Worst DDoS attack of all time hits French site

Web performance company CloudFlare reported that it mitigated a Distributed Denial of Service (DDoS) attack on a French Website that reached a record-setting attack of almost 400 Gigabits per second (Gbps).
This wasn't just boasting. Arbor Networks, a DDoS security company and CloudFlare rival, agreed that the attack reached at least 325Gbps.
Now for the really bad news: More such attacks are on their way.
Darren Anstee, Arbor Networks' Director of Solutions Architects, said, "According to Arbor Networks’ ninth Annual Worldwide Infrastructure Security Report (WISR) the size of attacks in 2013 eclipsed previous peaks by over 200 percent, with the largest reported attack at 309Gbps. Plus, multiple respondents reported attacks larger than 100Gbps — the previous largest attack size. At 325Gbps [this] attack was yet another new milestone. ATLAS also verifies this growth, with more than 8 times the number of attacks over 20Gbps tracked in 2013, as compared to 2012. Larger attacks are becoming more common and network operators need to ensure that they have the people, processes and infrastructure in place to handle large attack volumes before service, potentially for multiple customers, is impacted."
As for the attack reported by CloudFlare, Anstee continued, "Arbor Networks is able to confirm that its ATLAS system monitored an attack on Monday February 10, targeting a destination in France, which peaked at 325Gbps. As with other large attacks, a reflection technique appears to have been used to magnify the attacker’s capabilities, leveraging network time protocol (NTP, UDP 123) in this case. There also appear to have been other attacks over the week-end ranging in size from 40-80Gbs, targeting destinations in France."
NTP DDoS attacks are new. They were first reported in late December 2013 by Symantec. NTP is commonly used to sync times for systems over the Internet and local networks. If you've ever set the time on your PC or network router with an Internet time server you've used NTP. In a very short time, NTP reflection DDoS attacks have become popular.
This week, they were used in several massive DDoS attacks. The attack that CloudFlare fought off was the largest. Other attacks in the 20Gbps to 80Gbps range have been reported.
According to CloudFlare, these DDoS attacks start "with a server controlled by an attacker on a network that allows source IP address spoofing (e.g., it does not follow BCP38 IP source address spoofing protection). The attacker generates a large number of UDP [User Datagram Protocol] packets spoofing the source IP address to make it appear the packets are coming from the intended target. These UDP packets are sent to NTP servers (port 123) that support the MONLIST command."
MONLIST is a rather useless NTP command that's no longer supported in newer NTP servers. It forces NTP servers to return a list of up to 600 IP addresses that last accessed the NTP server. The response to a single MONLIST request can be up to 206-times larger than the request. CloudFlare explained, "In the attack, since the source IP address is spoofed and UDP does not require a handshake, the amplified response is sent to the intended target. An attacker with a 1Gbps connection can theoretically generate more than 200Gbps of DDoS traffic."
Featured
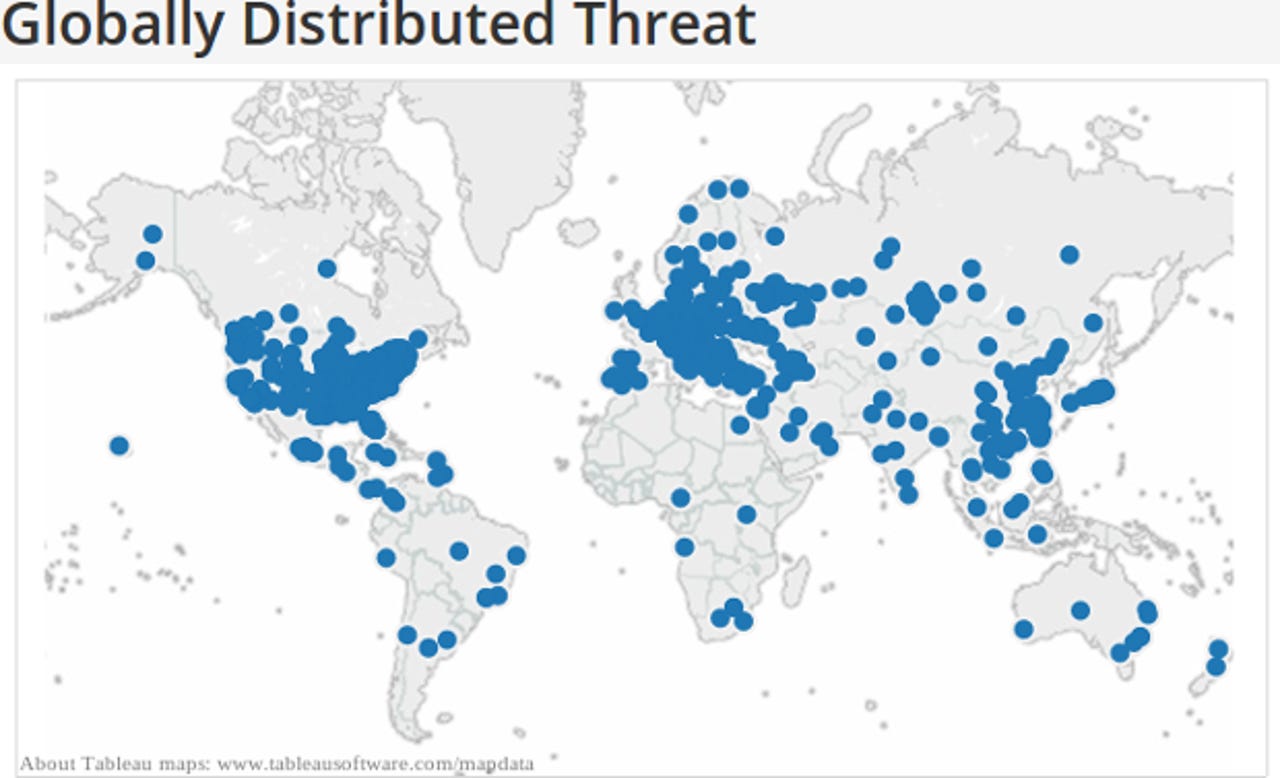
In practice, CloudFlare found that to generate the approximately 400Gbps of attack traffic, "the attacker used 4,529 NTP servers running on 1,298 different networks. On average, each of these servers sent 87Mbps of traffic to the intended victim on CloudFlare's network. Remarkably, it is possible that the attacker used only a single server running on a network that allowed source IP address spoofing to initiate the requests."
The good news is that you can prevent network servers from joining in future NTP DDoS attacks by following a few simple steps. First make sure you don't have an NTP server that's open to the rest of the world that supports MONLIST. You can check this just by visiting the OpenNTP Project site.
If your NTP Server is vulnerable, simply upgrade it to NTP-4.2.7p26 or later. This NTP fix has around since 2010 so only older, non-updated NTP servers should be vulnerable.
You should also make sure your network doesn't allow source Internet Protocol (IP) address spoofing. MIT's Spoofer Project tests will let you know if your network allows address spoofing. If it does, it's not that hard to implement BCP38.
The most annoying thing about this new rash of DDoS attacks is that the fixes to prevent have been around for years. Besides NTP's 2010 fix, the rules to implement BCP38 have been around since 2000!
Yes, these attacks are bad news, but they can only exist in the first place because network administrators and small-office/home-office (SOHO) equipment manufacturers have allowed these known security holes to remain open for years. It's time to close them once and for all. After all, the next Website to get smacked around might be yours!
Related Stories: