Fake 'Conficker.B Infection Alert' spam campaign drops scareware
Whereas the theme remains the same, the botnet masters have slightly modified the message:
"Dear Microsoft Customer,
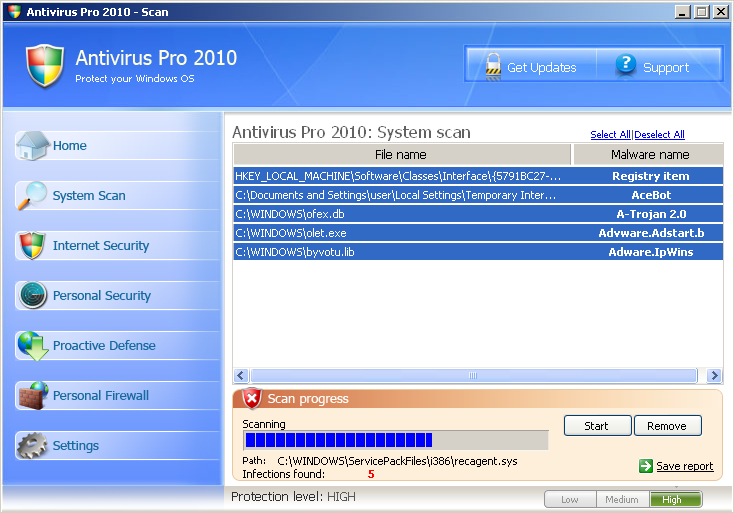
Starting 18/10/2009 the ‘Conficker’ worm began infecting Microsoft customers unusually rapidly. Microsoft has been advised by your Internet provider that your network is infected. To counteract further spread we advise removing the infection using an antispyware program. We are supplying all effected Windows Users with a free system scan in order to clean any files infected by the virus.
Please install attached file to start the scan. The process takes under a minute and will prevent your files from being compromised. We appreciate your prompt cooperation.
Regards, Microsoft Windows Agent #2 (Hollis) Microsoft Windows Computer Safety Division"
The use of email as propagation vector for scareware campaigns (The ultimate guide to scareware protection), and in particular the use of email attachments is an uncommon practice, compared to the single most effective way of hijacking traffic through blackhat search engine optimization where the cybercriminals rely on real-time news events.
The campaign is an example of a -- thankfully - badly executed one in the sense that with Microsoft's Security Essentials recently gained momentum, even the average Internet user would notice the suspicious timing of the offered "antispyware program".