2017 was a dumpster fire of privacy and security screw-ups


Oh look, it's 2017 making a last-minute appearance. (Image: file photo)
If you thought 2016 was bad -- a year of historical hacks and game-changing cyberattacks -- 2017 was even worse. Sure, 2016 may have killed every famous person we ever cared about, but this year brought shame on our favorite companies for getting security wrong and violating our privacy. Companies betrayed you, covered up hacks and renounced their responsibilities, and some just gave up any last damn they had about users.
It all started with this guy: outgoing president Barack Obama.
After eight years in office, one of which was largely embroiled in the biggest surveillance scandal of a generation, in the final days of his administration, Obama relaxed the rules on which intelligence agencies can get raw data collected by the NSA, including on Americans -- just in time for incoming president Donald Trump. Suffice to say, several privacy and rights groups weren't happy. One commentator called it one of President Obama's "most catastrophic mistakes."
Two words for you:

Speaking of the NSA: remember that time it lost control of its stolen hacking tools that let nation-state hackers infect hundreds of thousands of computers with a backdoor later used to deliver WannaCry ransomware?
Yeah, that happened this year.
But on the bright side, the news was only slightly eclipsed by the Equifax breach, whose crappy security practices let hackers steal all your data that you didn't know they had and didn't ask for them to take in the first place.
More than 145 million Americans -- Brits and Canadians included -- had their most sensitive data stolen and Equifax's response was so utterly abysmal (editor's note: sound the massive understatement siren) that the chief executive had to "retire." Not resigned, not fired -- but ebbed into a nice calm, relaxing retirement, where he can dry his tears with his $90 million retirement package. His first call of post-retirement business was a trip to the nation's capital, where he dodged every single question put to him by lawmakers during a Senate hearing in November.
Adding insult to injury, Equifax was told about the massive security vulnerability that it failed to patch(!) months before the hack took place. LOL, right? (But not really.)
Former Equifax chief executive Richard Smith at a congressional hearing in 2017. (Image: file photo)
Now-retired Equifax chief executive Richard Smith blamed just one lone, nameless IT staffer for failing to install the patch, while brushing over how terrible his company reacted following the breach.
Speaking of, you may have forgotten that when FCC chairman Ajit Pai isn't hellbent on ripping up the Obama-era net neutrality rules, he was also pushing for a rule change that let internet providers get more from the data on its customers.
Pai, a former Verizon lawyer appointed FCC chairman in January, put the breaks on the rollout of rules that would've forced internet providers to obtain customer permission before sharing their browsing histories with advertisers. Congress later voted on the rules, passing them by a narrow majority.
Naturally, we thought if Pai would let internet providers share your browsing history, we thought it was only fair for him to share his. (Hint: he didn't.)
FCC chairman Ajit Pai, shortly before he repealed net neutrality rules. (Image: FCC/YouTube)
Researchers earlier this year found that several ridiculously-named dating apps didn't use basic security features, and were leaking their users' data all over the internet. Locations and message histories were leaked, as well as other kinds of sensitive data you wouldn't want inadvertently shared with the world, especially because men are demonstrably awful.
Leaking dating sites is bad but how about letting Jeff Bezos' creepy minions into your house without a key? That's exactly what Amazon pitched to the world earlier this year: a way for delivery drivers to drop off parcels inside a person's home. Don't worry: Amazon gives you an internet-connected camera to put inside your home so users can make sure the delivery driver doesn't raid your fridge (or steal your valuables). Except it didn't work. The camera was busted, meaning rogue delivery drivers could freeze the camera to make it look like everything was fine when, in fact, everything wasn't.
Let's go to a live shot of Amazon's Cloud Cam:
Some good news: the flaw was fixed soon after.
Amazon's crappy cam wasn't the only Internet of Things disaster this year -- and hoo-boy, there were so many. Let's start with the 170 million exposed devices that were exposed to the internet. Webcams, routers, medical devices, and databases -- just to name a few. Not only can data get stolen, but vulnerable devices can be attacked and ensnared into botnets.
Take two examples. One was a not-so-smart lock that left customers stranded and unable to get into their houses. The other was a little more serious -- a heart pacemaker that had to be recalled after it was found that Abbott (formerly St. Jude) devices could be hacked and tampered with. The worst part is that Abbott couldn't update the devices, forcing a few hundred thousand customers to book in for repeat surgery.
From things in your body to things on your body.

