Microsoft fixes critical Windows, Office, IE security flaws

Microsoft has released its latest round security fixes in a massive Patch Tuesday update, with fixes for 57 known security vulnerabilities in total.
In 12 bulletins, five of the flaws are rated "critical," in which hackers and malware writers could remotely execute code on vulnerable machines, opening the doors up to malware attacks.
Read this
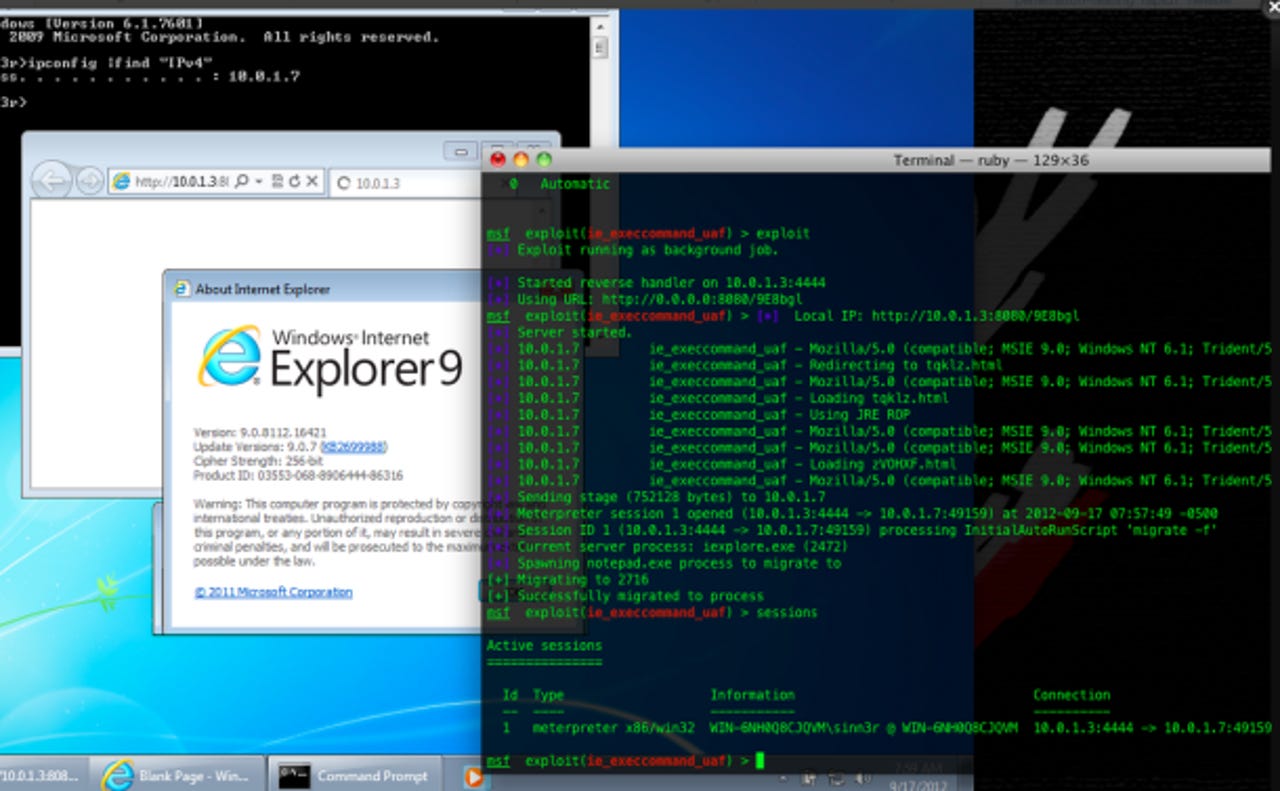
Two of the bulletins focus on all versions of Internet Explorer 6 and above—including IE7, IE8, IE9, and even IE10, which is only available for Windows 8 and Windows RT-powered devices, such as the Surface tablet.
For Windows 8 and Windows RT users, ZDNet's Mary Jo Foley explains that amid the security patches, a number of issues relating to Wi-Fi and "Connected Standby" have also been fixed.
In one bulletin, MS13-009, 13 flaws in total are patched, with one critical vulnerabilities fixed, which could have allowed hackers to gain access to a machine after visitors access a page laden with malware. Often the user doesn't even know that malware has been installed, but it could allow the hacker to access files and documents, and hijack the machine.
The second bulletin relating to Internet Explorer, MS13-010, fixes a vulnerability in an ActiveX library. Also rated critical, the flaw is being actively exploited in the wild, Microsoft said last week. The vulnerability lies in the Vector Markup Language (VML) library, which can be exploited if an unsuspecting user visits a malware-laden Web page.
Once versions of Internet Explorer are patched, they should become safe to use again—for now.
Another critical vulnerabilities found in Exchange Server, which could allow remote code execution through its WebReady document viewing service; another in Microsoft Office that could be exploited by a specially crafted media file; and one more fixes a critical bug in Windows Object Linking and Embedding (OLE), which could allow a hacker to access a machine with the same user permission rights.
The rest of the vulnerabilities are rated "important," but could also allow denial-of-service attacks and the elevation of user privileges.
Patch Tuesday fixes are available through the usual update channels, such as Windows Update, Microsoft Update, and Windows Server Update Services (WSUS).