Campaign Monitor hacked, accounts used for spamming
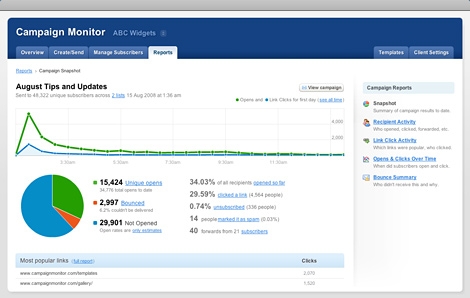
The compromise allowed the attackers to gain access to customer accounts, which they abused by importing their own lists of harvested emails in order to launch spam campaigns using the clean IP reputation of their servers. No credit card details have leaked, according to the company.
More info on the attack:
The main attack took place over this weekend, for a few hours on Saturday and Sunday and continuing into this week. We have up until now been gathering information so that we can contact you with accurate details, and also making sure we were stopping ongoing problems. We did not want to give you incomplete or misleading information. Right now we are still finding out more, but it is important you are all aware of the situation.
We are still actively working to get full detail on this, but essentially one of our servers was compromised, and that gave the hacker enough access to be able to get into a few customer accounts. We now know more, but don't want to publish any details as you can understand.
The incident reminds a similar one where compromised university accounts were used in the very same fashion. However, this tactic is fad due to a spammer's obsession with efficiency, which they're already achieving by using automatically registered/compromised email accounts, now representing close to 20% of the overall spam volume.
Who's behind this attack? It's either a spammer opportunist, or unethical competition that went to great lengths in an attempt to have Campaign Monitor's servers blacklisted, which isn't happening based on their bounce rate monitoring.
The company has notified the owners of the affected accounts, and has commissioned an external security audit.