Cybercriminals promoting malware-friendly search engines
Researchers from PandaLabs have recently uncovered a similar malicious search engine part of the blackhat SEO campaign, where the majority of searches lead to malware serving sites.
The first one has approximately 257,512 unique visitors +63.64% increase since last month, followed by the second one which has approximately 279,665 unique visitors with a +64.26% increase since last month, and the third one is apparently lacking behind with 39,175 unique visitors, a +22.63% increase since last month.
- Go through related posts: Inside an affiliate spam program for pharmaceuticals; Cybercriminals syndicating Google Trends keywords to serve malware; Google Video search results poisoned to serve malware; Malware-infected WinRAR distributed through Google AdWords
Interestingly, the search engines themselves are not visible in Google's results, an evasive practice applied by the cybercriminals who only serve malicious content to users visiting their sites upon clicking on a link from a pre-defined search engine where the blackhat SEO campaigns are active, in this case - Google, MSN, Yahoo, Comcast and AOL.
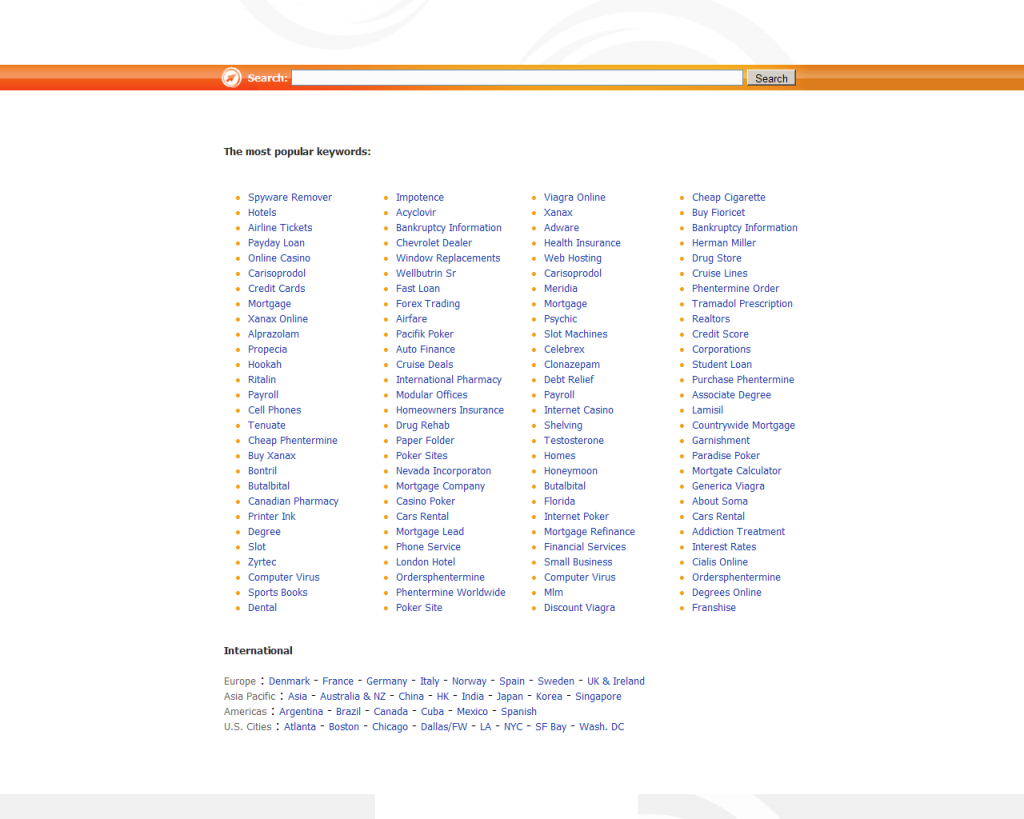
"7Search.com has been a leading Pay Per Click Search Engine Advertising and Affiliate Network since our inception in 1999. As a Search Engine who is dedicated to value and service for online businesses, 7search.com provides thousands of Web entrepreneurs with an economical and measurable opportunity to obtain Internet traffic and generate revenue through their online presence."
The company sued McAfee in 2008 for labeling it as a spyware and potentially dangerous site, which isn't the first, and definitely not the last time when affiliate networks attempts a frontal attack against vendors/researchers.
The use of these fake and malware-friendly search engines demonstrates the complexities of the cybercrime ecosystem, due to the double-monetization approach applied by the cybercriminals, earning pay per click revenue from the affiliate networks, and earning more revenue from serving search results serving scareware and pharmaceuticals with their own affiliate code.