Perimeter security: IT's Maginot Line

Information security is undergoing a revolution. Traditional perimeter defences and malware signature analysis are being rendered as obsolete as France's pre-World War II Maginot Line in the age of Blitzkrieg.
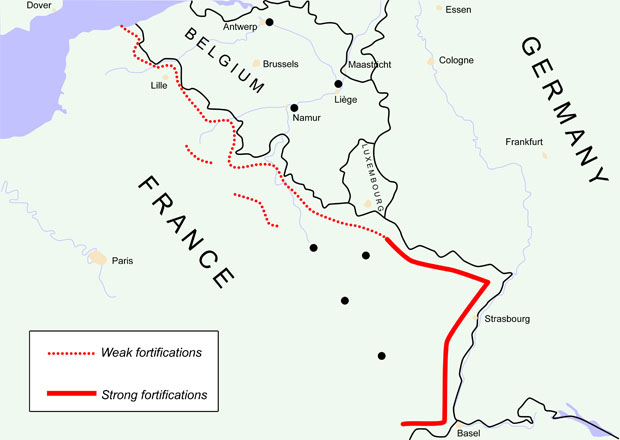
(Maginot Line image, by Niels Bosboom, CC3.0)
"It's very much Dad's Army protecting against the might of the German armed forces," Chris Wood, Sourcefire's regional director for Australia and New Zealand, told ZDNet Australia.
The Maginot Line was a massively complex and expensive series of fixed fortifications, built along France's eastern border in the 1930s to defend against German attack. But Germany's new Blitzkrieg tactics simply sent bombers and paratroopers over the top and tank divisions around the end, through Belgium, Luxembourg and the Netherlands. It happened fast, and was game over for France.
Similarly, network firewalls and traditional signature-based antivirus are fixed defences, designed to stop a frontal assault by known assailants.
But malware is now being parachuted into the network via bring-your-own-device (BYOD) policies or just on USB sticks. Employees are punching holes through the firewall, by setting up cloud services that are accessed through their web browsers. A network audit done six months ago is useless, when the network can be changed instantly, by anyone.
"Most organisations would have no idea what's going on across their networks," said Dr Paul Ashley, engineering manager at IBM Security Systems' Gold Coast facility, at a media briefing earlier this week. "It takes five minutes for me to download a BitTorrent application. All of a sudden, I'm streaming DVDs to my friend."
Wood agrees. "From my experience, the vast majority of organisations wouldn't have a clue what's running on their network," he said.
"There's a lot of information coming out about a disconnect — surveys, all that kind of stuff — between what the IT department believes is being used on their network and what it believes is being used to access corporate information, to what actually is being used by individuals," Wood said.
"An organisation can just go and give an infosec vendor a bucket load of money, and tick the box done, sorted ... That frustrates me, because organisations have to realise security is a process. It's a journey, not a destination."
Just as the network can now change instantly, so can the malware threats. Specific malware types are now typically used for just 20 minutes or less against a few targets, before they randomly morph into something else. Infosec vendors now have billions of malware signatures in their libraries, with a couple hundred thousand new ones arriving daily. It's impossible to transmit all those signature updates to every endpoint device.
Vendors are now switching to cloud-based services, where the endpoints report new files or network activity to some global intelligence system, for an assessment on whether it's malicious or benign.
Increasingly, those assessments are being made through behavioural analysis, based on what the file or network activity is doing, rather than what it looks like. Reputation analysis, where the same file or network activity being flagged as suspicious by different organisations, means it's more likely to be malicious.
To make all this work effectively, Wood said, you need to know what's happening in real time. "Not only what devices, but what applications, what traffic, who they're talking to, how much are they talking ... and it makes it increasingly more difficult when you have the proliferation of mobile devices and the power of those mobile devices."
You also need an accurate history of the network's past behaviour, to know whether today's events are part of an known pattern of safe behaviour or something new and suspicious. Security data must be kept for months, or even years. Activity might only be identified as a potential attack, because the outbound encrypted data channel being opened today is part of a trickle of data being sent to the same internet protocol (IP) address, from which a suspicious file was downloaded six months earlier.
While all the major vendors are touting their cloud-based solutions to face these new challenges, their approaches do differ.
Sourcefire's FireAMP malware protection system and its new FireAMP Mobile product for Android, to be released on 29 June, for example, not only monitor network traffic patterns, but also track every time individual files are moved, copied or opened, to spot unusual activity that could be a sign of data being exfiltrated.
If, for example, a confidential engineering schematic on the company's file server is being opened by a computer belonging to a salesperson, when, previously, it's only ever been opened by engineers, an alert can be raised — especially if that computer is also opening an encrypted communication channel to a foreign website.
This relatively new approach might even have prevented the newly-discovered Flame worm from operating undetected inside networks in Iran and elsewhere, for two years or more.
"I'm not going to say 'Yes, we would have found it'. I'm not going to be that presumptuous. But here's a piece of malware that's phoning home ... If you could have seen that traffic [in] real time, you could have noticed the change in the endpoints and how they were communicating, even if everything was encrypted," Wood said.
"You have to have more information about your network than the bad guys."
Meanwhile IBM has been focusing on the human element. Technology that went into development a year ago, to automatically identify the applications people are using by analysing their network traffic and controlling their activity to enforce organisational security policies, is now being deployed to customers as the QRadar Network Anomaly Detection appliance.
The appliance is integrated with the QRadar Security Intelligence Platform developed by Q1 Labs, which IBM acquired in October 2011.
QRadar can now identify around 400 applications and enforce granular control over their functionality.
"You might put a rule in that says we will allow you to go to those email-type services [like Google's Gmail], but we're only going to allow you to read your personal mail on there. Or, we may allow you to write, but we're not going to allow you to attach documents," Ashley said.
Similarly, Skype might be limited to text messaging only, with VoIP excluded because of its bandwidth cost, and file transfers banned to prevent exfiltration of corporate data.
"It allows a company to have a progressive social media policy, while still keeping control around the things they care about," said IBM's cloud security chief architect Neil Readshaw.
The days of just blocking things are over, Ashley said. "If you do that, all your Gen-Ys will just run out the door. You won't be able to keep them."
IBM has developed a "capability framework", as part of its structured approach to moving customers to more advanced network monitoring, data mining and other tools — though, not everything in its "capability framework" will be needed by every customer.
(Credit: IBM)
In this new model of big-data traffic analysis and active defence, the traditional network defences of perimeter firewalls and antivirus are still needed. But they are now the basics. It'll take time and effort for organisations to implement beyond those basics.
Stilgherrian travelled to a Gold Coast media briefing as IBM's guest.