Sophisticated, 'potent' trojan targets online bank users

Yet another sophisticated trojan is targeting online users to steal valuable financial data.
On Thursday, Robert Lipovsky from We Live Security documented the discovery of Win32/Spy.Hesperbot, a new and effective banking trojan which uses "credible-looking phishing-like campaigns related to trustworthy organizations" to dupe victims into running the malware on their systems.
In a blog post, Lipovsky explains that Hesperbot was discovered on a domain passing itself off as part of the Czech Postal Service.
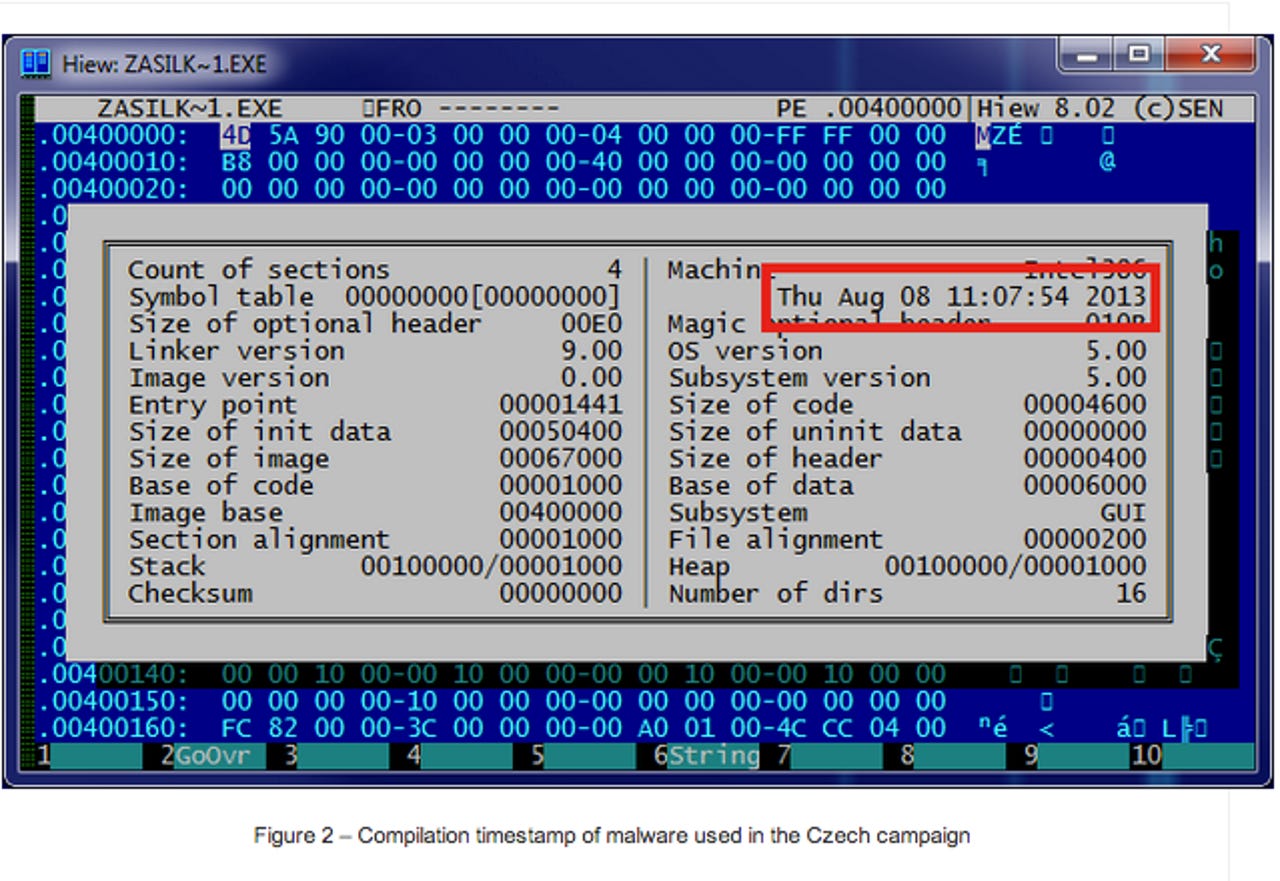
The campaign began on August 8 this year. After the domain ceskaposta.net was registered, phishing emails were sent in attempts to pass off as postal service invoices. The link in the email showed the legitimate ceskaposta.cz while pointing to the malicious domain, and the trojan is then downloaded as an executable file from the fake website.
The security team's analysis revealed that the banking trojan has similar functionality and goals to well-known malware Zeus and SpyEye. However, the team says that there are "significant implementation differences," which "indicated that this is a new malware family, not a variant of a previously known trojan."
The trojan has a number of common attack functionalities, including keystroke logging, screenshot creation and video capture. Hesperbot is also able to set up a remote proxy and create a hidden VNC server on the infected system. It is this factor which makes the malware so advanced -- by creating a VNC server hidden from the victim's notice, Hesperbot creates a graphical desktop sharing system which lets attackers remotely control the computer and transmits keyboard and mouse activity.
Hesperbot can also intercept network traffic and inject HTML with malicious code.
Debugging data was sent back to the command and control center, which suggests the malware is still in the early stages of development.
Turkish online bank users have faced this campaign for a while now, and Portugal's variation passes itself off as Portugal Telecom. While not present in the Czech phishing campaign, the Turkish and Portuguese attacks also include web injections which insert into bank web-pages when viewed on the infected PC.
"In the course of our research, we also stumbled upon an additional component used by Win32/Spy.Hesperbot," the researchers say. "This malware, detected by ESET as Win32/Spy.Agent.OEC, harvests e-mail addresses from the infected system and sends them to a remote server. It is possible that these collected addresses were also targeted by the malware-spreading campaigns."
The aim of the attackers is to obtain login credentials giving access to the victim's bank account and to get them to install a mobile component of the malware on their Symbian, Blackberry or Android smartphones. Hesperbot tends to target online banking users in Turkey, the Czech Republic, Portugal and the United Kingdom.