Cisco CallManager security bug alerts, fixes posted

Colleague Joris Evers reports today that Cisco has just issued a couple of fixes for two VoIP-related security flaws.
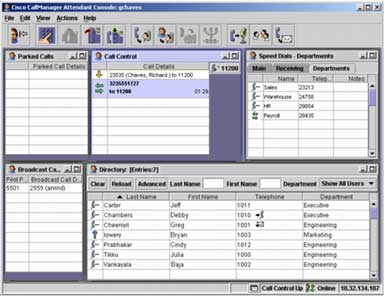
Both flaws exist in Cisco's CallManager software, a screen of which is shown at the top.
These flaws were referenced in separate advisories that warned one flaw could be conducive to a DoS (Denial of Service) attack, while the other could foster a breach in multi-level access privilege permissions.
Both of these pages I've just linked to contain fixes for CallManager versions 4.1, 4.0 and 3.3. If you are running 3.2, woe to you. No fix is offered. Instead, Cisco insists that you upgrade to at least 3.3.
Here are the deets, straight from Cisco.
First for the DoS vulnerability:
Vulnerable versions of Cisco Call Manager do not manage TCP connections and Windows messages aggressively, leaving some well-known, published ports vulnerable to Denial of Service attacks.
CSCea53907—CallManager does not time out TCP connections to port 2000 aggressively enough, leading to a scenario where memory and CPU resources are consumed with enough open connections. In specific scenarios, CallManager will leave the TCP connection open indefinitely until either the Call Manager service is restarted or the server is rebooted.
CSCsa86197, CSCsb16635, CSCsb64161—Multiple connections to ports 2001, 2002, or 7727 can fill up the Windows message queue. This prevents CCM from transacting with the Windows Service Manager, which restarts the CCM after a 30 second timeout.
And now for what Cisco calls the "Privilege Escalation" problem:
An administrative user with read-only permission can use a crafted URL on the CCMAdmin web page to escalate privileges to a full administrative level. This vulnerability applies to users who are authenticated to the read-only administrative level. Users with no administrative access and users with full administrative permissions continue to work as expected.
Successful exploitation of the vulnerability may result in privilege escalation where read-only administrative users can gain full administrative privileges and create, delete, or reset devices.
Hey ITs- consider yourselves warned.