S. Korea tops Asia's malware infection list

South Korea, for all its IT maturity and high broadband penetration rate, continues to be plagued by malware, particularly Trojans and adware. It topped the list among Asian countries in having the highest malware infection rate, according to a Microsoft study.
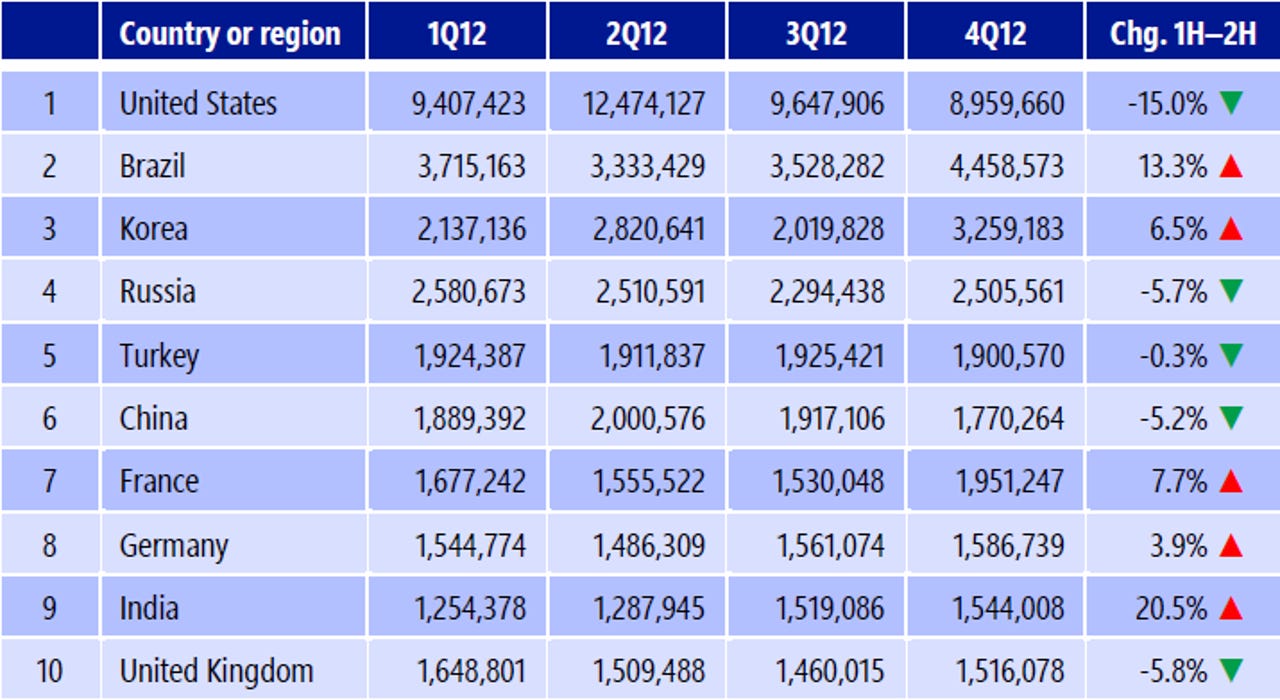
The recently-released Microsoft Security Intelligence Report Volume 14 (SIRv 14) showed that South Korea had the third-highest number of computers reporting detections and removals by Microsoft desktop anti-malware tools globally, and was top among other Asian markets. Some 5.28 million computers in the country detected and removed malware during the second half of 2012, behind the United States and Brazil, it stated.
Commenting on the findings, Tim Rains, director of product management at Microsoft's Trustworthy Computing, told ZDNet Asia in an interview Monday the high number of malware infections in South Korea is "rather interesting.
This is because countries with high broadband penetration rate tend to have lower malware infections as the broadband routers act as firewalls to prevent such viruses, he pointed out.
"Even though South Korea has strong broadband penetration and great public-private partnerships combating security similar to Japan, which has the lowest number of detection and removal of malware, it still has one of the highest malware infection rates in the world," Rains observed.
He added two particular threats continue to plague the country--miscellaneous Trojans and adware. In fact, 75 percent of computers studied for the survey reported detection of Trojans while 31 percent reported adware presence in the machine.
These Trojans are threats that purport to be one thing, such as security software, in order to infect unsuspecting users, Rains explained. This attack method is becoming popular among attackers in South Korea, who had been known to Trojan Downloaders and Droppers or other threats that can sneak into users' systems without their knowledge, he added.
Besides South Korea, two other Asian countries also made it to the top 10. China took sixth spot with 3.69 million computers, while India came in at ninth spot with 3.06 million computers, the study showed.
Microsoft analyzed online threats between July and December 2012, from more than a billion systems in over 100 countries worldwide. The SIRv14 was first released on April 18, 2013.
Malaysia highest concentration of phishing sites
Another Asian market, Malaysia, had the distinction of having the highest concentration of phishing sites. Where the global average was 5.10 phishing sites per 1,000 host computers, Malaysia had 17.66 for the same number of hosts.
Additionally, Malaysia's malware hosting sites and drive-by download were also above the global average. According to the report, Malaysia had 13.87 malware hosting sites per 1,000 hosts, compared to the worldwide average of 10.85, and 0.95 drive-by download per 1,000 URLs, which is above the global average of 0.33.
Rains said these above average findings could be due to the country's relatively good Wi-Fi, broadband, 3G and 4G connectivity in Malaysia compared to other markets in the regions, which enables Web-based attacks to be more effective.
Since phishing also requires compromised servers to conduct the attack, it could be the country has more such servers than others in this part of the world, he added.
Its neighbors Singapore and Hong Kong, too, had above average numbers when it comes to phishing sites at 5.98 and 6.23, respectively. This is down to both cities being banking and financial centers, which would naturally attract attention from cybercriminals and push their numbers above the global average, the Redmond executive explained.
Conficker sightings fall
The latest edition of the Microsoft study also showed the proportion of Conficker threats reported by enteprise computers has fell by 37 percent from 2011 to the second half of 2012.
By contrast, last year's findings showed Conficker as the biggest cybersecurity threat to businesses and was found on 1.7 million systems in the fourth quarter of 2011 alone.
Rains said it was "about time the Conficker died down", explaining the worm, first detected in November 2008, steals administrative passwords and uses these to log on to every other machine in the network, thereafter compromising these machines. It spreads mainly through unpatched vulnerabilities, autorun feature abuse and weak passwords, he added.
However, after five years, enterprises have fixed their patches, rolled out security updates and improved the use of passwords so it makes sense the Conficker worm is finding it more difficult to spread, he said.