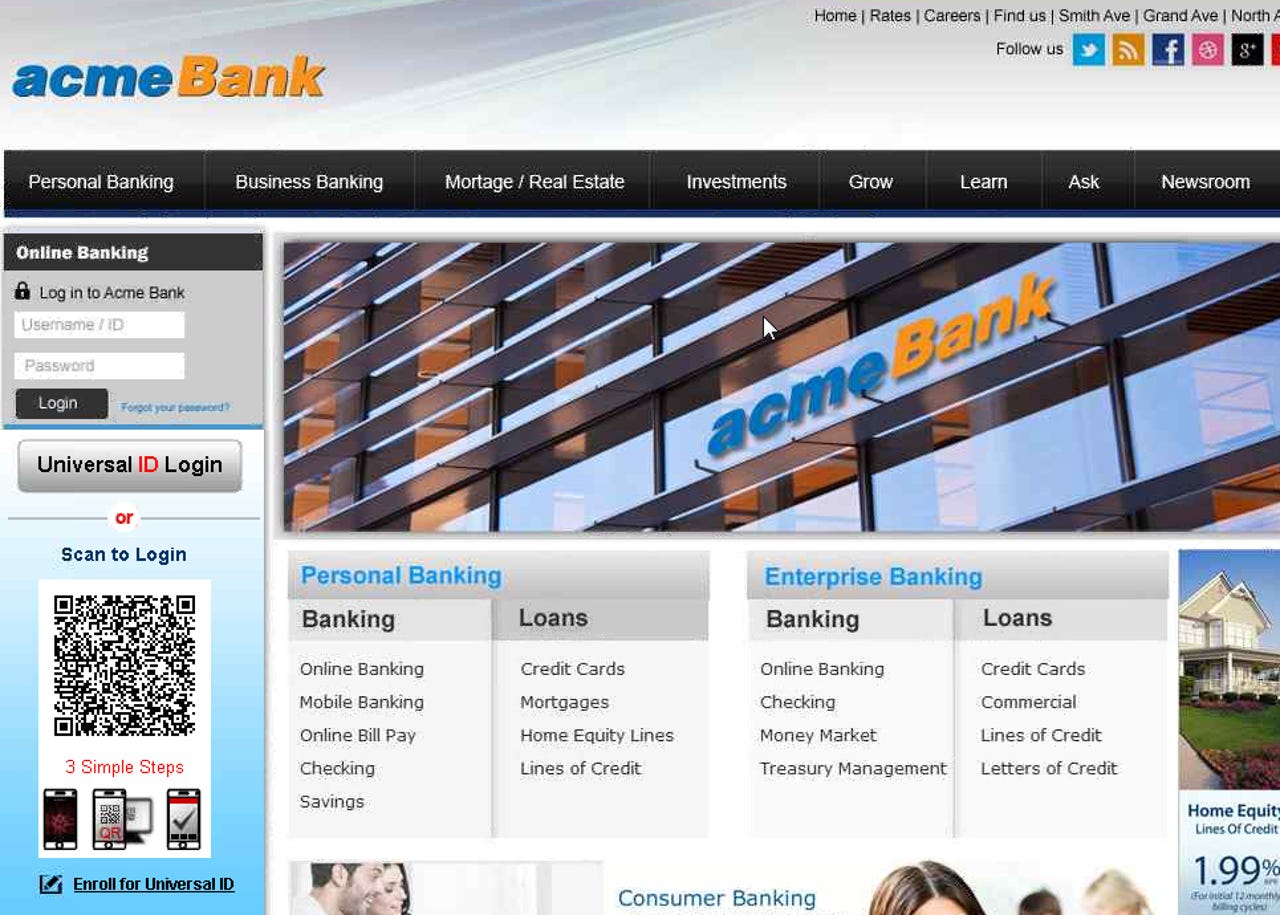
The telecom giant developed a QR code login that would allow a customer or employee to scan a QR code on a website with their smartphone without a user name or password. User names and passwords are a major security issue since few people use two-factor authentication and most passwords are reused across multiple sites. The QR code would get people into accounts without passwords.
Here's how it works:
- Customers could enroll for a Verizon Universal ID from a web page.
- After registering, the customer would download an app that would scan a dynamically generated QR code on a login page.
- Once a user scanned the code and Verizon confirmed the identity, he would be authenticated.
Tracy Hulver, chief identity strategist for Verizon, noted that QR codes could be used as a sole way into a site or app or combined with a PIN code. At an ATM, a user could scan a QR code to tap funds instead of entering a PIN and risking a skimmer. Hulver said enterprises have been interested in QR codes as a way to ditch passwords, but are also looking at other options.
AR + VR
"A QR code is an option, but not the only one," said Hulver, who added that a QR code can be easy to use.
Should Verizon customers start using QR codes, one interesting aspect of this form of two-factor authentication would be ease of use. For instance, I scan QR codes, but infrequently. The extra click and opening of an app means I have to be motivated to get the information.
Meanwhile, the QR code setup means you have to have your phone with you at all times. Most of us always have a phone, but an online retailer could see a QR code as one more friction point in the buying process.
More: