Meltdown-Spectre: Malware is already being tested by attackers

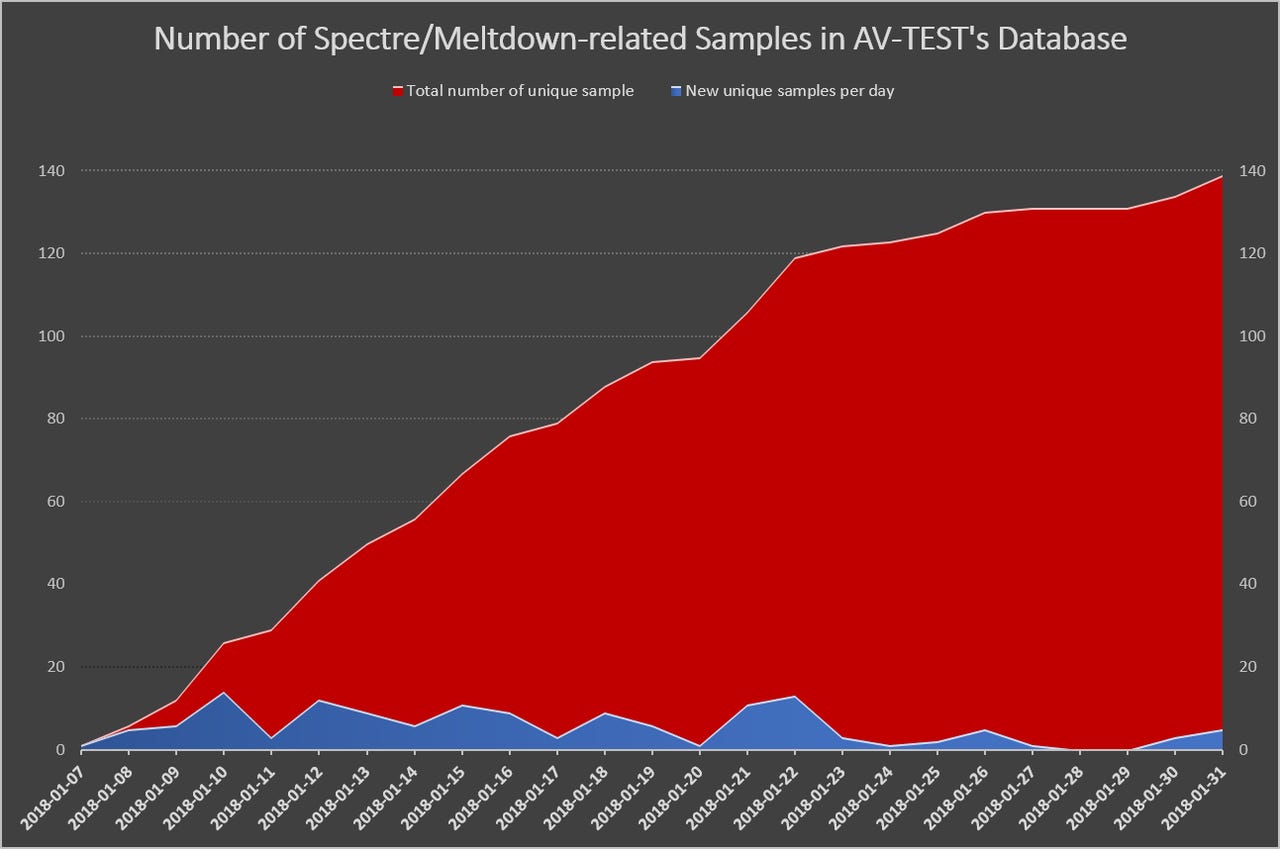
The number of potential Meltdown-Spectre malware samples collected by AV-Test has steadily climbed since the first one was spotted on January 7 to 139 by the end of January.
Meltdown-Spectre
German antivirus testing firm AV-Test has identified 139 samples of malware that seem to be early attempts at exploiting the Meltdown and Spectre CPU bugs.