Biometrics. Convenient as they are and as unique as they're meant to be, things aren't so great when your data gets stolen and you have to get your fingerprints burned off.
A small exaggeration, but you get the point. India's biometric-heavy society has been described as Orwellian. Everyone has their fingerprint enrolled with the government -- without it, you can go hungry. But some worry India's mandatory biometrics program is on the brink of a catastrophic breach.
Take Estonia, one of the world's most internet-connected economies, and owner of a similar national ID system. It was working fine until a security flaw forced the program into lockdown. Exploiting the flaw could let a successful hacker decrypt citizen data or even impersonate Estonians.
More proof that everything is just great -- until it's not.
Many think ID cards can be used for surveillance. They can. But they're no match for good old fashioned surveillance cameras -- with, bonus feature, facial recognition! Russia and China have become two national surveillance powerhouses in just a few short years. Moscow will use part facial recognition, part artificial intelligence to track you through the streets, while China's massive, overt panopticon can track down anyone in just a few minutes.
It's terrifying to say the least.
Mass surveillance and facial recognition and tracking in China. (Image: file photo)
Meanwhile, the US is trying to sneak around every law and authority it has to spy on Americans -- the one thing it's not really allowed to do (with exceptions -- and more -- and then some). News broke that the Treasury's in-house intelligence unit had found another loophole that allowed the department to snoop on the private financial records of Americans. Decrying the move, the department's own employees warned Congress of the privacy infraction. What did lawmakers do? Nada, zilch -- nothing.
One lawyer in the department's office flat-out called it "domestic spying."
It wasn't the only domestic spying story of the year. ZDNet reported, citing leaked files, that a surveillance program named Ragtime was collecting data on Americans. The NSA neither confirmed nor denied the highly classified program's existence.
If you were annoyed by the NSA overstepping its mark, look no further than what's in your pocket. Your phone may have betrayed you more than you realized.
OnePlus was embroiled in a privacy controversy when its phones were found to be sending identifiable data back to its servers. Other phones made by Blu were pulled from Amazon after an installed app was sending user data back to China. And for a time, Google was collecting your location -- even when it was turned off.
If it wasn't vulnerable to a privacy bug, your phone was almost certainly hackable for a time. A Broadcom chip opened up a whopping billion phones to a Wi-Fi-spreadable worm attack, and Samsung's Tizen phones and devices were riddled with security flaws.
But Apple took the brunt of the "stupid bugs of the year" award.
It's new macOS High Sierra operating system was vulnerable to a password-stealing attack even before the software was released. But worse was a flaw that let anyone get root access by entering... nothing as the password. Facepalms all around for Apple.
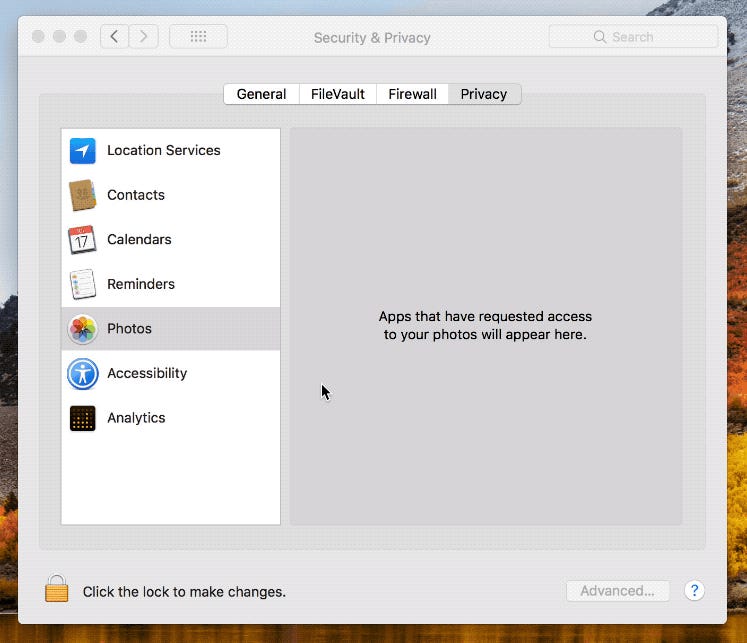
When it wasn't your phone itself, it was an app on it.
If it wasn't AccuWeather sending your precise geolocation to advertisers, it was the risk of Uber secretly recording your iPhone screen. Dozens of apps, as it turns out, were leaking your private data because of a lack of basic app security, and some were doing it covertly behind your back, like uploading your entire contacts list to their servers. And, some so-called secure apps weren't secure at all -- but it's no problem, it's not like anyone in the White House was using them (hint: they were).
It just goes to show you can't trust anyone -- even your apps -- or, if you're an NSA staffer, your Russian-built antivirus, which can detect the highly-classified hacking tools it's your job to develop but not take home and put on your Kaspersky-protected home computer. But that should be a given, right?
Apparently not for some bright spark, who did exactly that.
It's been a tough year -- and we've all taken some hits. While it's all seemed very incremental at times, the overall picture doesn't look great. The reality is that we, as users and consumers, are more aware than ever of the risks we face from hackers, nation states, and even the companies that serve us every day, but it's largely the companies that we rely on that persistently let us down.
Let's hope they do better next year.