Hack to School: Beware the open school wi-fi

It's back to school time again and many of your kids (my 6th grader included) will be bringing electronics to school every day. Schools generally have rules about when and for what phones, tablets and notebook computers can be used - if they are permitted at all - and now many are offering wi-fi.
At my daughter's school you're only supposed to be using it for school purposes when authorized by a teacher, but in the high school here they can use it for their own stuff during breaks and study hall.
In our district - and I understand this is the usual way these things work - the wi-fi is open, i.e. it's unencrypted, but you have to enter login credentials to gain access. A lot of public wi-fi services, like Comcast's Xfinity Wi-fi, require some sort of similar login.
Don't confuse this login with security on the wi-fi connection. The network traffic on all these connections is unencrypted and anyone else connected to the same wireless access point can sniff your network traffic and, potentially, impersonate you on sites to which you are connected. I'll explain that a bit more below.
Some institutions spend some bucks to make the network more secure. My alma mater, University of Pennsylvania, uses Cloudpath's XpressConnect to secure all wireless connections on their campus wireless network with WPA2.
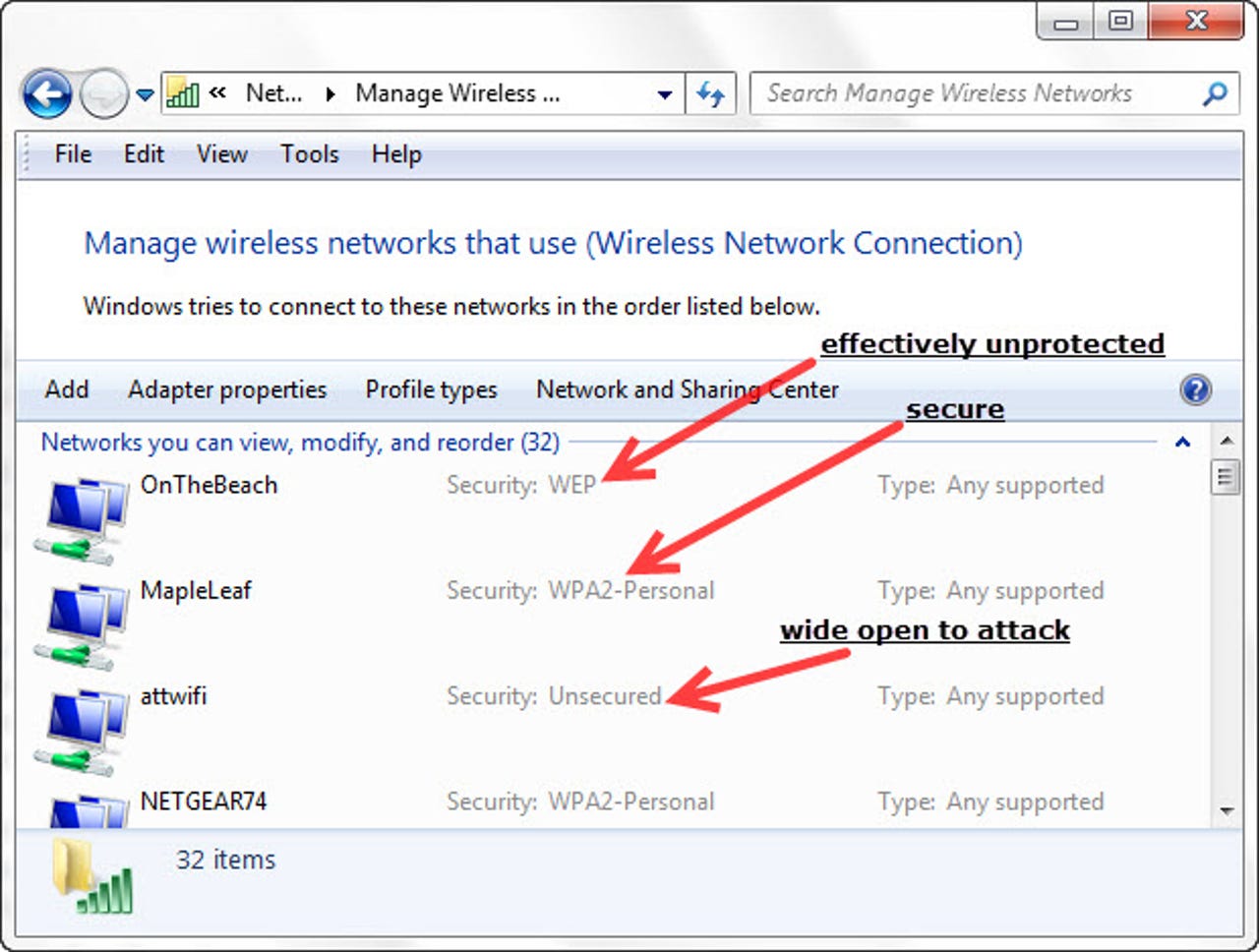
WPA2 is a standard for authentication and encryption of the actual network connection to wi-fi. In the simplest form, which you can do with any home wireless router these days, you set a password for the wireless network and anyone who wants to connect to that network needs the password. XpressConnect is certainly accessing a central directory of users and their individual credentials rather than giving everyone the same password.
