Microsoft fixes critical Windows, IE flaws for Patch Tuesday

Microsoft has released four critical security updates for Windows and Internet Explorer, along with a bevy of other products, in order to protect against at least 19 vulnerabilities identified in its software.
On deck this month, there are four "critical" vulnerabilities that affect Windows, Internet Explorer, Office, and Windows Server, including one for Silverlight that affects both Windows and Mac machines.
Critical updates are reserved for security flaws that could compromise the security of a device or system data, while important updates are reserved for those that could lead to an increased scope of attack by malware or hackers, such as an elevation of user privileges to allow hackers to access system files under administrative reach.
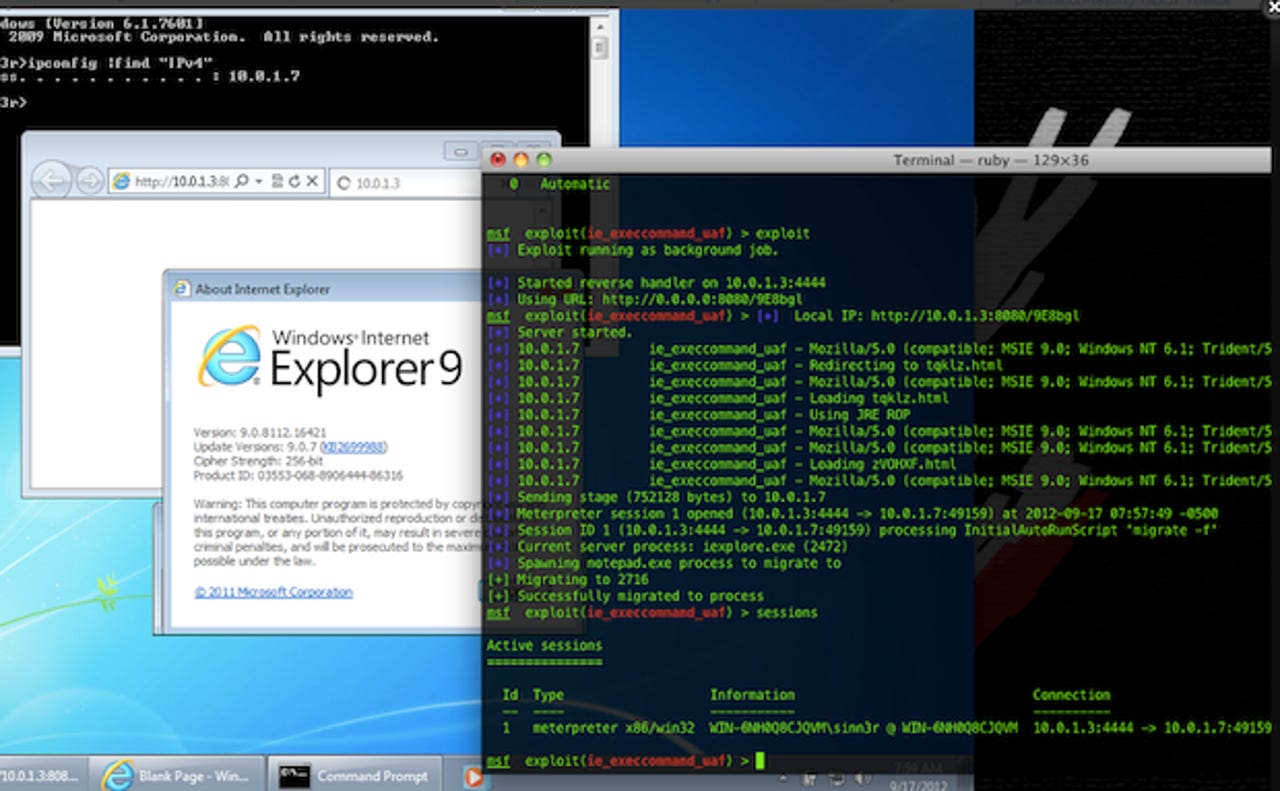
First and foremost, Microsoft has fixed a nine vulnerabilities in MS13-021 — eight privately disclosed flaws and one that was disclosed publicly — in which the web browser was at risk of being attacked by a flaw being actively exploited in the wild for around one month.
The most severe Internet Explorer flaw affected all versions of Windows XP (Service Pack 3) and above, including Vista, Windows 7, and Windows 8 — including tablets running Windows RT — running Internet Explorer 6 and above. The flaw could have allowed a hacker to access the vulnerable system with the same user rights. Those running as "users" rather than "administrators" were less at risk from having system files or documents affected.
Other critical vulnerabilities include MS13-022, which patches three flaws in Silverlight that could allow a hacker to gain access and take over a Windows-based or OS X-based machine.
Meanwhile, MS13-023 affects Office, specifically Visio, that could allow remote code execution if a malware-ridden Visio file was opened on a vulnerable machine. MS13-024 affects Windows Server-based systems running SharePoint, in which an attacker could plant malicious code in a search query, commonly known as an XSS vulnerability. This would have given hackers full administrator rights over the affected system.
Read this
The other vulnerabilities rated as "important" could allow data and information disclosure, or an elevation of privileges on affected machines. These affect SharePoint, OneNote, Outlook for Mac, and kernel-mode drivers in Windows-based machines.
On Microsoft's Security blog, Dustin Childs explained that the software giant has taken a "recent shift" in its approach towards application updates on the Windows Store, such as those that are available for Windows 8 and Windows RT-based machines.
"In the end, our decision provides customers easy access to needed security updates in a timely manner without sacrificing transparency."
In a separate post, Microsoft's Security Response Center's Mike Reavey said that the company will "deliver high-quality security updates for Windows Store apps as they become available. Providing security updates to Windows Store apps more frequently will allow us to add new functionality, fix issues and improve security".
"To ensure transparency, we will document all security updates for Windows Store apps in a security advisory, which we will revise with each new security update release. The security update process itself will be identical to that of any other Windows Store app update — customers will simply click on the store tile and select the update," he noted.
Today's Patch Tuesday updates are available on the usual channels, such as Windows and Microsoft Update, or through Windows Server Update Services.
The next round of monthly updates will arrive on April 9.