Melbourne teen behind Twitter attacks

update A Melbourne teenager has flagged a Twitter vulnerability that led to overnight attacks on what security advisers say could be half a million users.
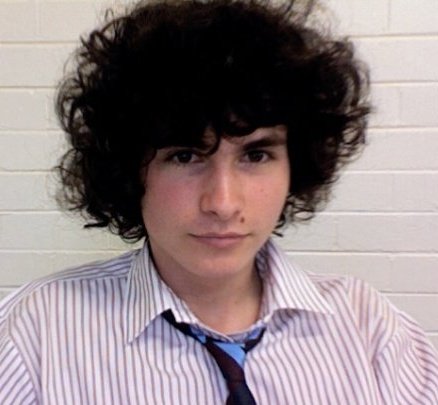
Pearce Delphin (Credit: Pearce Delphin)
High School student Pearce Delphin discovered the cross-site scripting (XSS) flaw following user RainbowTwtr's demonstration of a similar vulnerability, which was used to modify the Twitter background. RainbowTwtr exploited the XSS vulnerability to change the profile background picture to a rainbow colour, and tweeted the script in an update. The code was quickly re-tweeted by hundreds of users.
Delphin inserted a mouse-over field containing JavaScript, and the phrase "uh oh" into a script similar to that used by RainbowTwtr. The phrase then appeared as a pop-up message when the mouse pointer hovered over the code.
In an email, Delphin said he also created a script that would display a user's Twitter cookie that includes private information.
"I was definitely surprised no-one else had noticed such a massive hole, as it could potentially be used to steal tweeters' username and passwords," Delphin said, noting he maintains an interest in social networking and network security, but is focused on law.
"After originally seeing the 'rainbow tweets' Twitter profile, I analysed the code to realise they were using a CSS exploit in order to change the background appearance of their tweets.
"This got me thinking — if you're able to inject custom CSS, what prevents you from injecting JavaScript of HTML code?"
While he noted on his Twitter account @zzap should be kept away from users of the infamous 4chan forum, Norwegian programmer Magnus Holm had claimed to have developed the first non-malicious worm to exploit the vulnerability, which circulated over Internet Relay Chat channels within hours.
Several other worms, including malicious versions, were in circulation soon after.
"There's also another worm spreading thrugh [sic] getScript and some random Russian host. not sure if it's evil or not," Holm wrote on his Twitter feed.
XSS code from Deplhin and RainbowTwtr (Screenshot by Darren Pauli/ZDNet Australia)
The vulnerability, patched last month by Twitter, was exhumed following a website update.
Twitter claimed on its "safety" feed that user information had not been compromised.
"This exploit affected Twitter.com and did not impact our mobile website or our mobile applications," Twitter wrote on its blog.
"However, we are not aware of any issues related to it that would cause harm to computers or their accounts. And, there is no need to change passwords because user account information was not compromised through this exploit."
Kaspersky Labs noted on its Securelist blog that tweet updates exploiting the flaw were appearing at a rate of about 100 posts a second.
The exploit even reached the White House official Twitter page, AAP reports, which is followed by 1.8 million users.
Updated at 2.00pm, 22 September 2010: comments added from Pearce Delphin.