In either case, the password is used to create an encryption key, probably using AES encryption. Attackers sometimes get into protected wi-fi networks with dictionary attacks. This means they try to connect using a list of common passwords ('asdf', 'password', 'kitty', etc.) As long as your password isn't one of these trivial ones and is more than a few characters long, it's highly unlikely anyone is going to be able hack into it, and most attackers won't bother; they'll just move on to find an unprotected network.
But there's another advantage to WPA2 that often gets overlooked: session isolation. As I said before, on an open network, all the users can see everyone else's traffic. It's like basic Ethernet without a switch. WPA2 separates everyone's traffic from everyone else's. Because of this, if the provider of a public wi-fi network is interested in protecting their users, they should post a big sign on the wall with the network name and password on it. It doesn't matter if everyone knows the password; the proprietor wants them to get one. But with WPA2 the users will be far better protected from attack.
(Just to be complete, WPA is an earlier version of WPA2 which is not as secure; WEP is the earliest version of wi-fi encryption and is easily compromised.)
But sometimes all you have is open wi-fi, and remember, just because you have to log in to the network in order to gain access to the Internet or local resources doesn't mean the network isn't open.
Security professionals have always known that open wi-fi is utterly insecure, but a few years ago an attack tool arrived which brought the problem more into the public consciousness. Firesheep is a Firefox plugin which searches the local network for other connections and allows the user to co-opt them; yes, the Firesheep user could, back when it came out, find other users on the network on Facebook and take over their Facebook session. The Firesheep user could then act as the hijacked user, posting whatever they pleased.
I switched into past tense in the last paragraph because this specific attack is not doable anymore. Firesheep created enough outrage that Facebook and many other large services switched to using SSL/HTTPS for all connections. When the service you're connecting to encrypts its own traffic, as an HTTPS session does, then it doesn't matter if others can see the session because the traffic on it is encrypted.
And even though Firesheep hasn't worked on Firefox for many versions, it's still possible for someone to find and install an old version on which it works. Or they can use many of the lower-level tools which allow session hijacking: Wireshark and Network Miner being 2 of the finest. These tools are primarily designed for defensive network analysis, but in order to be effective they are necessarily capable of being used for attack as well.
So what are you to do if you have to be on an open wi-fi and have to use an unencrypted service? There's still a solution, and it may be a good back to school gift: A VPN.
A VPN is an encrypted network tunnel. Instead of connecting unencrypted through the wi-fi directly to any service, all your connections are encrypted and go through the wi-fi to a VPN server; at the point they are unencrypted and continue on to their destination (your mail server, iTunes, whatever). Since the unencrypted traffic is not on the local network, nobody can sniff it.
There are many public VPN services. I'm a happy customer of HMA! Pro (HMA stands for Hide My Ass), but there are many others (like Hotspot Shield) and many are free for certain levels of service.
These services can often be used with phones as well. HMA works by using the native mobile OS VPN client but others, such as Hotspot Shield, have apps in the stores. Search in the stores for 'VPN' and you'll find others. I only have recent experience with HMA.
Some schools may block users connecting to a VPN because it is also a way to bypass many security policies, such as if the school is blocking certain web sites. But the VPN is not just for school, it's also for other open public wi-fi like Starbucks, hotels, and friends' houses.
You may be thinking that this isn't a realistic security concern for a school kid. I'm not sure. Sniffing the school wi-fi sounds like exactly the sort of prank I might have tried in high school (decades before wi-fi). Are you actually sure nobody in your kids' school would do such a thing?