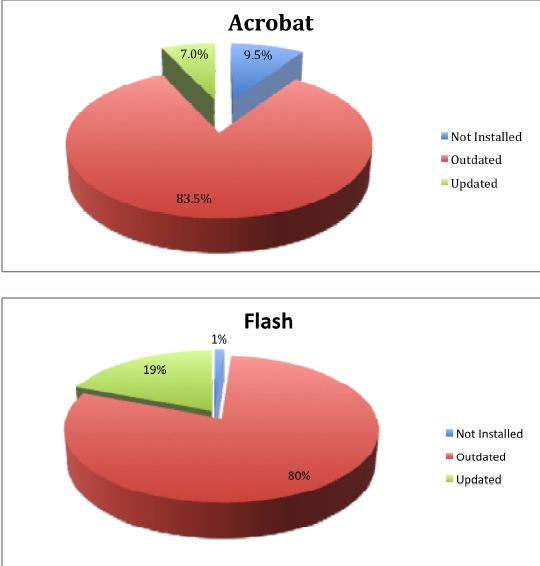
Research: 80% of Web users running unpatched versions of Flash/Acrobat
The company has also criticized Adobe by insisting that their update mechanism "does not meet the requirements of a system that is used by 99% of users on the Internet and is highly targeted by criminals", but is praising the update mechanism of Google's Chrome and Firefox, whose silent updates close the window of opportunity for malicious attackers to take advantage of.
Trusteer's research findings come a month after Secunia found out that Adobe is shipping an insecure version of Reader from its official site, justifying the action with the built-in updater, which apparently is not used by the 2.5 million users mentioned in the research, followed by an advice given in the SANS NewsBites newsletter, issue 61, that organizations should limit the use of Adobe products in order to minimize the attack surface.
Due to the high market penetration of Adobe's products, it's fairly logical to witness an increase of malicious exploitation of Adobe related vulnerabilities. However, there aren't any web malware exploitation kits in the wild that are exclusively relying on Adobe-specific vulnerabilities. Instead, the exploits-mix that is served upon successful browser recognition attempts to exploit the most common applications found on a particular PC in order to increase the probability of successful infection.
Data published by Secunia two months ago, indicates the same trend that cybercriminals have been aware of for a while now, namely, that the average insecure program per PC rate is still high, with 3 insecure programs in the U.S on average, and 4 insecure programs per PC in Europe based on the company's data. The company published similar findings two years, providing that an unpatched vulnerability is just as handy as a zero day one from the perspective of the cybercriminal who's efficiently infecting hundreds of thousands of users by exploiting outdated/unpatched flaws.
Adobe's products aren't an exception, they're targeted in between the rest of the vulnerabilities included in the exploits-mix. Don't just make sure that you're running the latest version of Flash and Reader, make sure that you're running the latest versions of all the applications on your PC, before cybercriminals do the check for you.