One year after Snowden, phone giants' privacy policies are laughable at best

If you didn't laugh, you'd probably cry.
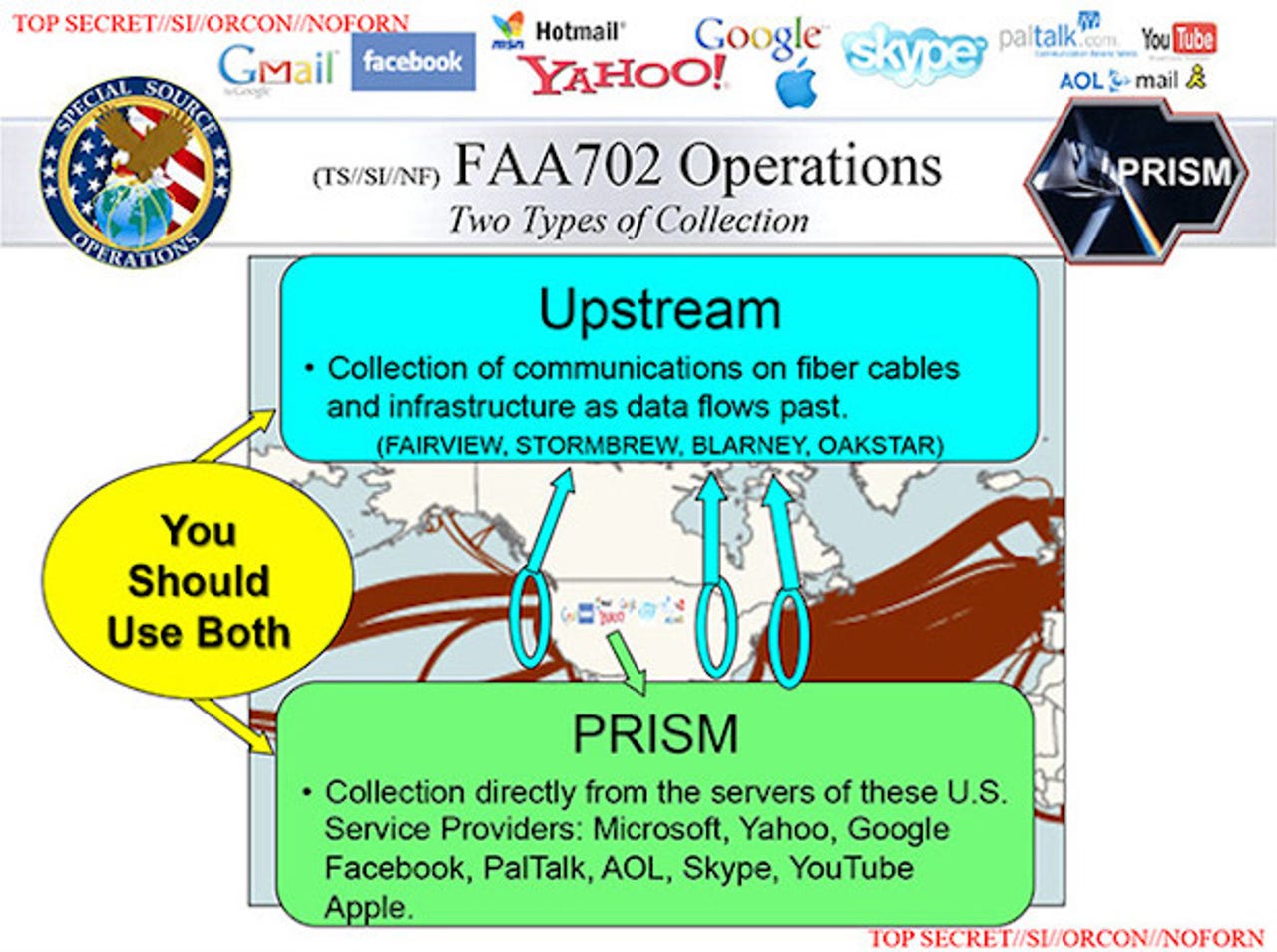
It's been one year to the day since we first learned about PRISM, the surveillance program authorized under Section 702 of the FISA Amendments Act, which allows targeted acquisitions of your Facebook, Google, Microsoft, and Yahoo data — among others.
Known internally as the "702 Program" by senators and congresspeople alike, the highly-controversial program relies on two methods of data acquisition: from the ISP or Internet company level, as well as "Upstream" data from high-level internet infrastructure. This works in conjunction with the U.K. government's "Tempora" program, which helps the U.S. National Security Agency collect data in Europe and further afield.
That relies on the telecom giants. Which phone giants? We don't know, because the U.S. government is holding those secret "relationships" — which are not entirely consensual on the corporate level — close to its chest.
Co-operation with the U.S. and U.K. government is mandatory under telecom regulations and law on both sides of the Atlantic. But the language of these companies' privacy policies are not — repeat not — governed by law.
