Microsoft warns of unpatched Windows flaw

Microsoft said Tuesday that it is investigating reports of a Windows flaw with its graphics engine that would allow a hacker to run code as if he were a logged in user.
There are no attacks that Microsoft knows about, the company said.
Microsoft is investigating new public reports of vulnerability in the Windows Graphics Rendering Engine. An attacker who successfully exploited this vulnerability could run arbitrary code in the security context of the logged-on user. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights.
After its investigation, Microsoft will determine whether to patch with its regular cycle or an out-of-cycle update.
Microsoft said in a blog post:
To target this vulnerability, an attacker must convince a user to visit a specially crafted malicious Web page, or to open a malicious Word or PowerPoint file. Furthermore, users whose accounts are configured to have fewer user rights on the system would be less affected by an attack then those running with administrative rights. The Advisory includes further mitigations and workarounds to protect our customers.
A few key points:
- Windows XP, Server 2003, Vista and Windows Server 2008 with service pack 2 are affected.
- Windows 7 and Windows Server 2008 R2 aren't.
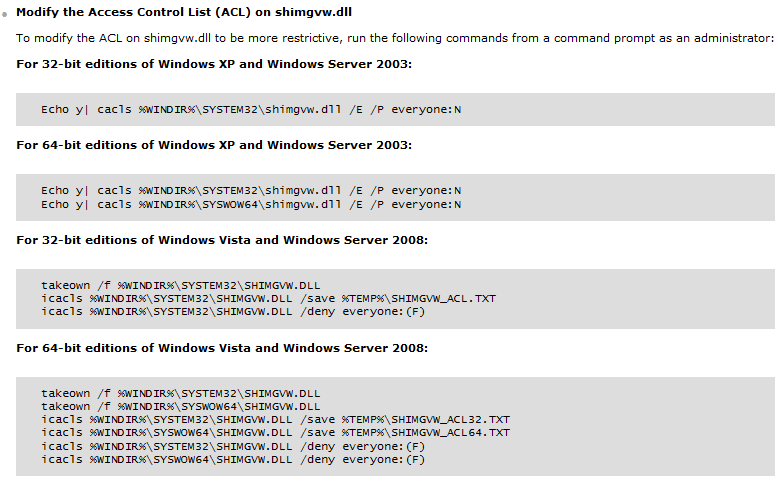
- And Microsoft has a workaround posted. Here are the directions: