High volume DDoS attacks rise in Q3 2014

High volume DDoS spiked in use during Q3 2014, according to new research released by Verisign.
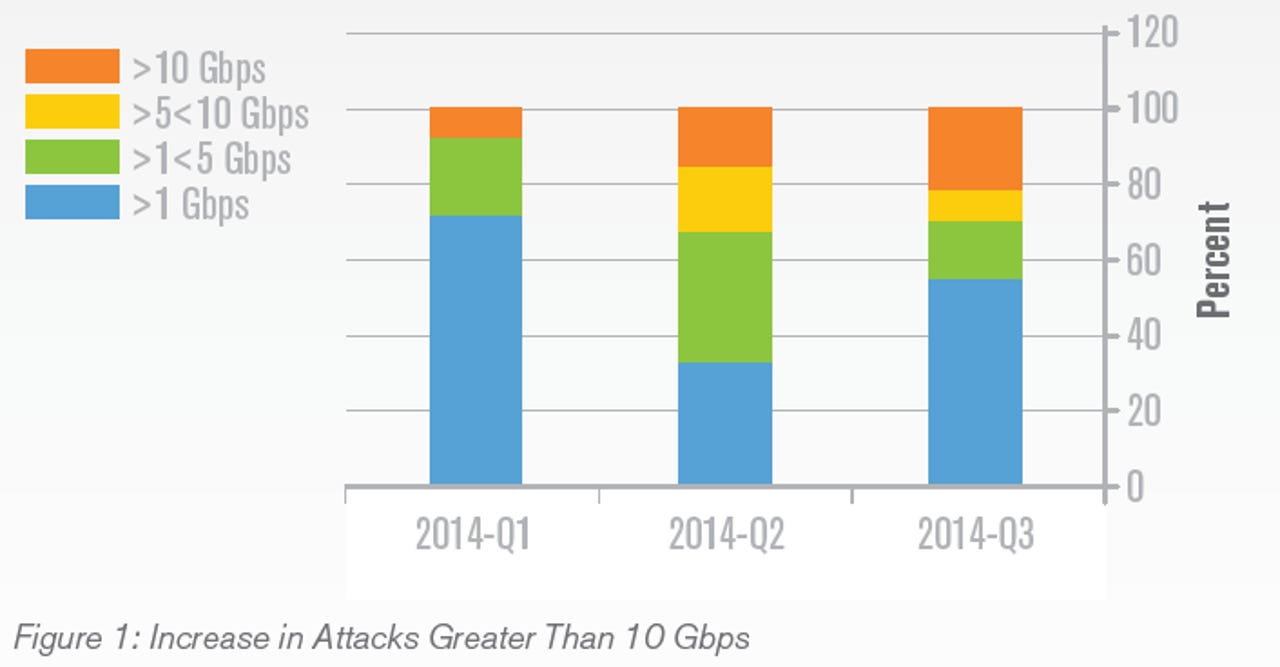
According to the Reston, Virginia-based firm's Q3 2014 DDoS Trends Report, through July to September this year there has been an increase in the frequency of DDoS attacks exceeding 10 Gbps in size, accounting for more than 20 percent of all mitigations conducted by the company.
Of these attacks, the largest was experienced by an online retailer, reaching 90Gbps in size. The cyberattack was aimed at disrupting the e-commerce capability of the victim, and was conducted via a pulsing User Datagram Protocol (UDP) flood employed in short bursts of 30 minutes or fewer -- consisting primarily of Network Time Protocol (NTP) reflective amplification attack traffic.
Historically and understandably, the security firm has seen a spike in cyberattacks against the e-commerce and financial industry as the holiday season gets in full swing.
"This highlights the need for more advanced DDoS protection capabilities other than the standard defenses of over-provisioning of bandwidth and on-premise mitigation devices, which are rendered ineffective the moment a DDoS attack exceeds an organization’s upstream bandwidth, or their Internet service provider’s capacity," Verisign says.
In addition, organizations unfortunate enough to be targeted are suffering an average of three separate attacks per customer, an increase of 60 percent quarter-on-quarter. This may be attributable to easier access to ready-made DDoS botnets and toolkits and the continual evolution and sophistication of cyberattacks -- a trend expected to continue.
Read this
Another element of note within the report is the use of a new protocol for UDP reflection attacks: Simple Service Discovery Protocol (SSDP / UDP port 1900). When it comes down to DDoS malware, Verisign observed increased use of the DBOT backdoor which runs on Unix-like systems and ELF malware, which was deployed through the Shellshock Bash vulnerability.
The most frequently targeted organizations during the third quarter hailed from the media and entertainment industries, representing more than 50 percent of all mitigation activity, while the largest and most resource-heavy attacks were aimed at e-commerce establishments.
Read on: In the world of security
- Apple Pay rival CurrentC hacked
- FBI Director: Mobile encryption could lead us to 'very dark place'
- FBI chief compares Chinese hackers to 'drunk burglars'
- Hackers infiltrate White House network
- Teen hackers charged with stealing $100 million in Army, Microsoft tech
- Enterprise network security takes backseat to speed: McAfee
- Military secrets theft hacking trail leads to Russia
- Facebook doubles advertising bug bounty