Hackers built a 'master key' for millions of hotel rooms

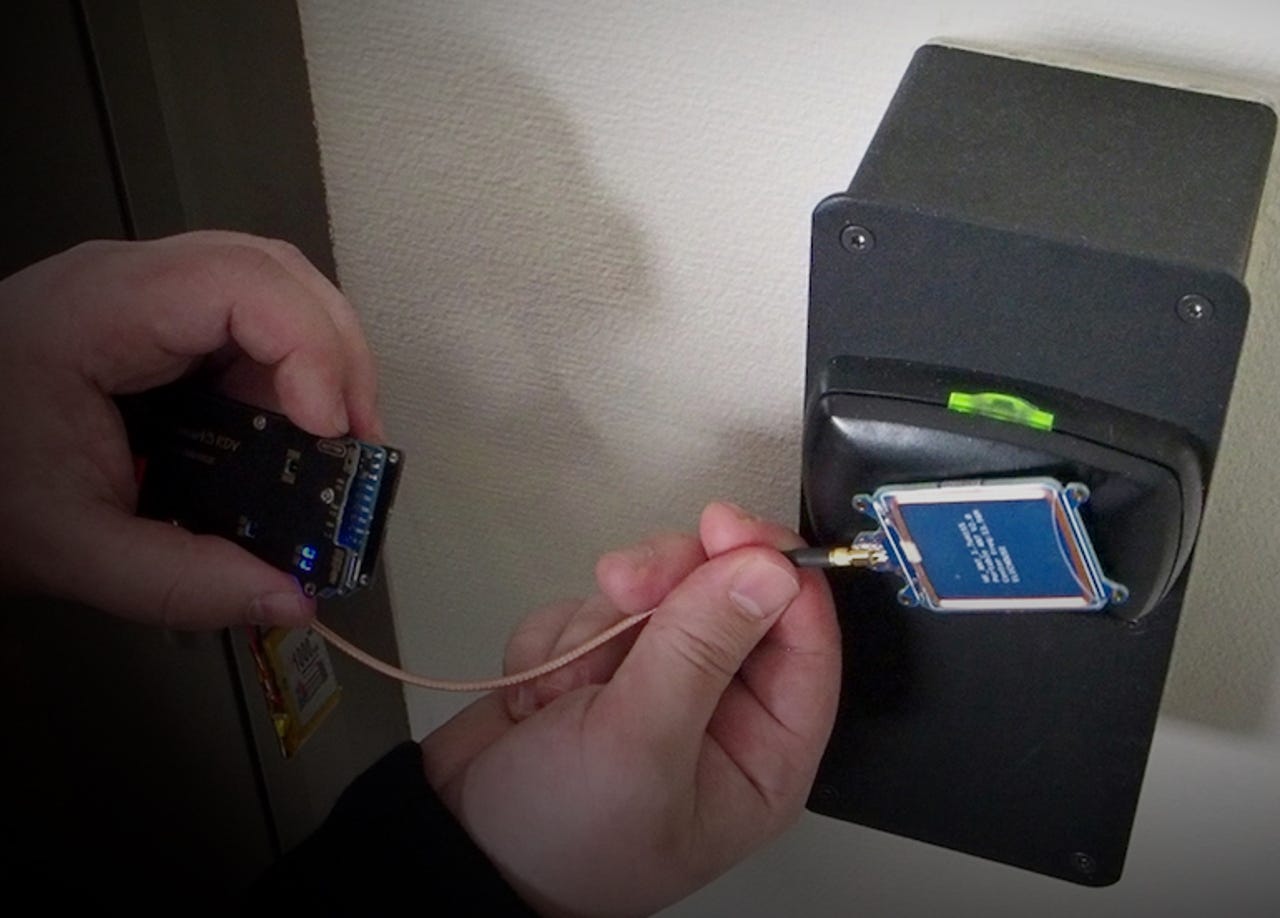
(Image: F-Secure/supplied)
Security researchers have built a master key that exploits a design flaw in a popular and widely used hotel electronic lock system, allowing unfettered access to every room in the building.
The electronic lock system, known as Vision by VingCard and built by Swedish lock manufacturer Assa Abloy, is used in more than 42,000 properties in 166 countries, amounting to millions of hotel rooms -- as well as garages and storage units.
