S. Korea, HK, Japan lead Web threat origins

South Korea, Hong Kong, and Japan are home to several cyberthreats such as spams, botnets, and servers hosting suspicious content.
According to the McAfee Threats Report: First Quarter 2013 released Monday, global spam levels were relatively stable in 2012 but registered a large increase in volume in the first quarter of 2013. E-mail spam volume climbed to 1.9 trillion in March 2013, almost twice that of December 2012.
The number of new spam URLs, or Web sites built for spamming purposes such as spam blogs or comment spam, also jumped from 30,000 the previous quarter to more than 45,000 in the first quarter, while new phishing URLs and associated domains fell after fourth-quarter's 50 percent increase.
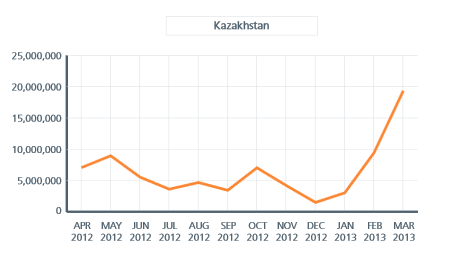
While most spam originated from the United States, South Korea ranked fourth in the top five in terms of growth rates where it saw an increase in spam e-mail of 54 percent. The other countries which made the list were Belarus which saw spam e-mail increase by 450 percent; Kazakstan at 150 percent; Ukraine at 58 percent; Peru at 41 percent.
Japan, at 420 percent, topped the global rank with the largest increase in the number of botnet senders.
Another Asian country, Hong Kong was one of the top three host countries for spam URLs and phishing URLs, behind the U.S. and Germany. In terms of countries hosting phishing URLs, though, Hong Kong ranked second.
Within the Asia-Pacific region, Hong Kong also housed the largest number of servers hosting malicious content, followed by China, South Korea, Japan, and India. Globally, Asia-Pacific ranked behind North America, and Europe and Middle East in terms of the number of locations from which servers hosting suspicious content originated.
According to Akamai's Third Quarter 2012 State of the Internet Report, released in January, South Korea, Hong Kong, and Japan ranked as the top three countries in terms of average connection speeds. However, the report also noted that more than half of the world's attack traffic originated from the Asia-Pacific region.
Rise of malware targeting data in enterprises, social media
According to the McAfee report, there was a 30 percent increase in master boot records (MBR) related malware and new instances of password-stealing Trojans repurposed to capture information on individuals and organizations beyond the financial sector.
It pointed to the Citadel Trojan as an example, which had been repurposed from a bank account threat to stealing personal information from targeted employees outside of the financial services industry.
Another social networking worm, Koobface, resurfaced with three times as many samples in the first quarter, which was a high point for the worm which targets Facebook, Twitter, among other social networking services. The worm was first discovered in 2008 and had seen relatively flat growth last year, reaffirming the cybercrime community's belief that social network users provided a very target-rich environment as potential victims, the report noted.
"The resurrection of Koobface reminds us that social networks continue to present a substantial opportunity for intercepting personal information," Vincent Weafer, senior vice president of McAfee Labs, said in a statement. "Within the enterprise, we see password-stealing Trojans evolving to become information-gathering tools for cyberespionage attacks."
"Whether they target login credentials or intellectual property and trade secrets, highly-targeted attacks are achieving new levels of sophistication," Weafer added.