GitHub to devs: Now you'll get security alerts on flaws in popular software libraries

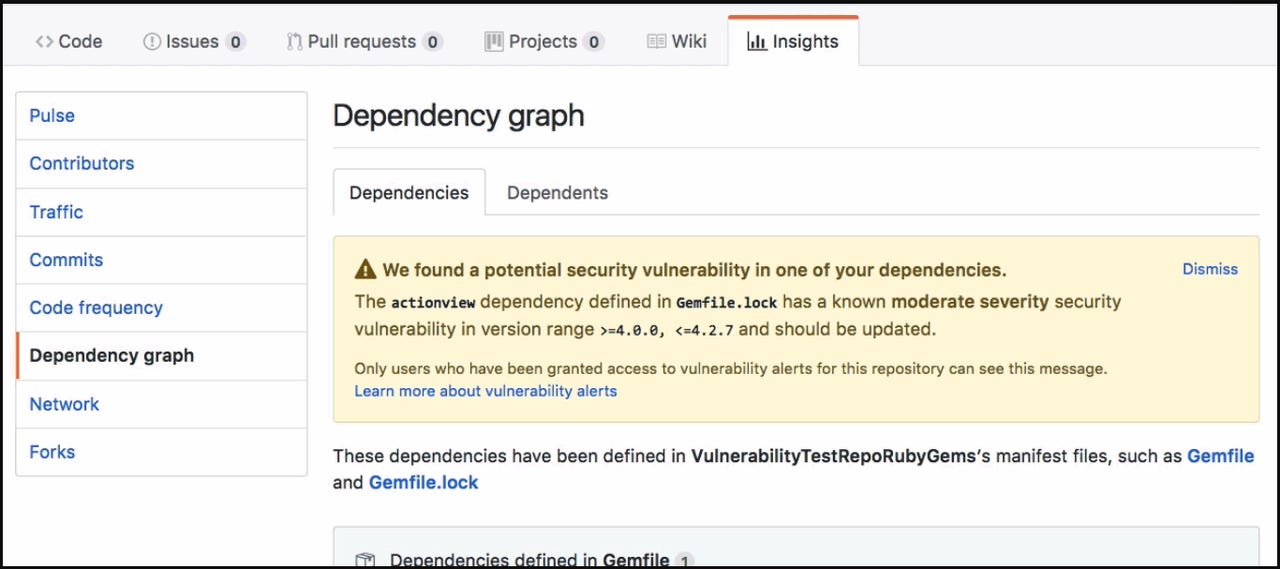
Devlopers can view the security alerts in the repository's dependency graph, which can be accessed from 'Insights'.
Development platform GitHub has launched a new service that searches project dependencies in JavaScript and Ruby for known vulnerabilities and then alerts project owners if it finds any.
The new service aims to help developers update project dependencies as soon as GitHub becomes aware of a newly announced vulnerability.
GitHub will identify all public repositories that use the affected version of the dependency. Projects under private repositories will need to opt into the vulnerability-detection service.
The alerts should have a big impact on security, given that GitHub now hosts nearly 70 million repositories, with projects that rely on dependent software packages or software libraries that frequently do not get updated when new flaws are disclosed.
The alerts form part of GitHub's so-called 'dependency graph', which helps developers monitor projects that their code depends on, and lists a project's various Ruby and JavaScript dependencies.
Developers can view the security alerts in the repository's dependency graph, which can be accessed from 'Insights'.
The alerts are only sent to project owners and others with admin access to repositories. The company promises never to publicly disclose vulnerabilities for a specific repository. Users can choose to receive the alerts by email, web notifications or the GitHub interface.
GitHub's is also using machine learning to suggest fixes from the GitHub community.
The alerts are based on public vulnerabilities in Ruby gems and NPM, the package manager for Node.js, on MITRE's Common Vulnerabilities and Exposures (CVE) List. GitHub will add Python to its vulnerability alert service in 2018.
Python, Ruby, and JavaScript are among the top five languages on GitHub, along with Java and PHP.
It appears the alerts will be limited to flaws with CVE IDs initially. However, as GitHub notes many publicly disclosed flaws don't have CVE IDs. It suggests future improvements will help it identify more vulnerabilities as it collects more data about them.
Previous and related coverage
GitHub aims to make coding more automated
Leveraging 10 years of data, GitHub is introducing automated features it says are "just the start of a longterm roadmap."
GitHub seeks to spur innovation with Kubernetes migration
The GitHub team learned deploying Kubernetes clusters in a physical environment isn't easy; some ended up running a Kubernetes cluster at home.
GitHub: Open source is dominated by men who just can't communicate
A random selection of users for GitHub's Open Source Survey reveal a population that's 95 percent male.