Cisco plugs holes in Voice Portal, SSH implementation

The network routing and switching giant today released three security bulletins with patches for multiple vulnerabilities affecting the Cisco Voice Portal and the Secure Shell server (SSH) implementation in Cisco IOS.
The most serious of the vulnerabilities carries a CVSS Base Score of 9.0 and can lead to privilege escalation attacks against businesses using the Cisco Unified Customer Voice Portal (CVP).
In this advisory, Cisco warns that the vulnerability could be exploited to allow a user with an administrator role to create, modify, or delete a superuser account, which has greater system privileges.
Successful exploitation of the vulnerability may result in full control of the system.
Vulnerable products include:
CVP software versions prior to 4.0(2)_ES14 for the 4.0.x release, 4.1(1)_ES11 for the 4.1.x release, and 7.0(1) for the 7.x release.
Cisco also shipped patches for multiple vulnerabilities in the IOS SSH, warning that the flaws could give unauthenticated users the ability to generate a spurious memory access error or, in certain cases, reload the device. This issue carries a CVSS Base Score of 7.8.
A third bulletin warns of three SSH vulnerabilities in the Cisco Service Control Engine (SCE) that may result in system instability or a reload of the SCE.
The first vulnerability may be triggered during SSH login activity that is conducted within aggressive time frames. The second vulnerability may be triggered with normal SSH login activity in combination with other SCE management actions occurring simultaneously. The third vulnerability may be triggered during SSH login and is specific to the usage of unique invalid authentication credentials.
The Cisco Service Control Engine (SCE) issues carry a CVSS Base Score of 7.8.
Patch download and deployment information can be found in the individual bulletins.
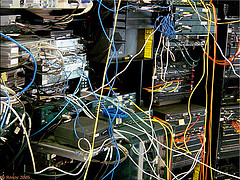
* Image source: roney's Flickr photostream (Creative Commons 2.0)