Manchester City Council pays $2.4m in Conficker clean up costs
Pretty severe according to a recently released a report entitled "Service interruption resulting from ICT disruption in February 2009" which details the financial costs of a Conficker incident affecting Manchester City Council's network - 1.5 million pounds in clean up costs and lost revenue from the downtime.
Where did all the money go, and can this incident cost be used as an average to draw conclusions from in the long term in respect to assessing Conficker's financial impact on affected networks? Let's find out.
The infection obviously caught them off guard, since no antivirus, IPs, patch management solutions or general security awareness were in place. The results came shortly - hundreds of unprocessed bus lane fines due to service disruption, post-infection network-wide USB device ban, installation of antivirus software and patch management solutions, and a thousand Conficker infected laptops accumulating such a hefty clean up bill.
According to the audit report, 600k pounds went for consulting fees support and expertise and another 600k for the purchase of Wyse terminals to replace the PCs which have been affected. The report always tries to emphasize that the purchase of the Wyse terminals has been budgeted long before the Conficker infection took place, which I doubt based on single sentence within the incident response document attempting to explain how Conficker attacks - "The Conficker virus attacks ICT systems by what is known as a “denial of service attack”.
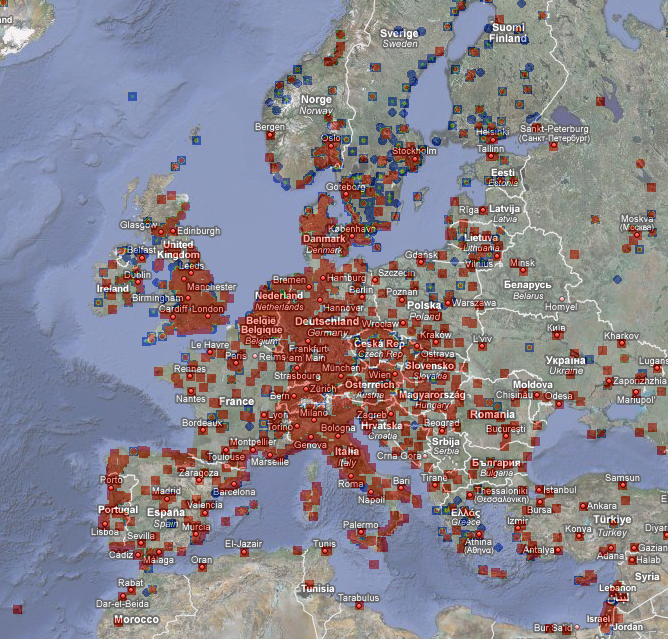
- Go through related Conficker posts: Conficker's estimated economic cost? $9.1 billion; New worm exploiting MS08-067 flaw spotted in the wild; 3.5m hosts affected by the Conficker worm globally; Conficker worm’s copycat Neeris spreading over IM; Fake “Conficker Infection Alert” spam campaign circulating
The 1.5m pounds cost incurred by Manchester's City Council may not be the real Conficker cost, but the cost for the lack of basic security awareness which would have prevented the infection or mitigated its impact. A matter of interpretation or not, the money is gone, and it's money gone in times when Conficker remains in stand-by mode.