"So far, the AV-Test Institute discovered 139 samples that appear to be related to recently reported CPU vulnerabilities. CVE-2017-5715, CVE-2017-5753, CVE-2017-5754," the company wrote on Twitter.
The company has posted SHA-256 hashes of several samples that a check on Google's VirusTotal indicates is being detected by some antivirus engines.
Since Google disclosed the Meltdown and Spectre attacks on January 3, operating system vendors, chip makers, and browser makers have released patches to mitigate the three types of speculative side-channel attacks.
Google's Chromium developers assessed that the attacks could impact browsers that support JavaScript and WebAssembly when executing externally code from a website.
As Apple noted after issuing its patches, the Spectre attacks are extremely difficult to exploit, even if a malicious app is running locally on a macOS or iOS device. However, the attacks can be exploited in JavaScript running in the browser. A successful attack could expose passwords and other secrets.
AV-Test told SecurityWeek that it has found the first JavaScript proof-of-concept (PoC) attacks for web browsers. Most of the malware samples are versions of PoCs that have been published online.
The number of samples AV-Test has collected has steadily climbed since the first one was spotted on January 7. By January 21 it had over 100 samples, and as of the end of January the count was 139.
Bugs in Intel's microcode updates for the Spectre Variant 2 attack have caused the most problems on patched systems, prompting HP and Dell to pause and roll back their respective BIOS updates, while Microsoft this week issued a Windows update that disabled Intel's fix for Variant 2. Intel is working on microcode updates that don't cause higher reboots and potential data loss.
In all three cases where updates have been pulled, existing mitigations for Spectre Variant 1 and Meltdown Variant 3 have been left in place. The threat of JavaScript attacks against browsers stems from Variant 1.
AV-Test's CEO Andreas Marx told ZDNet each of the 139 samples only use one of the three attacks. But while the files contain the "problematic program codes", Marx added he can't confirm that all of them successfully exploit the vulnerabilities.
"Due to the extremely high number of affected computers/systems and the complexity to 'fix' the Spectre-Meltdown vulnerabilities, I'm sure that the malware writers are just looking for the best ways to extract information from computers and especially browsers," he said.
As it is though, cybercriminals would probably find it easier and more profitable to use tools to build ransomware or a cryptocurrency miner.
He also offered a tip to minimize your risk of being hit by any more successful Spectre malware that may emerge.
"If you don't need your PC for more than an hour, switch it off. If you go for lunch or a break, close your browser. This should decrease your attack surface a lot and also save quite some energy," said Marx.
Previous and related coverage
Windows emergency patch: Microsoft's new update kills off Intel's Spectre fix
The out-of-band update disabled Intel's mitigation for the Spectre Variant 2 attack, which Microsoft says can cause data loss on top of unexpected reboots.
Meltdown-Spectre: Why were flaws kept secret from industry, demand lawmakers
Great work on patching your own products, but why were smaller tech companies kept in the dark?
Spectre flaw: Dell and HP pull Intel's buggy patch, new BIOS updates coming
Dell and HP have pulled Intel's firmware patches for the Spectre attack.
Windows 10 Meltdown-Spectre patch: New updates bring fix for unbootable AMD PCs
AMD PCs can now install Microsoft's Windows update with fixes for Meltdown and Spectre and the bug that caused boot problems.
Meltdown-Spectre: Intel says newer chips also hit by unwanted reboots after patch
Intel's firmware fix for Spectre is also causing higher reboots on Kaby Lake and Skylake CPUs.
26% of organizations haven't yet received Windows Meltdown and Spectre patches (Tech Republic)
Roughly a week after the update was released, many machines still lack the fix for the critical CPU vulnerabilities.
Bad news: A Spectre-like flaw will probably happen again (CNET)
Our devices may never truly be secure, says the CEO of the company that designs the heart of most mobile chips.