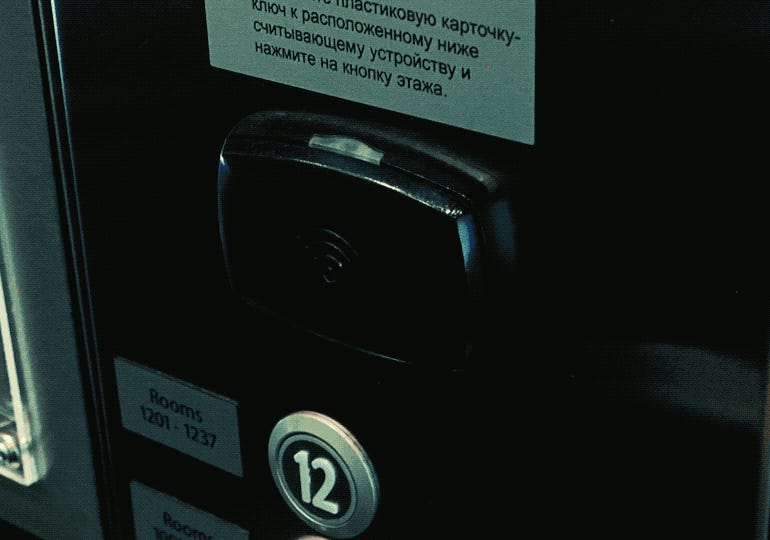
These electronic lock systems are commonplace in hotels, used by staff to provide granular controls over where a person can go in a hotel -- such as their room -- and even restricting the floor that the elevator stops at. And these keys can be wiped and reused when guests check-out.
It turns out these key cards aren't as secure as first thought.
F-Secure's Tomi Tuominen and Timo Hirvonen, who carried out the work, said they could create a master key "basically out of thin air."
Any key card will do. Even old and expired, or discarded keys retain enough residual data to be used in the attack. Using a handheld device running custom software, the researchers can steal data off of a key card -- either using wireless radio-frequency identification (RFID) or the magnetic stripe. That device then manipulates the stolen key data, which identifies the hotel, to produce an access token with the highest level of privileges, effectively serving as a master key to every room in the building.

This wasn't an overnight effort. It took the researchers over a decade of work to get here.
The researchers started their room key bypass efforts in 2003 when a colleague's laptop was stolen from a hotel room. With no sign of forced entry or unauthorized access to the room, the hotel staff are said to have dismissed the incident. The researchers set out to find a popular brand of smart lock to examine. In their words, finding and building the master key was far from easy, and took "several thousand hours of work" on an on-off basis, and using trial and error.
"Developing [the] attack took considerable amount of time and effort," said Tuominen and Hirvonen, in an email to ZDNet.
"We built a RFID demo environment in 2015 and were able to create our first master key for a real hotel in March 2017," they said. "If somebody was to do this full time, it would probably take considerably less time.
There was good news, the researchers said.
"We don't know of anyone else performing this particular attack in the wild right now," said the researchers, downplaying the risk to hotel customers.
Their discovery also prompted Assa Abloy to release a security patch to fix the flaws. According to their disclosure timeline, Assa Abloy was first told of the vulnerabilities a month later in April 2017, and met again over several months to fix the flaws.
The software is patched at the central server, but the firmware on each lock needs to be updated.
24 internet-connected things that really shouldn't be online
"This requires someone to be physically present at the lock," the researchers wrote.
But few details are available about the patch. A spokesperson for Assa Abloy did not return several emails and phone calls requesting comment. The company delivered the patch to customers in early 2018, but it's not known how many hotels have rolled out the fix.
Several major hotels, including the Waldorf Astoria in Berlin, the Grand Hyatt in San Francisco, and the Renaissance Downtown in Toronto, are said to be customers of the Swedish lock maker.
We reached out to representatives of Hyatt and Marriott but did not hear back by the time of publication.
A Hilton spokesperson said the company was "aware" of the vulnerabilities.
"The safety and security of our guests are of paramount importance. We are working closely with Ving to remediate impacted systems at a limited number of hotels," said the spokesperson.
The researchers urged buildings using the door locks to update as soon as possible.