Foxit closes PDF hole used in iPhone jailbreak

Foxit has patched a vulnerability in its PDF reader that is used in jailbreaking software for the iPhone.
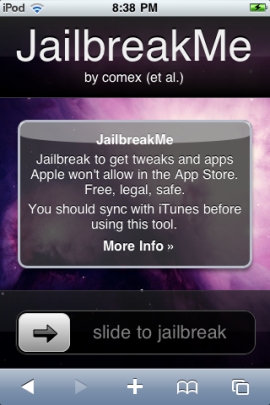
The new browser-based iPhone 4 jailbreak. Screenshot: Steven Musil
The flaw, which is used by Jailbreakme 2.0, could be also exploited to compromise a computer or handset and execute malicious code, Foxit said in its patch release announcement on Friday. The software maker recommended that users update software to the latest version of Foxit Reader, 4.1.1.0805.
A successful exploit uses a corrupted font placed inside a specially crafted PDF file to crash the Compact Font Format (CFF) handler in a Foxit system, F-Secure said in a blog post last Wednesday.
The PDF-related vulnerability, which affects desktop computers as well as handheld devices, came to light after it was used by Jailbreakme 2.0 to bypass Apple's restrictions to install software on iPhones. It can be exploited using the PDF viewer in the Safari browser on iPods, iPads and iPhone3, 3GS and 4, according to an advisory from Vupen.
The Jailbreakme software takes advantage of the way the browser parses PDF files, enabling the code to get inside a protective sandbox. A second hole allows code to break out of the sandbox and get root, or control, privileges on the device, according to researcher Charle Miller. Apple has promised to fix the Safari flaw.