In fact the irony is that despite the disclosures, and many of these companies being thrown under the bus by the Snowden leaks, they are still, in some cases one year after the fact, still promoting peace, love, happiness, and above all else — privacy.
Which in itself is a loose term.
While we are still not yet sure in every case which companies are handing data over to the U.S. and U.K. governments — among others — the fact of the matter is that the telecom system is broken. The telcos as they stand are legally required to hand over some or all of your data as it flows over their pipes. The global telco system can't be trusted to promote or protect your privacy.
It's not a secret. And the Snowden disclosures only reaffirmed what we knew before. Laws are public for a reason. But their privacy policies are laughable at best. To wit:
BT — U.K.'s largest telecoms provider
As the largest British telecom provider in the U.K., you would think the company would dish out a privacy policy, akin to its American counterparts. No such luck. The company has yet to reveal any government figures, despite being named as a partner in the U.K. government's Tempora program, codenamed "Remedy."
But it does say on its privacy policy, buried way down the page, that:
"We are serious about guarding the security of your personal information and the details of any transactions made. We take appropriate organisational and technical security measures to protect your data against unauthorised disclosure or processing."
Although it falls under European data protection law, each country in the European Union is responsible for its own national security. Often is the case, national security trumps data protection law, because it's secret and nobody will find out. At least the theory goes.
Verizon — U.S. largest telecoms provider, cable operator
Verizon isn't just a phone company. It also provides submarine fiber cables that connect countries to each other. And it probably wins the award for the most laughable privacy policy of all.
Verizon states that it is "committed to protecting your privacy" on its main privacy policy page, adding:
"At Verizon, we are committed to maintaining strong and meaningful privacy protections for customers. Our privacy policy is designed to inform you about the information we collect, how we use it, and your options about certain uses of information."
Not once on this page does it mention anything about handing over data legally to the U.S. government or others, but it does ask you to "read more" — burying it on a second page out of sight.
Let's not forget this is the company that was named and shamed in the leaked FISA Court ruling that forces it to hand over every shred of metadata that it has under Section 215 of the Patriot Act for the U.S. government's bulk metadata program.
Since the disclosures, Verizon served up its own transparency report. It's not easy to find on the website, but it's there. As far as we could tell, there's no word of the transparency report on its privacy policy, either.
AT&T — Major U.S. telecoms provider, cable operator
AT&T hasn't been directly to the wolves by the Snowden disclosures — yet — but the company remains on tetchy ground with the public after it rolled over to the U.S. government a few years ago by letting it (albeit without much say) tap into its network.
On its transparency report website, AT&T says:
"We take our responsibility to protect your information and privacy very seriously, and we pledge to continue to do so to the fullest extent possible and always in compliance with the law of the country where the relevant service is provided."
It was less than a decade since Room 641A, the secret San Francisco, California-based room that was being used by the National Security Agency to vacuum up copies of vast amounts of data flowing through it.
Discovered by an AT&T whistleblower, it led to the disclosures of vast domestic surveillance under the Bush administration, which in turn led to the FISA Amendments Act of 2008 — designed to curtail surveillance of Americans on U.S. soil.
Vodafone — European phone giant, cable operator
Vodafone, which now includes Cable & Wireless, are U.K.-based providers of cell service, landline service, and fiber cables around the world.
The company took a somewhat different approach in its transparency report by blowing wide open, "not without risk," the fact that it has secret government cable taps. Vodafone probably broke half-a-dozen U.K. laws in the process, but the British public will likely thank it for its actions in the end.
In most places Vodafone retains control over its systems used for lawful interception of communications, it became the first telco to disclose that in a number of undisclosed countries where it operates, the authorities have "direct access" to its networks, bypassing Vodafone completely.
Vodafone's report remains the most comprehensive transparency report to date.
That said, its initial privacy statement seems to be at odds with its own transparency report:
"Customers trust us with their privacy and maintaining this trust is at the heart of everything we do. Our aim is to create a culture of privacy at Vodafone, and our Privacy Commitments set out the principles that govern our approach."
Maintaining that trust is all good and well, and Vodafone does a better job of highlighting its need to disclose data to governments and their intelligence agencies. But its privacy-focused sustainability pages are buried from the main site, along with its transparency report, and it's not exactly easy to find if you're a privacy-conscious user.
Featured
There's a simple lesson to learn from this. Although the Snowden disclosures have been eye-opening to the vast global surveillance system we live in today, U.S. and U.K. companies complying with secret requests under their own respective jurisdictions are still not allowed to talk about any involvement, co-operation, or collaboration with state agencies.
It's not a carte blanche anti-transparency movement. The surveillance and intelligence laws (even if their interpretations are secret) are available to read and a matter of record.
But the weaselling and dodging of the issues by some of the major companies only hurts the confidence in the public using their services.
Hey, if it's just the general public that suffers at the end of the day, and not the profits of these corporate giants — then who the hell cares... he says with a hearty dose of sarcasm.