Researchers expose complex cyber espionage network
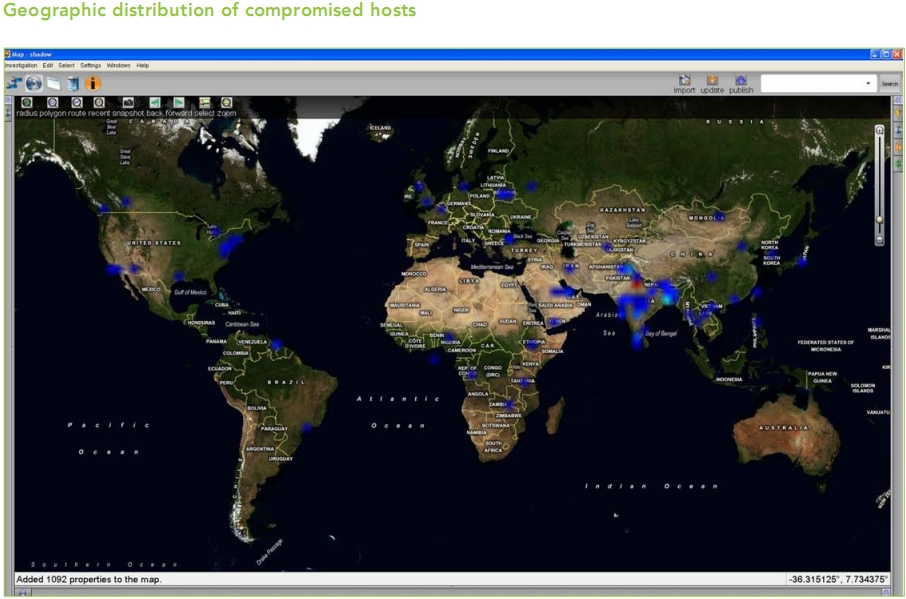
Security researchers from the Information Warfare Monitor (Citizen Lab and SecDev) and the ShadowServer Foundation, have released the findings from their eight month investigation, “Shadows in the Cloud”, detailing the inner workings of complex cyber espionage network that was systematically stealing sensitive documents/correspondence from the Indian government, the United Nations, as well as Dalai Lama's offices, from January to November 2009.
More details on attack vectors used, the command and control infrastructure, and the victim analysis based on the recovered documents, some of which are marked as SECRET, RESTRICTED and CONFIDENTIAL:
- Shadows in the Cloud documents a complex ecosystem of cyber espionage that systematically compromised government, business, academic, and other computer network systems in India, the Offices of the Dalai Lama, the United Nations, and several other countries. The report also contains an analysis of data which were stolen from politically sensitive targets and recovered during the course of the investigation. These include documents from the Offices of the Dalai Lama and agencies of the Indian national security establishment. Recovery and analysis of exfiltrated data, including one document that appears to be encrypted diplomatic correspondence, two documents marked “SECRET”, six as “RESTRICTED”, and five as “CONFIDENTIAL”. These documents are identified as belonging to the Indian government. However, we do not have direct evidence that they were stolen from Indian government computers and they may have been compromised as a result of being copied onto personal computers. The recovered documents also include 1,500 letters sent from the Dalai Lama’s office between January and November 2009. The profile of documents recovered suggests that the attackers targeted specific systems and profiles of users.
Just like the majority of targeted malware attacks, this one was also relying on client-side exploits (Report: Malicious PDF files comprised 80 percent of all exploits for 2009) served through different file types (PDF, PPT, DOC) using a relevant topic of interest to Indian and Tibetan communities, which were then spamvertised to the victims of interest.
What's particularly interesting about the cyber espionage facilitating network in question, is the mix of legitimate and purely malicious infrastructure in an attempt to not only increase the life cycle of the campaign, but also, to make it harder for network administrators to detect the malicious use of popular free email service providers, as well as social networks.
- During our investigation we found that such intermediaries included Twitter, Google Groups, Blogspot, Baidu Blogs, and blog.com. The attackers also used Yahoo! Mail accounts as a command and control component in order to send new malicious binaries to compromised computers. In total, we found three Twitter accounts, five Yahoo! Mail accounts, twelve Google Groups, eight Blogspot blogs, nine Baidu blogs, one Google Sites and sixteen blogs on blog.com that we being used as part of the attacker’s infrastructure. The attackers simply created accounts on these services and used them as a mechanism to update compromised computers with new command and control server information.
The practice of blending legitimate infrastructure into the malicious mix is nothing new. In fact, in 2009 cybercriminals continued demonstrating their interest in abusing legitimate services such as Twitter, Google Groups, Facebook as command and control servers, as well as Amazon’s EC2 as a backend.
The attack vector in question, is the client-side exploits serving embassy, with the following international embassies serving malware to their visitors over the past few years as an example of the trend:
- 2007 - Syrian Embassy in London Serving Malware
- 2007 - U.S Consulate in St. Petersburg Serving Malware
- 2008 - The Dutch Embassy in Moscow Serving Malware
- 2008 - Embassy of Brazil in India Compromised
- 2009 - Embassy of India in Spain Serving Malware
- 2009 - Ethiopian Embassy in Washington D.C Serving Malware
- 2009 - Embassy of Portugal in India Serving Malware
- 2009 - Azerbaijanian Embassies in Pakistan and Hungary Serving Malware
Who visits the web site of a particular embassy next to the people looking for information? It's the embassy staff itself, as well as other high-profile visitors. Therefore, a compromised web site of an embassy, which make in fact act as the weakest link in case it's insecure and open to exploitation compared to a failed targeted attack, could be on purposely used as an attack vector for a particular cyber espionage campaign.
The lines between cybercrime, and cyber espionage keep getting thinner, with financially-motivated cybercriminals today, in the best position to become information brokers of stolen high value data tomorrow, or even worse - set up the foundations for cyber espionage as a service propositions.