Malicious 'Kyle and Stan' ad network uses Amazon, YouTube to target Windows and Mac users

Cybercriminals have been caught using Amazon, Yahoo, and YouTube domains to spread spyware, adware and browser hijackers on both Windows and Macs.
The malvertising network, discovered by Cisco researchers and dubbed 'Kyle and Stan', includes over 700 malicious domains from 74 large websites, and has made 9,541 connections to potential victims since May. Some of the higher traffic domains Cisco has found serving up malicious ads in that time include amazon.com, ads.yahoo.com, youtube.com, and www.winrar.com.
Tech Pro Research
Malvertising — serving malware through online ads — is a persistent pest on the internet, which relies on online ad networks to distribute malware to audiences of popular websites.
According to Armin Pelkmann, a researcher at Cisco's Talos Security Research, while the Kyle and Stan network of 700 domains is large, it's "most likely just the tip of the iceberg" — a guess the company bases on the observation that the domains it uses have a strict naming pattern, which suggests the automated registration of a large number of domains. Currently, said Pelmann, all domains that can be linked directly to the malvertising network are hosted on Amazon.
"The large number of domains allows the attackers to use a certain domain just for a very short time, burn it and move on to use another one for future attacks. This helps avoiding reputation and blacklist based security solutions. All in all we are facing a very robust and well-engineered malware delivery network that won’t be taken down until the minds behind this are identified," he wrote.
But while the ability to scale up the malvertising network is interesting, a distinctive feature of the network is that it's designed to serve up a unique piece of malware for every visitor, making it harder to detect it. In addition, it's serving up different malware for Mac and Windows devices that visit one of the websites running a malicious ad.
"We observed that Windows and Mac users get redirected to different malware in order to infect both operating systems," said Pelkmann.
"Once the victim gets redirected to the final URL, the website automatically starts the download of a unique piece of malware for every user. The file is a bundle of legitimate software, like a media-player, and compiles malware and a unique-to-every-user configuration into the downloaded file."
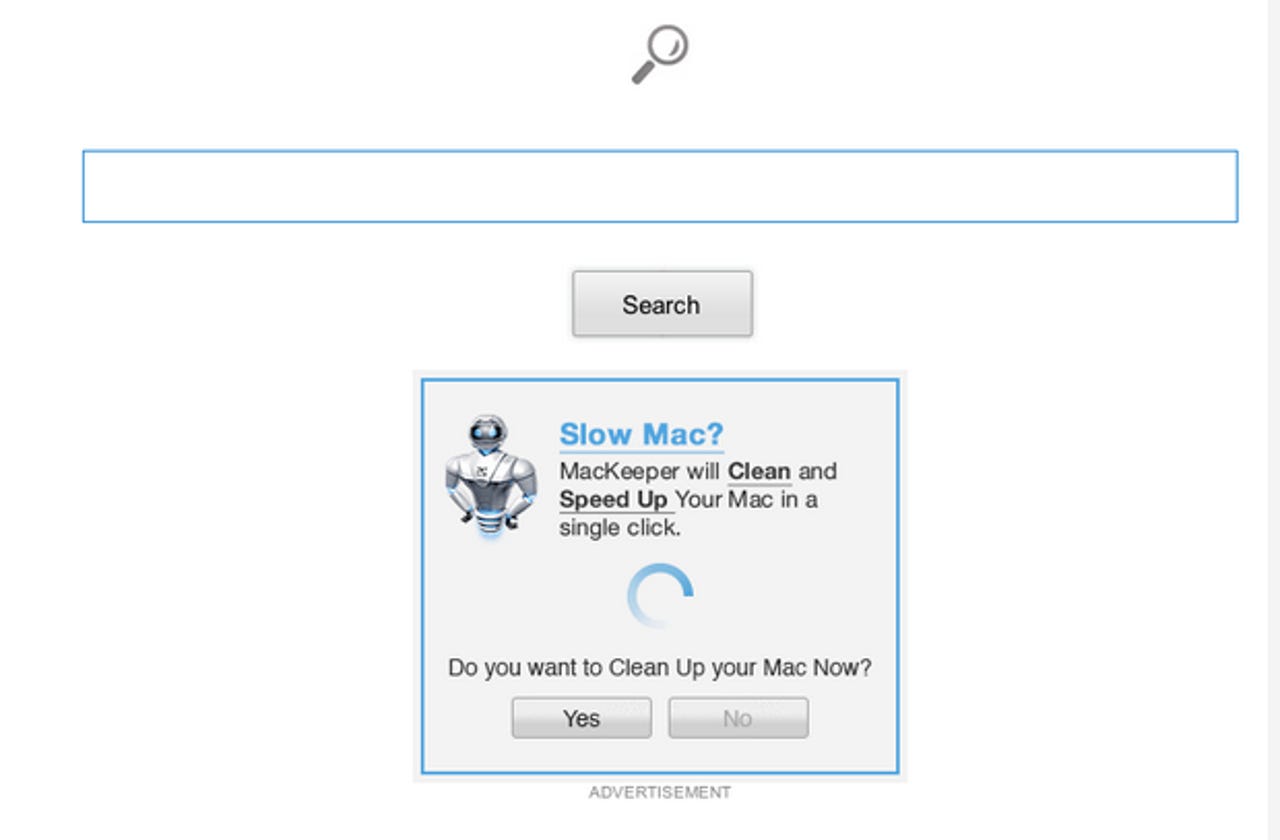
The good news is that the attackers are relying purely on attempts to trick would-be victims into installing the malicious software package — which means there's a point at which the user can avoid infection. In the case of a Mac visitor, the legitimate application MPlayerX is bundled with two adware/browser hijackers known as Conduit and VSearch. Meanwhile, the Windows sample Cisco has found relies on an adware/spyware dropper that retrieves its payload through a GET request.